POC Crew
[#POC2026] CFT 👈 WANTED
We’re looking for deep, practical, hands-on trainings from you
Exploit development, browser, kernel, AI security — surprise us.
CFT deadline: 26th June
More info: https://t.co/d94HoJc4hy
We’re looking for deep, practical, hands-on trainings from you
Exploit development, browser, kernel, AI security — surprise us.
CFT deadline: 26th June
More info: https://t.co/d94HoJc4hy

[#POC2026 NOTICE]
Your offensive conference is BACK again in its shape!
and POC2026 begins in a new home.
⏰ Date: November 12–13
📍 New Venue: The Westin Seoul Parnas, Korea 🇰🇷
👨🏫 CFT: June 1 – June 26
🎙️ CFP: June 1 – September 30
🎟️ Registration: September 1 – October 31
Your offensive conference is BACK again in its shape!
and POC2026 begins in a new home.
⏰ Date: November 12–13
📍 New Venue: The Westin Seoul Parnas, Korea 🇰🇷
👨🏫 CFT: June 1 – June 26
🎙️ CFP: June 1 – September 30
🎟️ Registration: September 1 – October 31

Great time in OffensiveCon2026
The talks were high quality, P2O was exciting, and the few surprises throughout the event made it even better!
And of course catching up with old & new friends is always a thing - the true Power Of Community!
Safe flight y'all🙌
The talks were high quality, P2O was exciting, and the few surprises throughout the event made it even better!
And of course catching up with old & new friends is always a thing - the true Power Of Community!
Safe flight y'all🙌


Off to Berlin for @offensive_con!
Great research deserves great conversations and the best ones usually happen after the talks:)
We are bringing the booze to the foyer: whisky, premium soju, and a few surprises from tomorrow, pouring for 4 days straight.
AI may win at speed,
Great research deserves great conversations and the best ones usually happen after the talks:)
We are bringing the booze to the foyer: whisky, premium soju, and a few surprises from tomorrow, pouring for 4 days straight.
AI may win at speed,
#Zer0Con2026, a wrap up!
Big thanks to our speakers, sponsors, participants, and staff members for making this incredible journey with us.
Special appreciation to those who joined from a far despite ongoing global situation, we truly appreciate your effort coming all this way.
Big thanks to our speakers, sponsors, participants, and staff members for making this incredible journey with us.
Special appreciation to those who joined from a far despite ongoing global situation, we truly appreciate your effort coming all this way.




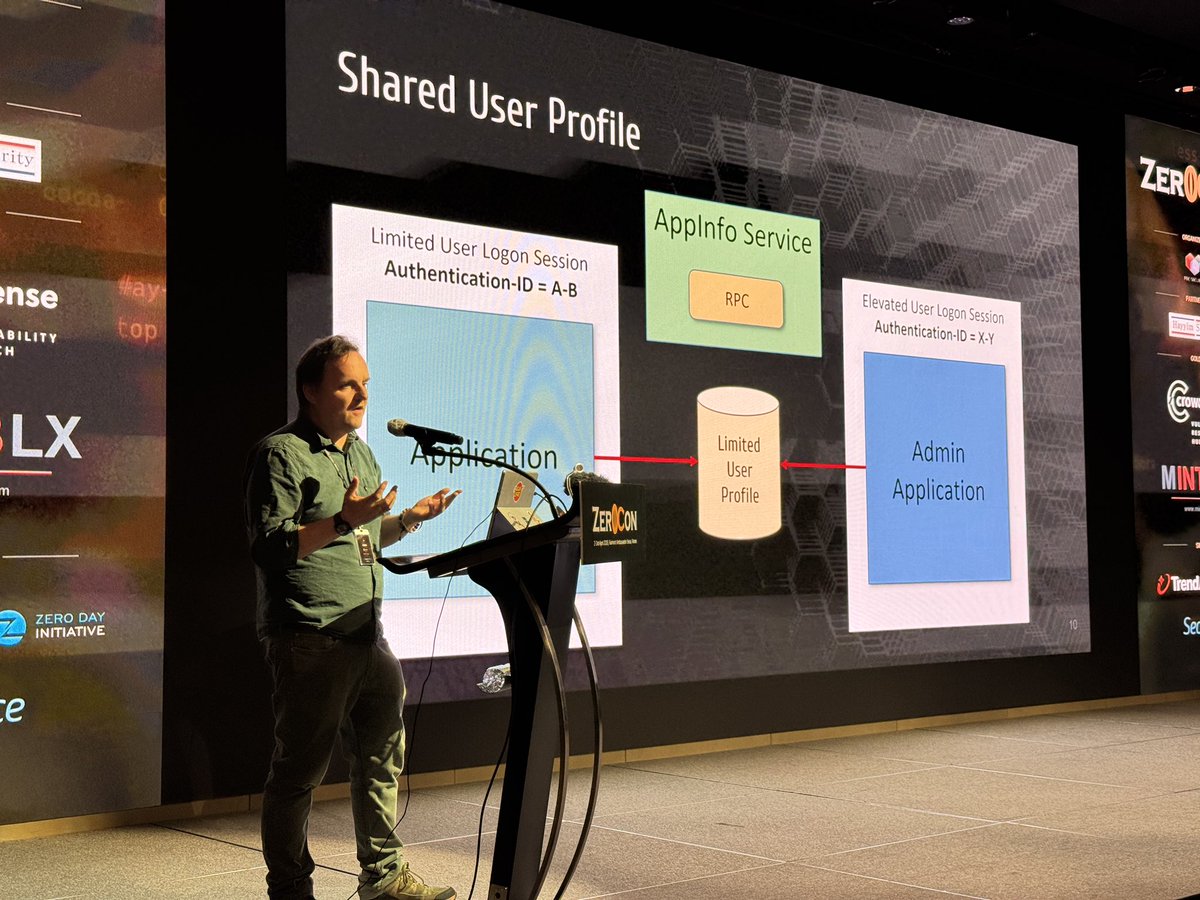
🐼 James Forshaw(@tiraniddo) - Protecting your Administrator and Other Friends
🔥 Ye Zhang(@VAR10CK) - Attacking Apple Display Co-Processor

🤖Georgi G(@munmap) & Ben R(@XploitBengineer) - Promp2Pwn – LLMs Winning at Pwn2Own
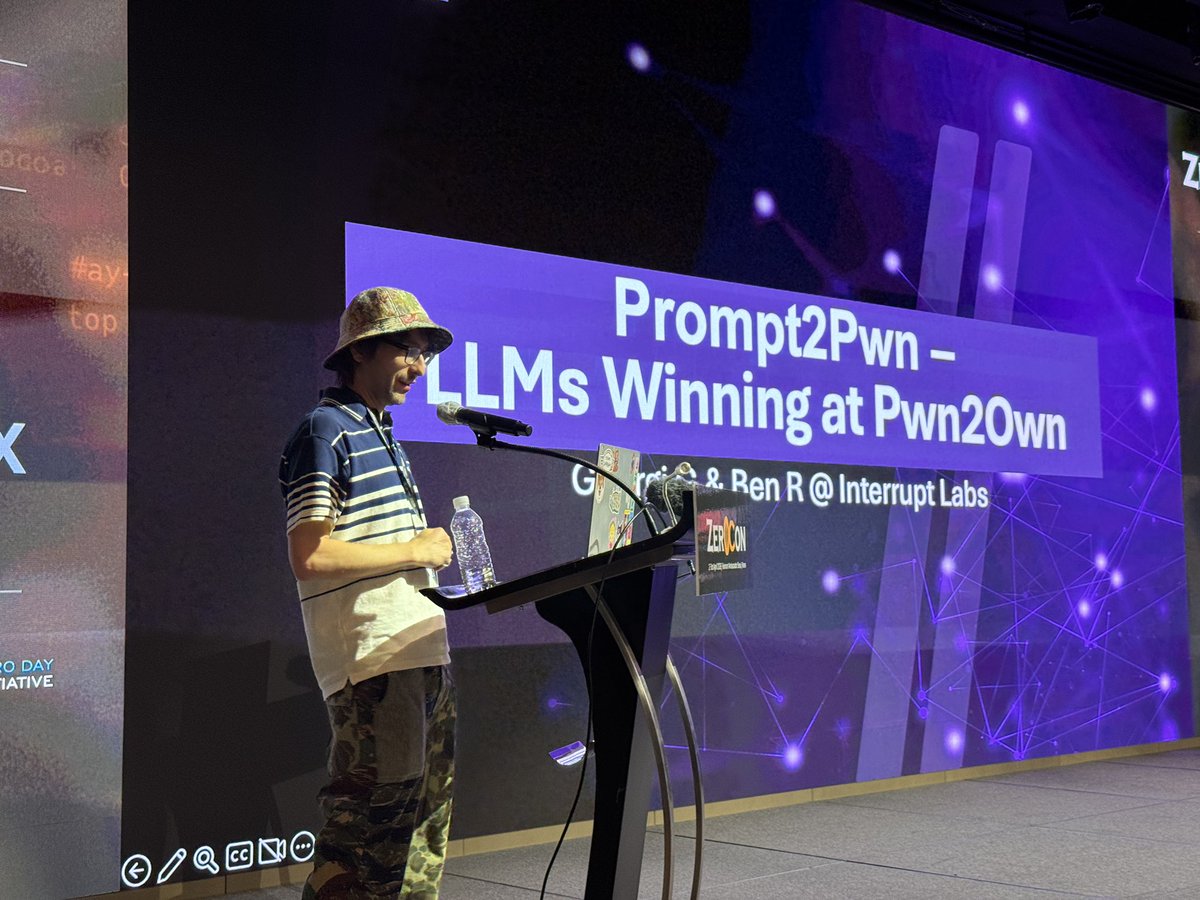
His first time in Korea 🇰🇷
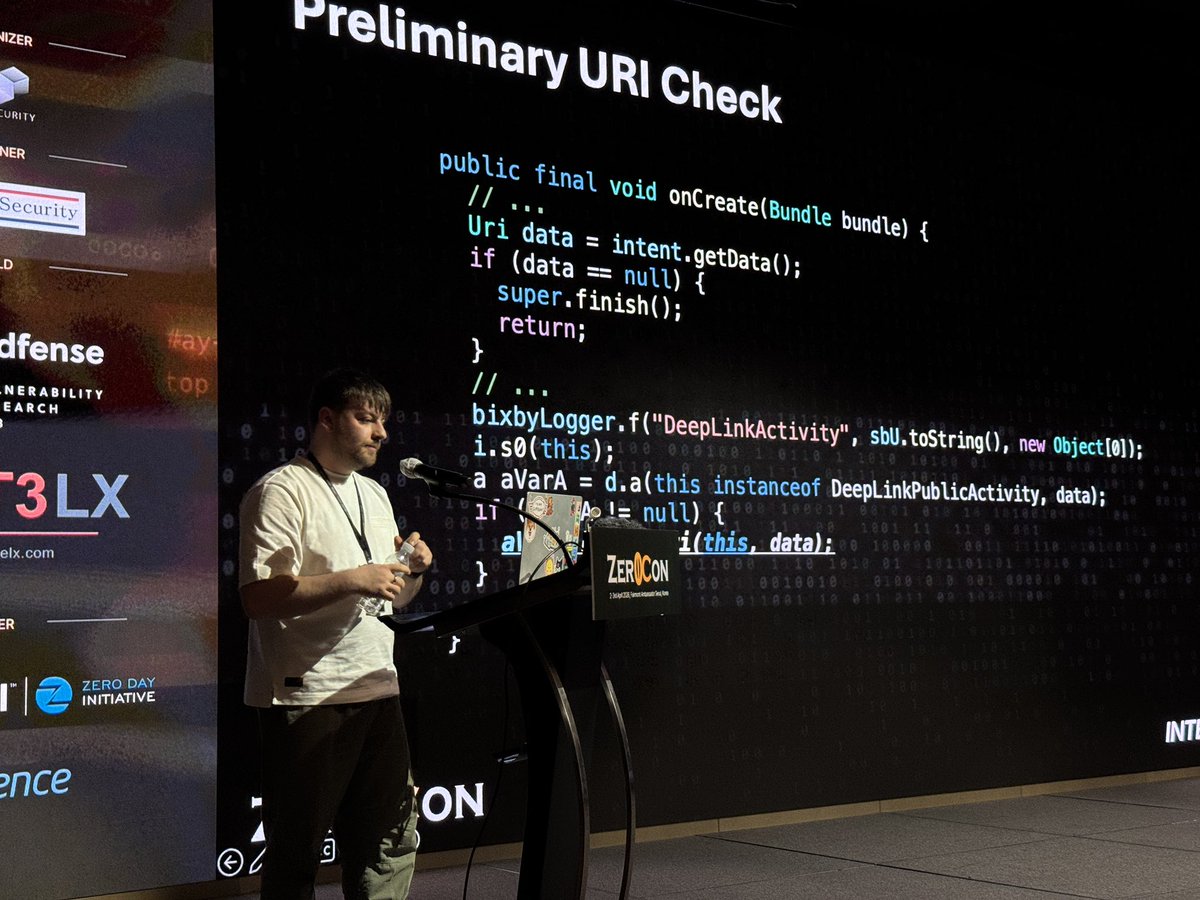
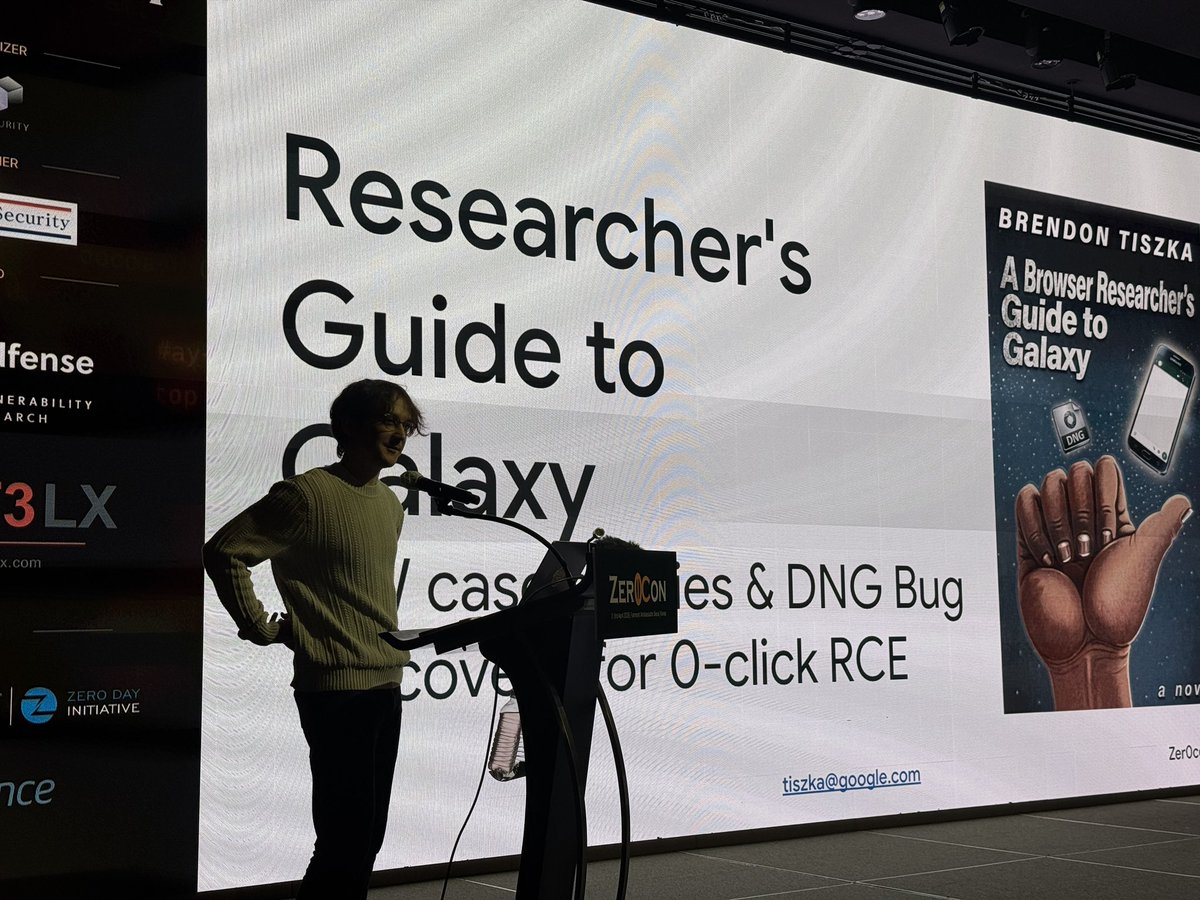
Brendon Tiszka - Researcher's Guide to the Galaxy: Digging into Samsung 0-click, Android Messengers, DNG, and other image formats
Brendon Tiszka - Researcher's Guide to the Galaxy: Digging into Samsung 0-click, Android Messengers, DNG, and other image formats
Day2 start!! 👤 Anonymous Researcher - Web Security Still Has Secrets — And They're Dangerous

👍 Mathieu Farrell(@Coiffeur0x90) - Breaking the Backbone of Global ISP Networks

Enjoy 🥂 #Zer0Con2026

☄️ Vatafu Vladut(@f00fc7c800) - From inside with love: using uninitialized kernel memory to achieve cross container infoleak

🍎 Csaba Fitzl(@theevilbit) & Gergely Kalman(@gergely_kalman) - Kalman macOS Exploit Mixtape – Hack Like it's the 80s


🎃Chih-Yen Chang(@u1f383) - Modern Android Kernel Exploitation Through a Mali Driver Vulnerability

🤟 We are now start!
Lachlan Davidson - Discovering React2Shell and Unleashing the New Age of JavaScript Exploits
Lachlan Davidson - Discovering React2Shell and Unleashing the New Age of JavaScript Exploits


All three Zer0Con trainings have successfully kicked off.🥸
Wishing everyone an engaging and productive three days ahead.💫
#Zer0Con2026
Wishing everyone an engaging and productive three days ahead.💫
#Zer0Con2026




😉 Thank you for sponsoring #Zer0Con2026
MintelX (@mintelx_lab) is a security research and exploit acquisition company. We’re proud to sponsor Zer0Con and support the global security research community.
MintelX (@mintelx_lab) is a security research and exploit acquisition company. We’re proud to sponsor Zer0Con and support the global security research community.

🔥 Thank you for sponsoring #Zer0Con2026
Not all n-days are created equal. Crowdfense's(@crowdfense ) N-Day Vulnerability Feed gives you real-world weaponised vetted exploits and technical analysis for the high-risk CVEs actively abused in the wild. Research-grade intelligence,
Not all n-days are created equal. Crowdfense's(@crowdfense ) N-Day Vulnerability Feed gives you real-world weaponised vetted exploits and technical analysis for the high-risk CVEs actively abused in the wild. Research-grade intelligence,

Thank you for sponsoring #Zer0Con2026
TrendAI ZDI(@thezdi) is driving the future of AI-powered security - identifying vulnerabilities, enabling responsible disclosure, and helping build a safer ecosystem. ZDI remains a standout example of that mission in action.
TrendAI ZDI(@thezdi) is driving the future of AI-powered security - identifying vulnerabilities, enabling responsible disclosure, and helping build a safer ecosystem. ZDI remains a standout example of that mission in action.
Thank you for sponsoring #Zer0Con2026
We at Secfence(@secfence) are hiring world class researchers! If you think you fit the bill - reach out to us at zer0con@secfence.com.
We are also acquiring bugs with top payouts.
Reach out to us at - vr@secfence.com
We at Secfence(@secfence) are hiring world class researchers! If you think you fit the bill - reach out to us at zer0con@secfence.com.
We are also acquiring bugs with top payouts.
Reach out to us at - vr@secfence.com

#Zer0Con2026 Training will close at 23:59 on March 26 (KST).
If the training gets full before then, it might close earlier.
Cheers! 😎
For more: https://t.co/15bGQDgjGc
If the training gets full before then, it might close earlier.
Cheers! 😎
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 All speakers are now officially announced.
• Ticket registration is expected to close soon due to limited capacity.
• Training sessions are still open for registration.
If you’re coming to Zer0Con, take the opportunity to gain knowledge, meet great people, and
• Ticket registration is expected to close soon due to limited capacity.
• Training sessions are still open for registration.
If you’re coming to Zer0Con, take the opportunity to gain knowledge, meet great people, and
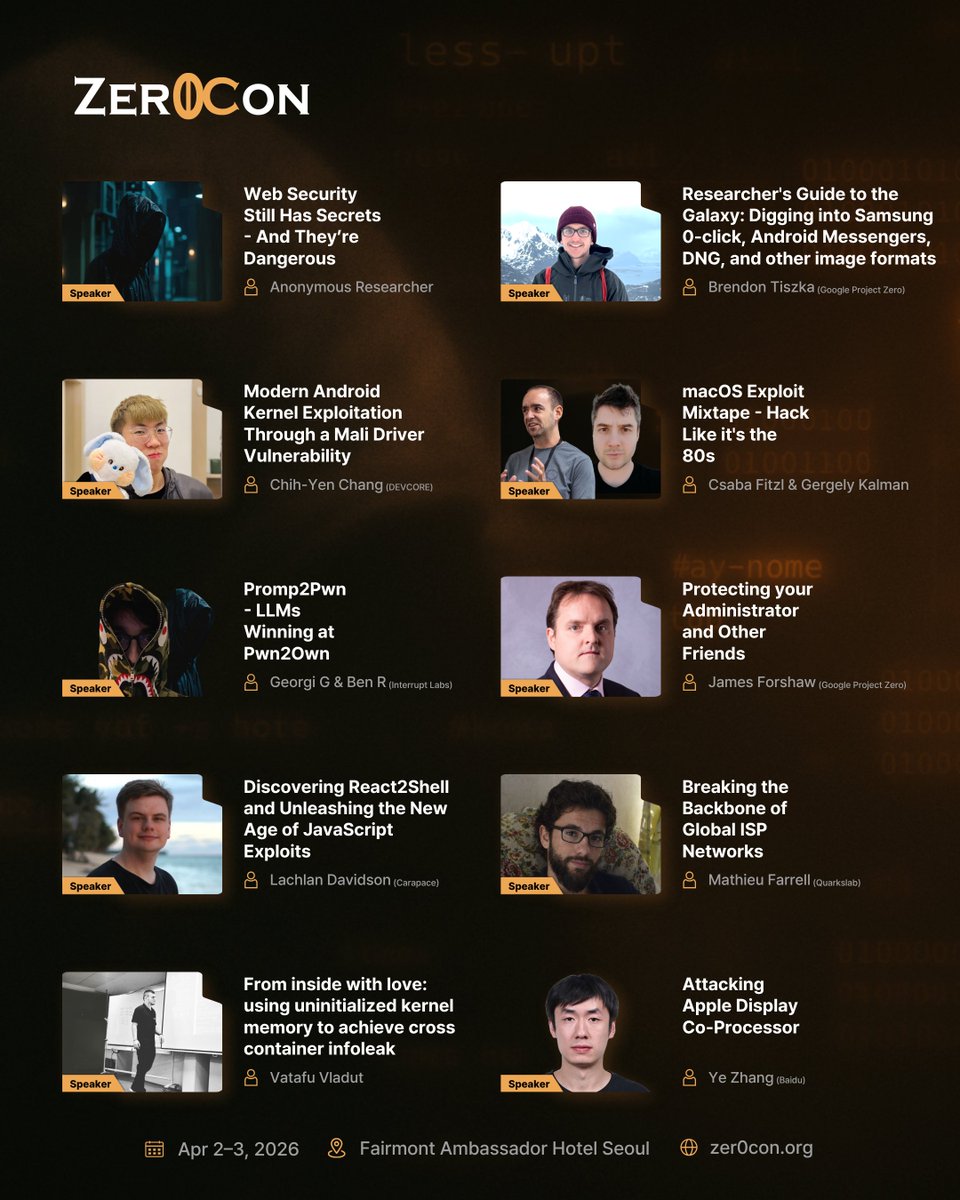
#Zer0Con2026 - SPEAKER 🤖
Georgi G(@munmap) & Ben R(@XploitBengineer) from Interrupt Labs - “Promp2Pwn - LLMs Winning at Pwn2Own”
For more: https://t.co/15bGQDgjGc
Georgi G(@munmap) & Ben R(@XploitBengineer) from Interrupt Labs - “Promp2Pwn - LLMs Winning at Pwn2Own”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 🌐
Mathieu Farrell(@Coiffeur0x90) from Quarkslab - “Breaking the Backbone of Global ISP Networks”
For more: https://t.co/15bGQDgjGc
Mathieu Farrell(@Coiffeur0x90) from Quarkslab - “Breaking the Backbone of Global ISP Networks”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 🍎
Ye Zhang(@VAR10CK) from Baidu - “Attacking Apple Display Co-Processor”
For more: https://t.co/15bGQDgjGc
Ye Zhang(@VAR10CK) from Baidu - “Attacking Apple Display Co-Processor”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 🧠
Vatafu Vladut(@f00fc7c800) - “From inside with love: using uninitialized kernel memory to achieve cross container infoleak”
For more: https://t.co/15bGQDgjGc
Vatafu Vladut(@f00fc7c800) - “From inside with love: using uninitialized kernel memory to achieve cross container infoleak”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER ⚛️
Lachlan Davidson from Carapace - “Discovering React2Shell and Unleashing the New Age of JavaScript Exploits”
For more: https://t.co/15bGQDgjGc
Lachlan Davidson from Carapace - “Discovering React2Shell and Unleashing the New Age of JavaScript Exploits”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 🛡️
James Forshaw(@tiraniddo) from Google Project Zero - “Protecting your Administrator and Other Friends”
For more: https://t.co/15bGQDgjGc
James Forshaw(@tiraniddo) from Google Project Zero - “Protecting your Administrator and Other Friends”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 🌌
Brendon Tiszka from Google Project Zero - “Researcher’s Guide to the Galaxy: Digging into Samsung 0-click, Android Messengers, DNG, and other image formats”
For more: https://t.co/15bGQDgjGc
Brendon Tiszka from Google Project Zero - “Researcher’s Guide to the Galaxy: Digging into Samsung 0-click, Android Messengers, DNG, and other image formats”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 🕶️
Anonymous Researcher - “Web Security Still Has Secrets - And They’re Dangerous”
For more: https://t.co/15bGQDgjGc
Anonymous Researcher - “Web Security Still Has Secrets - And They’re Dangerous”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 🎃
Pumpkin Chang(@u1f383) from DEVCORE - “Modern Android Kernel Exploitation Through a Mali Driver Vulnerability”
For more: https://t.co/15bGQDgjGc
Pumpkin Chang(@u1f383) from DEVCORE - “Modern Android Kernel Exploitation Through a Mali Driver Vulnerability”
For more: https://t.co/15bGQDgjGc

#Zer0Con2026 - SPEAKER 💾
Csaba Fitzl(@theevilbit) & Gergely Kalman(@gergely_kalman) - “macOS Exploit Mixtape - Hack Like it’s the 80s”
For more: https://t.co/15bGQDgjGc
Csaba Fitzl(@theevilbit) & Gergely Kalman(@gergely_kalman) - “macOS Exploit Mixtape - Hack Like it’s the 80s”
For more: https://t.co/15bGQDgjGc

[#Zer0Con2026]
💥 CFP "D-3"
🗓️ CFP: ~ Feb 22, 2026
Take the stage.
💥 CFP "D-3"
🗓️ CFP: ~ Feb 22, 2026
Take the stage.
[Zer0Con2026] TRAINING
All three trainings are Confirmed & Scheduled ✅
• Date: 30th Mar ~ 1st April 2026 (3 DAYS)
• Fairmont Ambassador Seoul, South Korea
The door stays open for latebirds... but try not to be the last one flying in.
Sign up: https://t.co/6cUC0ODFXm
All three trainings are Confirmed & Scheduled ✅
• Date: 30th Mar ~ 1st April 2026 (3 DAYS)
• Fairmont Ambassador Seoul, South Korea
The door stays open for latebirds... but try not to be the last one flying in.
Sign up: https://t.co/6cUC0ODFXm



[Zer0Con2026] TRAINING
"MalOpSec 2 -> EDR: The Great Escape"
by @DrCh40s & @t0nvi
🗓️Date: 30th Mar ~ 1st April 2026 (3 DAYS)
📌Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/6cUC0ODFXm
#Zer0Con2026
"MalOpSec 2 -> EDR: The Great Escape"
by @DrCh40s & @t0nvi
🗓️Date: 30th Mar ~ 1st April 2026 (3 DAYS)
📌Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/6cUC0ODFXm
#Zer0Con2026

[#Zer0Con2026] Registration is open for Zer0Con 2026.
📍 Fairmont Ambassador Hotel Seoul
🗓 April 2-3, 2026
🎟 Limited to 120 seats
🔗 https://t.co/15bGQDgjGc
📍 Fairmont Ambassador Hotel Seoul
🗓 April 2-3, 2026
🎟 Limited to 120 seats
🔗 https://t.co/15bGQDgjGc

[#Zer0Con2026]
🗓️ CFP closes in "30 days"
🌕 CFP: ~ Feb 22, 2026
No hesitation. Only execution ;)
🗓️ CFP closes in "30 days"
🌕 CFP: ~ Feb 22, 2026
No hesitation. Only execution ;)

We are heading back to Korea with wonderful memories from Barcelona. We would like to thank @__x86 💙 @epsilon_sec for giving us such great time. #OffensiveBCN


[Zer0Con2026] TRAINING
"macOS Vulnerability Research Training"
by @theevilbit & @gergely_kalman
🗓️Date: 30th Mar ~ 1st April 2026 (3 DAYS)
📌Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/6cUC0ODFXm
#Zer0Con2026
"macOS Vulnerability Research Training"
by @theevilbit & @gergely_kalman
🗓️Date: 30th Mar ~ 1st April 2026 (3 DAYS)
📌Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/6cUC0ODFXm
#Zer0Con2026

[Zer0Con2026] TRAINING
“Exploiting the Android Kernel"
by @andreyknvl
🗓️Date: 30th Mar ~ 1st April 2026 (3 DAYS)
📌Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/6cUC0ODFXm
#Zer0Con2026
“Exploiting the Android Kernel"
by @andreyknvl
🗓️Date: 30th Mar ~ 1st April 2026 (3 DAYS)
📌Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/6cUC0ODFXm
#Zer0Con2026

Wish you a blast year ahead.
Grateful for the past, ready for what’s next!
HAPPY NEW YEAR EVERYONE🙌
Grateful for the past, ready for what’s next!
HAPPY NEW YEAR EVERYONE🙌
[#Zer0Con2026] Announcements
Zer0Con2026 CFP / CFT is officially "OPENED"
🔒Date: April 2~3, 2026
🏨Venue: Fairmont Ambassador Seoul, South Korea
🌕CFT: ~ Jan 1, 2026
🌕CFP: ~ Feb 22, 2026
🌕Sponsor: ~ Feb 28, 2026
For more: https://t.co/61Vh1ld9pM
Zer0Con2026 CFP / CFT is officially "OPENED"
🔒Date: April 2~3, 2026
🏨Venue: Fairmont Ambassador Seoul, South Korea
🌕CFT: ~ Jan 1, 2026
🌕CFP: ~ Feb 22, 2026
🌕Sponsor: ~ Feb 28, 2026
For more: https://t.co/61Vh1ld9pM

[POC2025] Talks are now UP ONLINE!
Talks from #POC2025 are now publicly available on YouTube!
Enjoy the sessions - see you again at POC2026!
Talks from #POC2025 are now publicly available on YouTube!
Enjoy the sessions - see you again at POC2026!
#POC2025 Slides are up NOW!
Those slides currently in private and will be uploaded later by the speakers 😆
Those slides currently in private and will be uploaded later by the speakers 😆
Thank you so much for being with us at POC2025 ✨
Your time and presence truly meant a lot 🙏
Hope to meet you all again next year! 💫
Wishing everyone a safe and restful flight home ✈️💙
#POC2025
Your time and presence truly meant a lot 🙏
Hope to meet you all again next year! 💫
Wishing everyone a safe and restful flight home ✈️💙
#POC2025




The Drinking Hell trophy was lifted by Si*** 🏆
We sincerely hope that everyone who challenged him still managed to catch their flights on time. 🫡 ✈️
#POC2025
We sincerely hope that everyone who challenged him still managed to catch their flights on time. 🫡 ✈️
#POC2025


Huge thanks to @SAFATeamApS and @prdgmshift for sponsoring our Closing party, The ENDS!
Your support didn’t just level up the event — it made the whole night unforgettable.
Appreciate you both for bringing the energy, the vibe, and the magic. ✨
#POC2025
Your support didn’t just level up the event — it made the whole night unforgettable.
Appreciate you both for bringing the energy, the vibe, and the magic. ✨
#POC2025




Such a fun vibe 😄
Bocheng Xiang (@crispr_x) & HeeChan Kim (@heegong123) – Follow the Link: Building Full-Chain Local Privilege Escalation on Windows 🔗🪟
#POC2025
Bocheng Xiang (@crispr_x) & HeeChan Kim (@heegong123) – Follow the Link: Building Full-Chain Local Privilege Escalation on Windows 🔗🪟
#POC2025

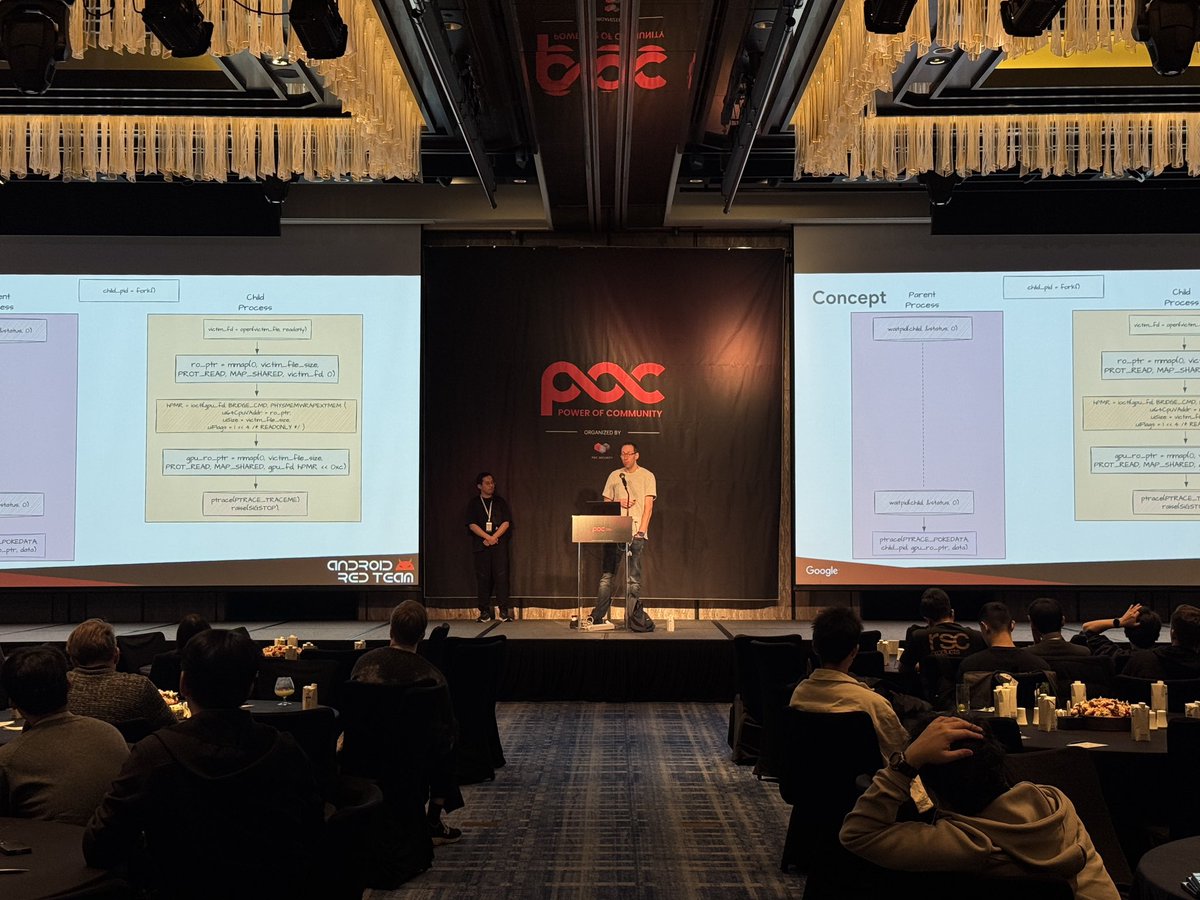
Sweet talk, enjoyed it!
Xingyu Jin (@1ce0ear) & Martijn Bogaard (@jmartijnb) – Dirty Ptrace: Exploiting Undocumented Behaviors in Kernel mmap Handlers 🐧🛠️
#POC2025
Xingyu Jin (@1ce0ear) & Martijn Bogaard (@jmartijnb) – Dirty Ptrace: Exploiting Undocumented Behaviors in Kernel mmap Handlers 🐧🛠️
#POC2025
Fuzzing, Fuzzing!
Innokentii Sennovskii (@Rumata888) – Zero Knowledge, Full Coverage: A Fuzzing Paradox ⛓️🔍
#POC2025
Innokentii Sennovskii (@Rumata888) – Zero Knowledge, Full Coverage: A Fuzzing Paradox ⛓️🔍
#POC2025

Big thumbs up for this one 👍
Alfie CG (@alfiecg_dev) – Trigon: developing a deterministic iOS kernel exploit 📱
#POC2025
Alfie CG (@alfiecg_dev) – Trigon: developing a deterministic iOS kernel exploit 📱
#POC2025

#POC2025 x @FlagYard CTF is going great so far! 🔥
Shoutout to all players grinding through the challenges.
Keep hacking and stay tuned for the final result soon!
Shoutout to all players grinding through the challenges.
Keep hacking and stay tuned for the final result soon!

Nice flow, nice talk 😎
Yongkang Jia (@j_kangel) & Xiao Lei (@N0p_Orz) – Bug Tamer: Turning Limited Heap Overflow into Full VMware Escape 🖥️
#POC2025
Yongkang Jia (@j_kangel) & Xiao Lei (@N0p_Orz) – Bug Tamer: Turning Limited Heap Overflow into Full VMware Escape 🖥️
#POC2025

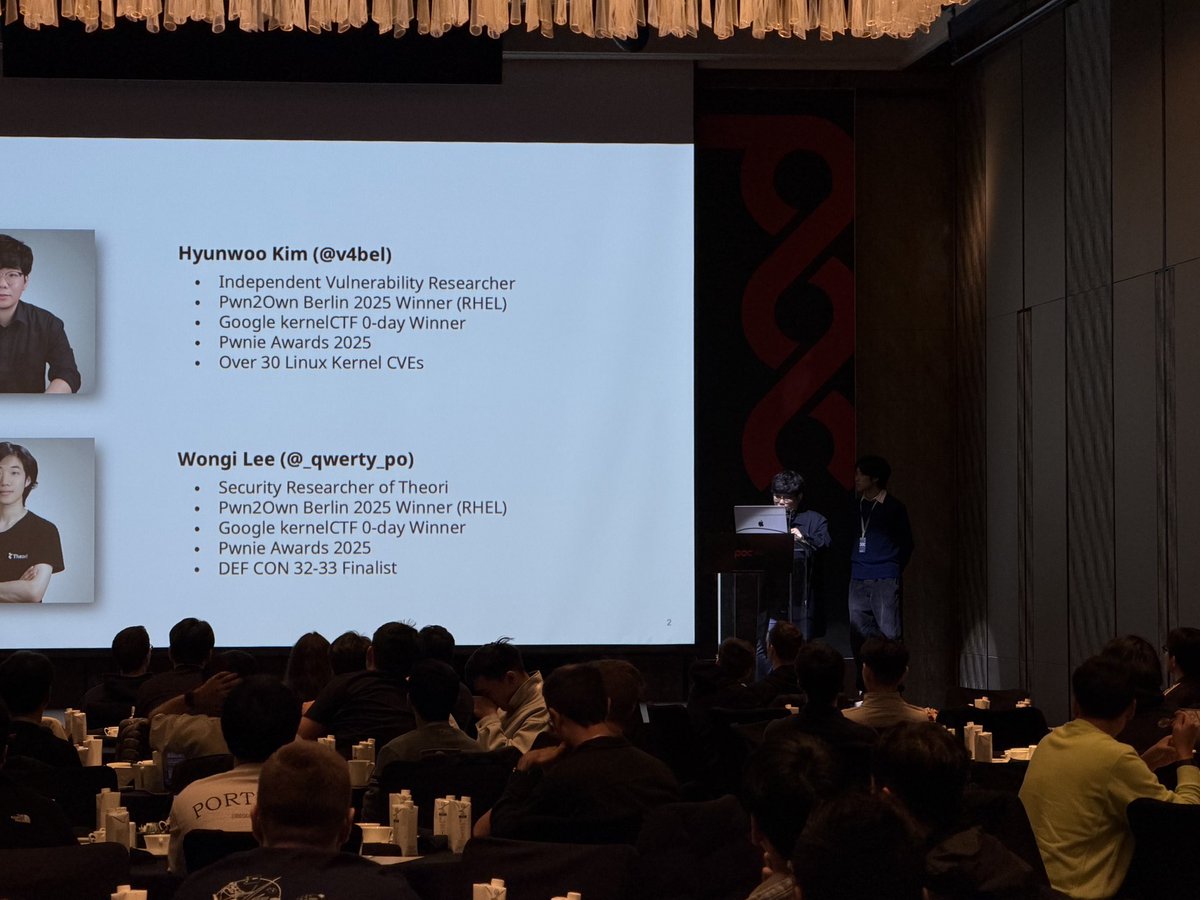
Enjoyed every minute 😄
Hyunwoo Kim (@v4bel) & Wongi Lee (@_qwerty_po) – Race Condition Symphony: From Tiny Idea to Pwnie 🐧🎶
#POC2025
Hyunwoo Kim (@v4bel) & Wongi Lee (@_qwerty_po) – Race Condition Symphony: From Tiny Idea to Pwnie 🐧🎶
#POC2025
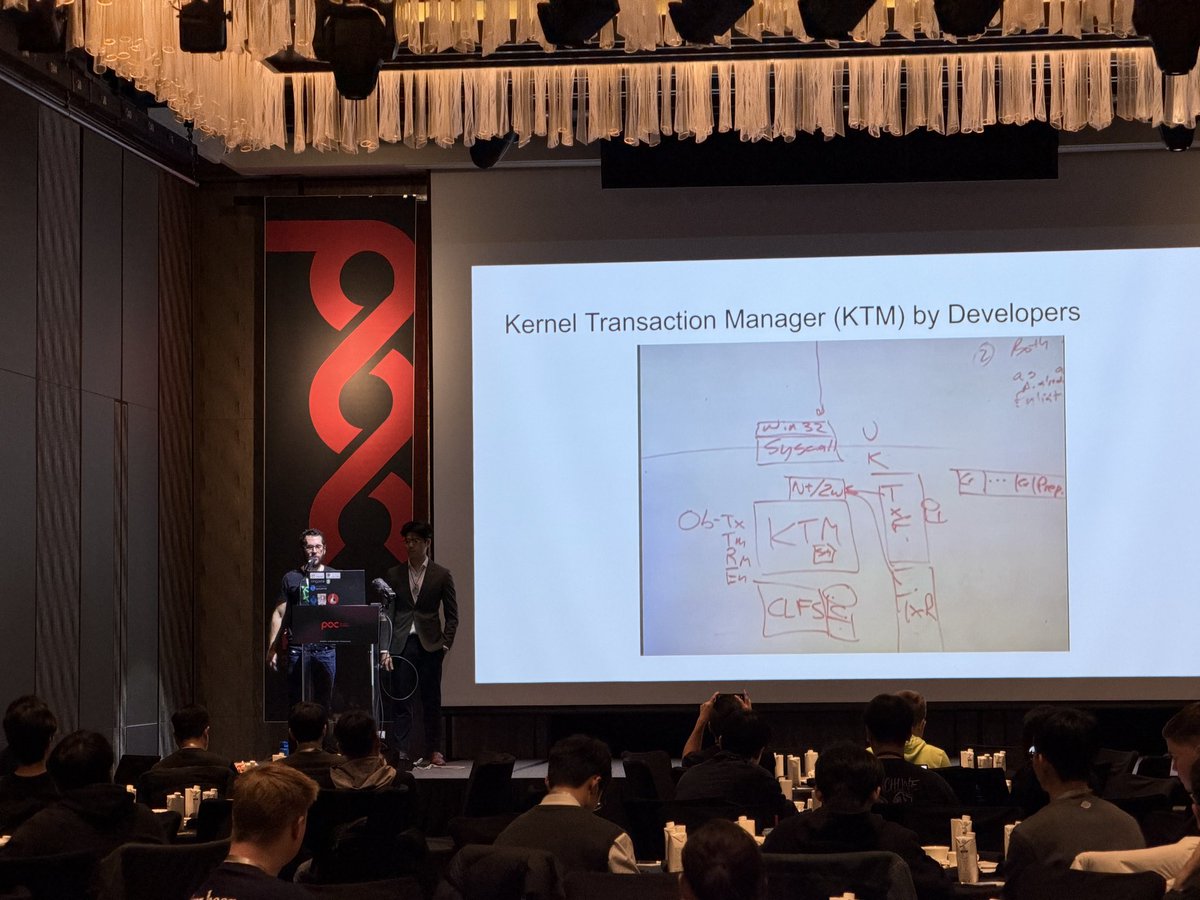
Good vibes from this one ✨
Cedric Halbronn (@saidelike) & Jael Koh (@_jaelkoh) – Revisiting Windows 11 KTM: Lessons Learnt from New Vulnerabilities 🪟
#POC2025
Cedric Halbronn (@saidelike) & Jael Koh (@_jaelkoh) – Revisiting Windows 11 KTM: Lessons Learnt from New Vulnerabilities 🪟
#POC2025
Yup, that was awesome 😎
Xuangan Xiao (@xgxiao66) & Zikai Xu (@N7utbN) – The Biometric AuthToken Heist: Cracking PINs and Bypassing CE via a Long Ignored Attack Surface 🔐
#POC2025
Xuangan Xiao (@xgxiao66) & Zikai Xu (@N7utbN) – The Biometric AuthToken Heist: Cracking PINs and Bypassing CE via a Long Ignored Attack Surface 🔐
#POC2025

I hope you guys enjoyed today and see you tomorrow 😘
#POC2025
#POC2025

Loved this one, seriously 😆
Christine Fossaceca (@x71n3) – (Sploit)Lights, Camera, Action! Exploiting Spotlight to Bypass TCC and Leak Data from Apple Intelligence 🍎🎬
#POC2025
Christine Fossaceca (@x71n3) – (Sploit)Lights, Camera, Action! Exploiting Spotlight to Bypass TCC and Leak Data from Apple Intelligence 🍎🎬
#POC2025

Big fan of this session 😎
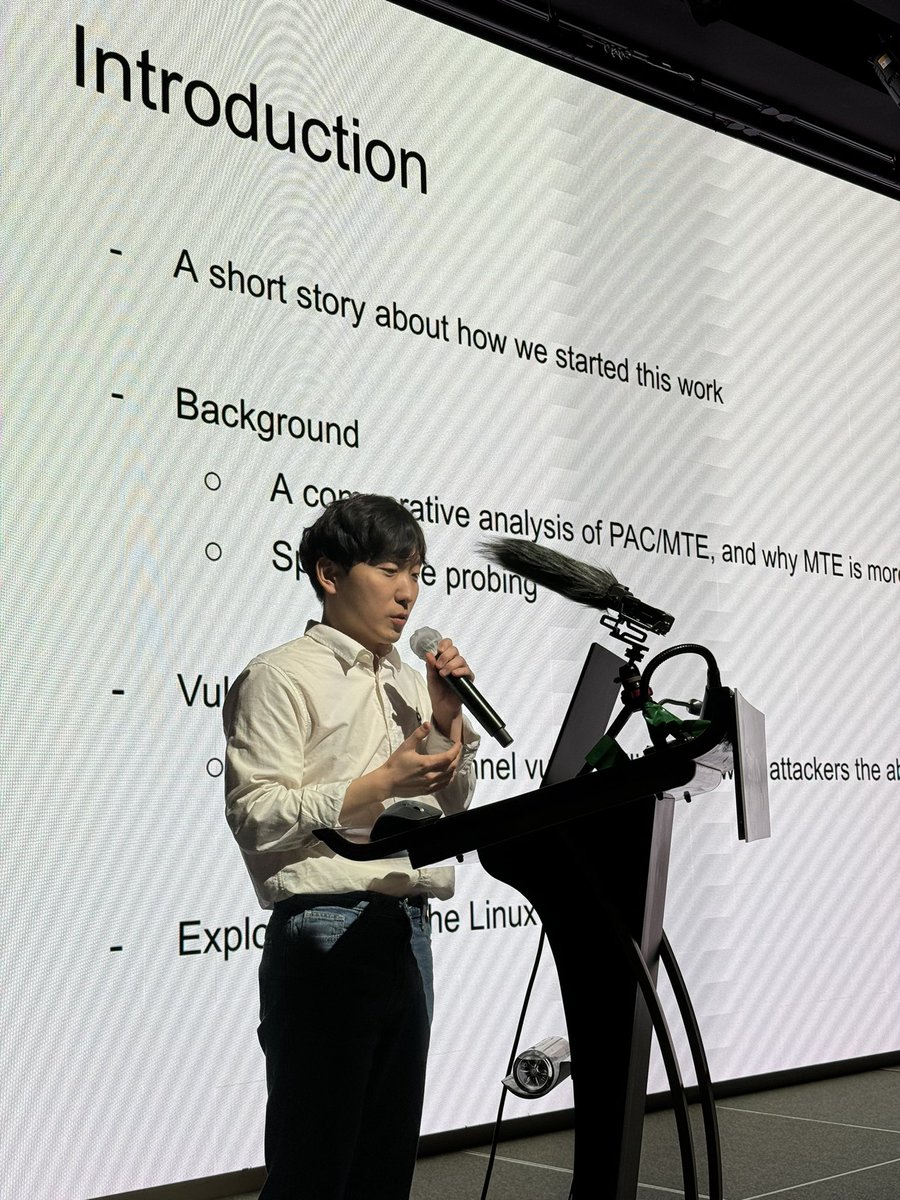
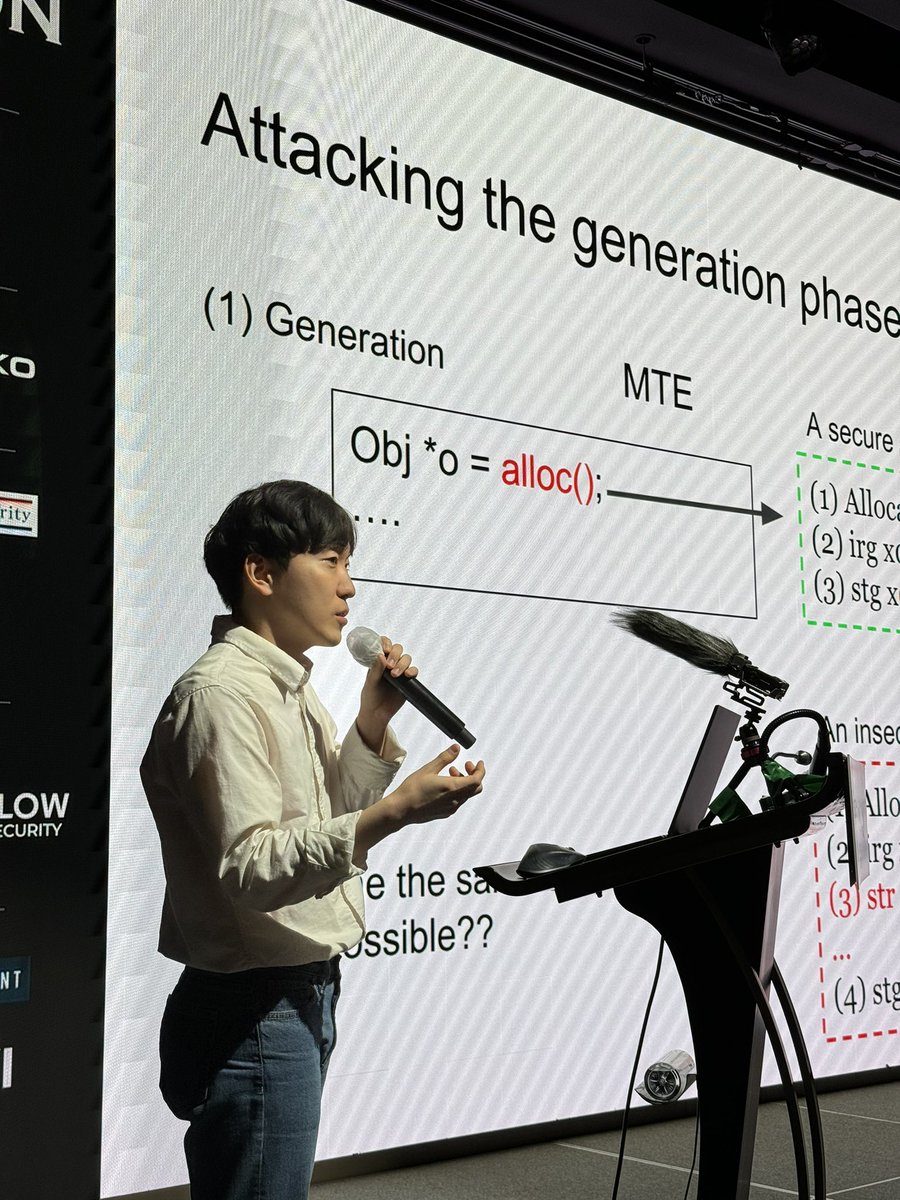
Yong Wang (@ThomasKing2014) – A tale of challenging MTE: Rooting Google Pixel with kernel MTE enabled in one shot 🔧
#POC2025
Yong Wang (@ThomasKing2014) – A tale of challenging MTE: Rooting Google Pixel with kernel MTE enabled in one shot 🔧
#POC2025

Such a good presentation 🤙
Igor Sak-Sakovskiy (@psych0tr1a) – Internet explorer isn't forgotten 🕸️
#POC2025
Igor Sak-Sakovskiy (@psych0tr1a) – Internet explorer isn't forgotten 🕸️
#POC2025

Great talk! Loved it 😄
Mikhail Evdokimov (@konatabrk) – PerfektBlue: Universal 1-click Exploit to Pwn Automotive Industry — Mercedes-Benz, Volkswagen, Škoda, and others 🚗
#POC2025
Mikhail Evdokimov (@konatabrk) – PerfektBlue: Universal 1-click Exploit to Pwn Automotive Industry — Mercedes-Benz, Volkswagen, Škoda, and others 🚗
#POC2025

We had a wonderful community time thanks to @Binary_Gecko .
Don’t forget we also have a cocktail hour tomorrow!
Cheers 🥂
#POC2025
Don’t forget we also have a cocktail hour tomorrow!
Cheers 🥂
#POC2025


Zuotong Feng & JiaLiang Wu – Large Language Models-Powered Defense Upgrade: Reshaping the Automated Path for APT Intelligence Operations and Live Drills 🤝🤖
#POC2025
#POC2025

Incredible talk!
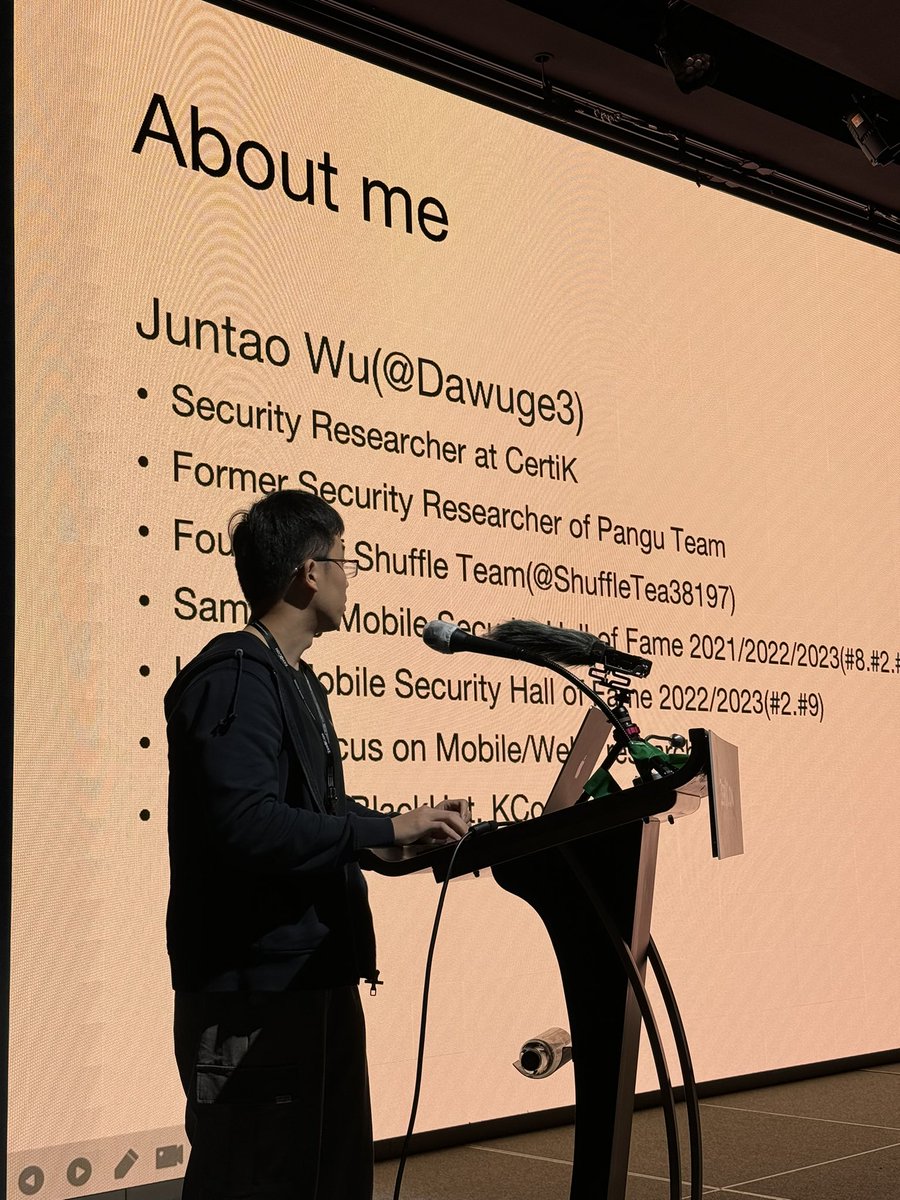
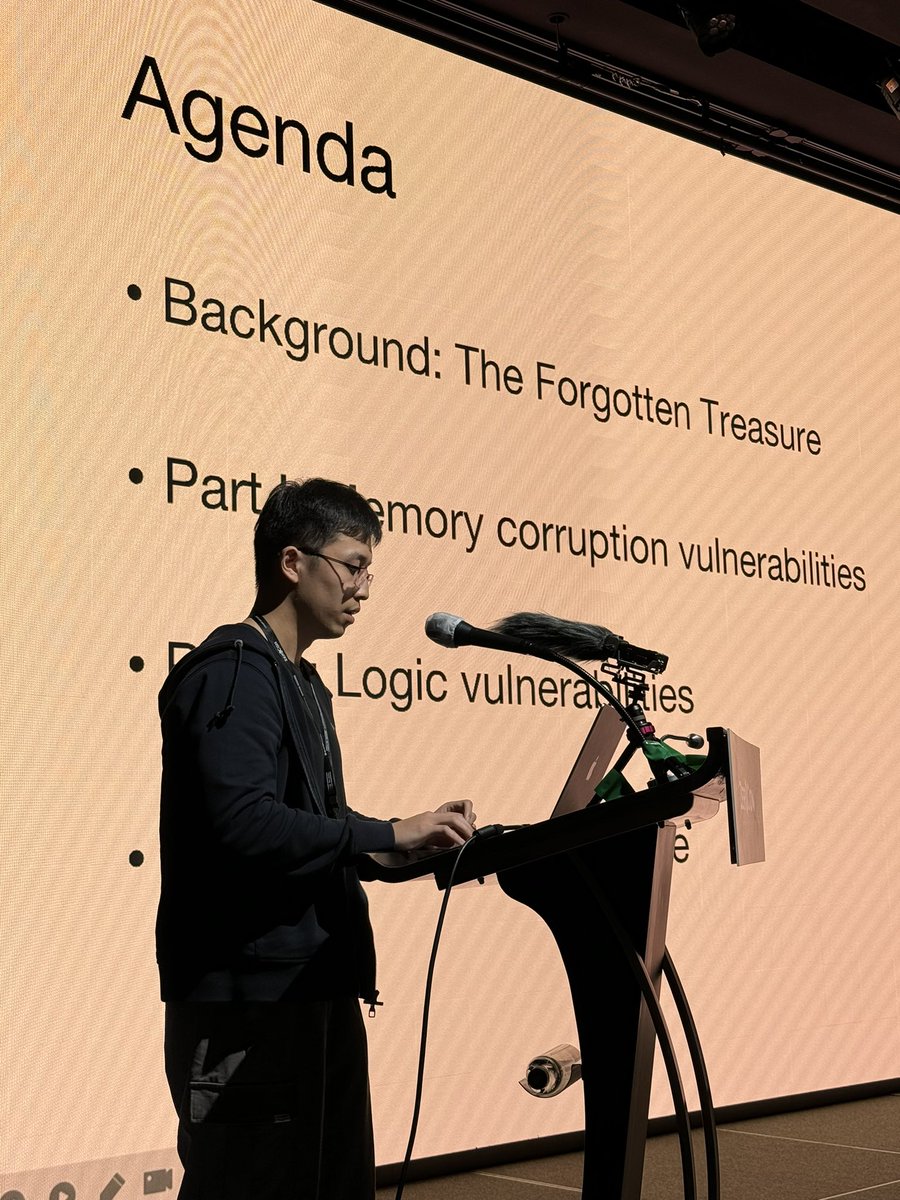
Juntao Wu (@wugedbl) & Hangyu Hua (@HBh25Y) – Security World Vulnerability Discovery Across Diverse Chip Architectures 🔎
#POC2025
Juntao Wu (@wugedbl) & Hangyu Hua (@HBh25Y) – Security World Vulnerability Discovery Across Diverse Chip Architectures 🔎
#POC2025

Master of JSE
Samuel Groß (@5aelo) – JavaScript Engine Security in 2025: New Bugs, New Defenses 🌐
#POC2025
Samuel Groß (@5aelo) – JavaScript Engine Security in 2025: New Bugs, New Defenses 🌐
#POC2025


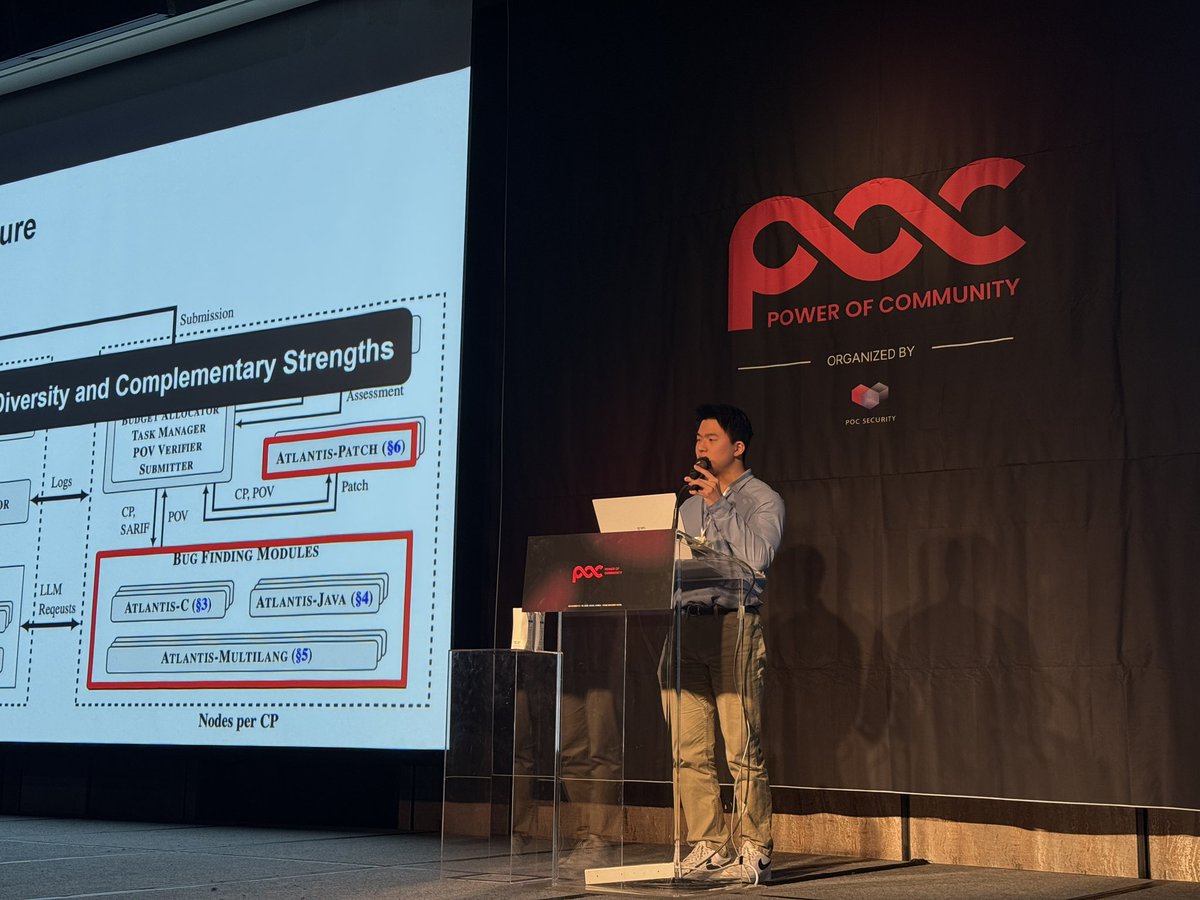
What a Brilliant Team!
Woosun Song (@pr0cf51) – ATLANTIS: AI-driven Threat Localization, Analysis, and Triage Intelligence System 🤖
#POC2025
Woosun Song (@pr0cf51) – ATLANTIS: AI-driven Threat Localization, Analysis, and Triage Intelligence System 🤖
#POC2025

Huge thanks for the keynote 💙
It was fantastic.
Brian Gorenc (@MaliciousInput) – From Buffer Overflows to Breaking AI: Two Decades of ZDI Vulnerability Research 🎤
#POC2025
It was fantastic.
Brian Gorenc (@MaliciousInput) – From Buffer Overflows to Breaking AI: Two Decades of ZDI Vulnerability Research 🎤
#POC2025


Ready to roll. #POC2025


POC2025 x @hackyboiz !
Step into the world of Hackyboiz’s Squid Game!
Visit our booth and take on classic Korean challenges:
- 🍬 Dalgona Candy
- 🥏 Jegichagi
- 🟦🟥 Ddakji
- 🤖👧 Mad Young-hee
○△□ You are invited. Can you survive them all?
#POC2025
Step into the world of Hackyboiz’s Squid Game!
Visit our booth and take on classic Korean challenges:
- 🍬 Dalgona Candy
- 🥏 Jegichagi
- 🟦🟥 Ddakji
- 🤖👧 Mad Young-hee
○△□ You are invited. Can you survive them all?
#POC2025
All three trainings have kicked off smoothly! 🚀
Wishing everyone a great 3-day session ahead — see you all at the conference! 😎
#POC2025
Wishing everyone a great 3-day session ahead — see you all at the conference! 😎
#POC2025



🔥 [POC2025] Drinking Hell 🔥
Survive the night, Be the final boss
Welcome to legendary "Drinking Hell", the unofficial (but totally essential) closing ritual of POC
No slides, no exploits — just pure chaos, laughter, and memories.
💀 When & Where: After the Day 2 dinner - just
Survive the night, Be the final boss
Welcome to legendary "Drinking Hell", the unofficial (but totally essential) closing ritual of POC
No slides, no exploits — just pure chaos, laughter, and memories.
💀 When & Where: After the Day 2 dinner - just

Drop your business card and win! 💥
Join the POC2025 Lucky Draw and stand a chance to win:
🥇 iPad 2025 128GB
🥈 AirPods 4
🥉 Logitech MX Master 4
Simply place your card in the event box and wait for the draw!
Winners will be announced during the Closing Ceremony on Nov 14.
Join the POC2025 Lucky Draw and stand a chance to win:
🥇 iPad 2025 128GB
🥈 AirPods 4
🥉 Logitech MX Master 4
Simply place your card in the event box and wait for the draw!
Winners will be announced during the Closing Ceremony on Nov 14.

POC2025 Photo Challenge! 📸
Strike a pose, snap a shot, and join the fun!
Take your photo using the instant camera on-site, post it on the event board, and let the crowd decide. 🗳️
The top 5 teams with the most votes will each win a pair of Samsung Galaxy Buds Pro 3! 🎧
Winners
Strike a pose, snap a shot, and join the fun!
Take your photo using the instant camera on-site, post it on the event board, and let the crowd decide. 🗳️
The top 5 teams with the most votes will each win a pair of Samsung Galaxy Buds Pro 3! 🎧
Winners
Level unlocked: Diamond Sponsor 💎
Proud to have Radiant(@RRLabs32) as our Diamond Sponsor at POC2025.
Based in Israel and Europe, we take on the toughest challenges and seek fearless researchers to push boundaries with us.
#POC2025
Proud to have Radiant(@RRLabs32) as our Diamond Sponsor at POC2025.
Based in Israel and Europe, we take on the toughest challenges and seek fearless researchers to push boundaries with us.
#POC2025
PARTY Sponsor 🥂🍹🍸🍷
Thank you @SAFATeamApS for sponsoring Party for the conference!
SAFA driven by top-tier experts, stands at the forefront of European research, while breaking the glass ceiling they are uncovering tomorrow’s vulnerabilities before anyone else.
#POC2025
Thank you @SAFATeamApS for sponsoring Party for the conference!
SAFA driven by top-tier experts, stands at the forefront of European research, while breaking the glass ceiling they are uncovering tomorrow’s vulnerabilities before anyone else.
#POC2025

PARTY Sponsor 🥂🍹🍸🍷
Thank you @prdgmshift for sponsoring Party for the conference!
Paradigm Shift is Europe’s premier security research hub, powered by a dream team of world-class researchers with an unrivaled track record.
#POC2025
Thank you @prdgmshift for sponsoring Party for the conference!
Paradigm Shift is Europe’s premier security research hub, powered by a dream team of world-class researchers with an unrivaled track record.
#POC2025

Congratulations to everyone who made it to the CTF finals!
Wishing you all the best of luck and great results.
@FlagYard #POC2025
Wishing you all the best of luck and great results.
@FlagYard #POC2025

[POC2025] Gold Sponsor 🌕
Big appreciate the boost!
@Binary_Gecko , which also runs Offensivecon, is a German company who conducts the the most complex Vulnerability Research out there.
They aim to be the best company in the world for talented researchers with a "work hard -
Big appreciate the boost!
@Binary_Gecko , which also runs Offensivecon, is a German company who conducts the the most complex Vulnerability Research out there.
They aim to be the best company in the world for talented researchers with a "work hard -

[POC2025] - Full Speaker Lineup Revealed! 🔥
We’re thrilled to unveil the incredible minds shaping this year’s 20th anniversary stage.
#POC2025
We’re thrilled to unveil the incredible minds shaping this year’s 20th anniversary stage.
#POC2025

[POC2025] SPEAKER UPDATE
👤 Samuel Groß(@5aelo) - "JavaScript Engine Security in 2025: New Bugs, New Defenses"
#POC2025
👤 Samuel Groß(@5aelo) - "JavaScript Engine Security in 2025: New Bugs, New Defenses"
#POC2025

[POC2025] SPEAKER UPDATE
👤 Christine Fossaceca(@x71n3) - "(Sploit)Lights, Camera, Action! Exploiting Spotlight to Bypass TCC and Leak Data from Apple Intelligence"
#POC2025
👤 Christine Fossaceca(@x71n3) - "(Sploit)Lights, Camera, Action! Exploiting Spotlight to Bypass TCC and Leak Data from Apple Intelligence"
#POC2025

[POC2025] SPEAKER UPDATE
👤 Woosun Song(@pr0cf51) - "ATLANTIS: AI-driven Threat Localization, Analysis, and Triage Intelligence System"
#POC2025
👤 Woosun Song(@pr0cf51) - "ATLANTIS: AI-driven Threat Localization, Analysis, and Triage Intelligence System"
#POC2025

[POC2025] SPEAKER UPDATE
👥 Yongkang Jia(@j_kangel) & Xiao Lei(@N0p_Orz) - "Bug Tamer: Turning Limited Heap Overflow into Full VMware Escape"
#POC2025
👥 Yongkang Jia(@j_kangel) & Xiao Lei(@N0p_Orz) - "Bug Tamer: Turning Limited Heap Overflow into Full VMware Escape"
#POC2025

[POC2025] SPEAKER UPDATE
👥 Zuotong Feng & JiaLiang Wu - "Large Language Models-Powered Defense Upgrade: Reshaping the Automated Path for APT Intelligence Operations and Live Drills"
#POC2025
👥 Zuotong Feng & JiaLiang Wu - "Large Language Models-Powered Defense Upgrade: Reshaping the Automated Path for APT Intelligence Operations and Live Drills"
#POC2025

[POC2025] SPEAKER UPDATE
👤 Igor Sak-Sakovksiy(@psych0tr1a) - "Internet explorer isn't forgotten"
#POC2025
👤 Igor Sak-Sakovksiy(@psych0tr1a) - "Internet explorer isn't forgotten"
#POC2025

[POC2025] SPEAKER UPDATE
👤 Innokentii Sennovskii(@Rumata888) - "Zero Knowledge, Full Coverage: A Fuzzing Paradox"
#POC2025
👤 Innokentii Sennovskii(@Rumata888) - "Zero Knowledge, Full Coverage: A Fuzzing Paradox"
#POC2025

[POC2025] SPEAKER UPDATE
👥 Hyunwoo Kim(@v4bel) & Wongi Lee(@_qwerty_po) - "Race Condition Symphony: From Tiny Idea to Pwnie"
#POC2025
👥 Hyunwoo Kim(@v4bel) & Wongi Lee(@_qwerty_po) - "Race Condition Symphony: From Tiny Idea to Pwnie"
#POC2025

[POC2025] SPEAKER UPDATE
👤 Yong Wang(@ThomasKing2014) - "A tale of challenging MTE: Rooting Google Pixel with kernel MTE enabled in one shot"
#POC2025
👤 Yong Wang(@ThomasKing2014) - "A tale of challenging MTE: Rooting Google Pixel with kernel MTE enabled in one shot"
#POC2025

[POC2025] SPEAKER UPDATE
👥 Xingyu Jin(@1ce0ear) & Martijn Bogaard - "Dirty Ptrace: Exploiting Undocumented Behaviors in Kernel mmap Handlers"
#POC2025
👥 Xingyu Jin(@1ce0ear) & Martijn Bogaard - "Dirty Ptrace: Exploiting Undocumented Behaviors in Kernel mmap Handlers"
#POC2025

[POC2025] SPEAKER UPDATE
👥 Cedric Halbronn(@saidelike) & Jael Koh(@_jaelkoh) - "Hunting for overlooked cookies in Windows 11 KTM and baking exploits for them"
#POC2025
👥 Cedric Halbronn(@saidelike) & Jael Koh(@_jaelkoh) - "Hunting for overlooked cookies in Windows 11 KTM and baking exploits for them"
#POC2025

[POC2025] SPEAKER UPDATE
👥 Bocheng Xiang(@crispr_x) & HeeChan Kim(@heegong123) - "Follow the Link: Building Full-Chain Local Privilege Escalation on Windows"
#POC2025
👥 Bocheng Xiang(@crispr_x) & HeeChan Kim(@heegong123) - "Follow the Link: Building Full-Chain Local Privilege Escalation on Windows"
#POC2025

[POC2025] SPEAKER UPDATE
👥 Juntao Wu(@Dawuge3) & Hangyu Hua(@HBh25Y) - "Security World Vulnerability Discovery Across Diverse Chip Architectures"
#POC2025
👥 Juntao Wu(@Dawuge3) & Hangyu Hua(@HBh25Y) - "Security World Vulnerability Discovery Across Diverse Chip Architectures"
#POC2025

Off to Paris for @hexacon_fr 🇫🇷
Let’s catch up over wine.
Let’s catch up over wine.

🚩 THE COUNTDOWN BEGINS!
#POC2025 CTF x @FlagYard will be the highlight event of our anniversary year.
• Qualifiers (Online): October 12, 2025
• Finals (Onsite): November 13-14, 2025
📍 Venue: Four Seasons Hotel, Seoul, South Korea
Join the global hacking community, prove
#POC2025 CTF x @FlagYard will be the highlight event of our anniversary year.
• Qualifiers (Online): October 12, 2025
• Finals (Onsite): November 13-14, 2025
📍 Venue: Four Seasons Hotel, Seoul, South Korea
Join the global hacking community, prove

[POC2025] Gold Sponsor🌕
Huge thanks to @epsilon_sec — lucky to have you with us! 🙏
"Epsilon is a European company focused on high-end research that values technical excellence, teamwork and a fun culture!"
#POC2025
Huge thanks to @epsilon_sec — lucky to have you with us! 🙏
"Epsilon is a European company focused on high-end research that values technical excellence, teamwork and a fun culture!"
#POC2025

[POC2025] Gold Sponsor🌕
Shout-out to @amazon for the continued partnership and support! ⚡️
"At Amazon, security is job zero. Our security teams are central to maintaining customer trust and delivering delightful customer experiences at global scale."
#POC2025
Shout-out to @amazon for the continued partnership and support! ⚡️
"At Amazon, security is job zero. Our security teams are central to maintaining customer trust and delivering delightful customer experiences at global scale."
#POC2025

[POC2025] Gold Sponsor🌕
Thanks a bunch! - @CorelliumHQ again, being part of the journey 🙏🌟
"Corellium provides security research tools for iOS/Android focused on vulnerability research, application security, malware analysis and forensics - we look forward to meeting
Thanks a bunch! - @CorelliumHQ again, being part of the journey 🙏🌟
"Corellium provides security research tools for iOS/Android focused on vulnerability research, application security, malware analysis and forensics - we look forward to meeting

[POC2025] Gold Sponsor🌕
Big love to @pksecurity_io for the awesome support!💙
"We do sophisticated R&D in various areas like Windows, Android, ioT and Web. Check us out IRL! exciting to see you there and hear your story!"
#POC2025
Big love to @pksecurity_io for the awesome support!💙
"We do sophisticated R&D in various areas like Windows, Android, ioT and Web. Check us out IRL! exciting to see you there and hear your story!"
#POC2025

[POC2025] KEYNOTE SPEAKER UPDATE
👤 Brian Gorenc(@MaliciousInput) – "From Buffer Overflows to Breaking AI: Two Decades of ZDI Vulnerability Research"
ZDI(@thezdi) also stands with their 20 years!
Now AI finds 0days—
but the bugs? still the same old mess.
#POC2025
👤 Brian Gorenc(@MaliciousInput) – "From Buffer Overflows to Breaking AI: Two Decades of ZDI Vulnerability Research"
ZDI(@thezdi) also stands with their 20 years!
Now AI finds 0days—
but the bugs? still the same old mess.
#POC2025

[POC2025] SPEAKER UPDATE 4⃣
👤 Alfie CG(@alfiecg_dev) – "Trigon: Developing a deterministic iOS Kernel Exploit"
#POC2025
👤 Alfie CG(@alfiecg_dev) – "Trigon: Developing a deterministic iOS Kernel Exploit"
#POC2025

[POC2025] SPEAKER UPDATE 3⃣
👤 Mikhail Evdokimov(@konatabrk) -
"PerfektBlue: Universal 1-click Exploit to Pwn Automotive Industry - Mercedes-Benz, Volkswagen, Skoda and Others"
#POC2025
👤 Mikhail Evdokimov(@konatabrk) -
"PerfektBlue: Universal 1-click Exploit to Pwn Automotive Industry - Mercedes-Benz, Volkswagen, Skoda and Others"
#POC2025

[POC2025] SPEAKER UPDATE 2⃣
👥 Xuangan Xiao(@xgxiao66) & Zikai Xu(@N7utbN) – "The Biometric AuthToken Heist: Cracking PINs and Bypassing CE via a Long Ignored Attack Surface"
#POC2025
👥 Xuangan Xiao(@xgxiao66) & Zikai Xu(@N7utbN) – "The Biometric AuthToken Heist: Cracking PINs and Bypassing CE via a Long Ignored Attack Surface"
#POC2025

[#POC2025] Registration is NOW OPEN!
Early Bird: Sept 1 – Sept 30
Standard: Oct 1 – Oct 30
CFP is still OPEN —
We’re already seeing 🔥 talks coming in
Got something bold, brilliant, or badass?
Submit yours before → Sept 30
📢1st Speaker Line-up drops this week🙏
🌐
Early Bird: Sept 1 – Sept 30
Standard: Oct 1 – Oct 30
CFP is still OPEN —
We’re already seeing 🔥 talks coming in
Got something bold, brilliant, or badass?
Submit yours before → Sept 30
📢1st Speaker Line-up drops this week🙏
🌐
There’s been a slight change in the schedule.
Stay tuned! 😎 #POC2025
Stay tuned! 😎 #POC2025

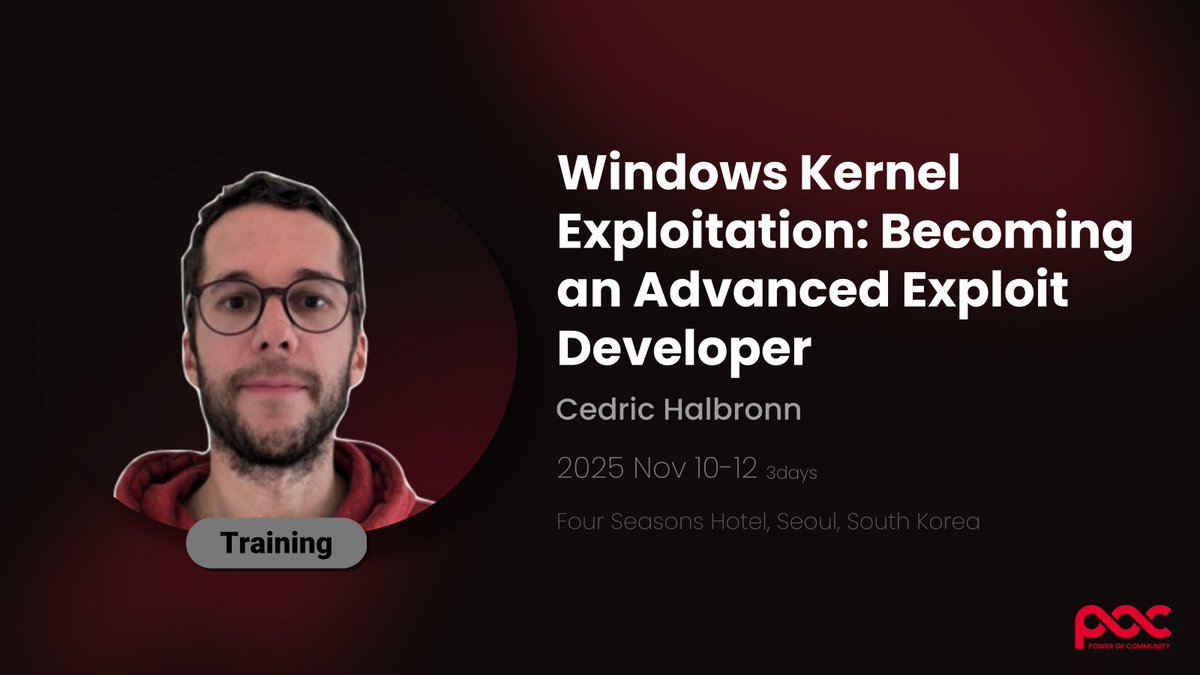
🧠 [POC2025] TRAINING
Windows Kernel Exploitation: Becoming an "Advanced" Exploit Developer
by Cedric Halbronn (@saidelike)
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025
Windows Kernel Exploitation: Becoming an "Advanced" Exploit Developer
by Cedric Halbronn (@saidelike)
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025
🔍 [POC2025] TRAINING
Chrome (Renderer) Exploitation on Android
by Vitaly Nikolenko (@vnik5287)
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025
Chrome (Renderer) Exploitation on Android
by Vitaly Nikolenko (@vnik5287)
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025

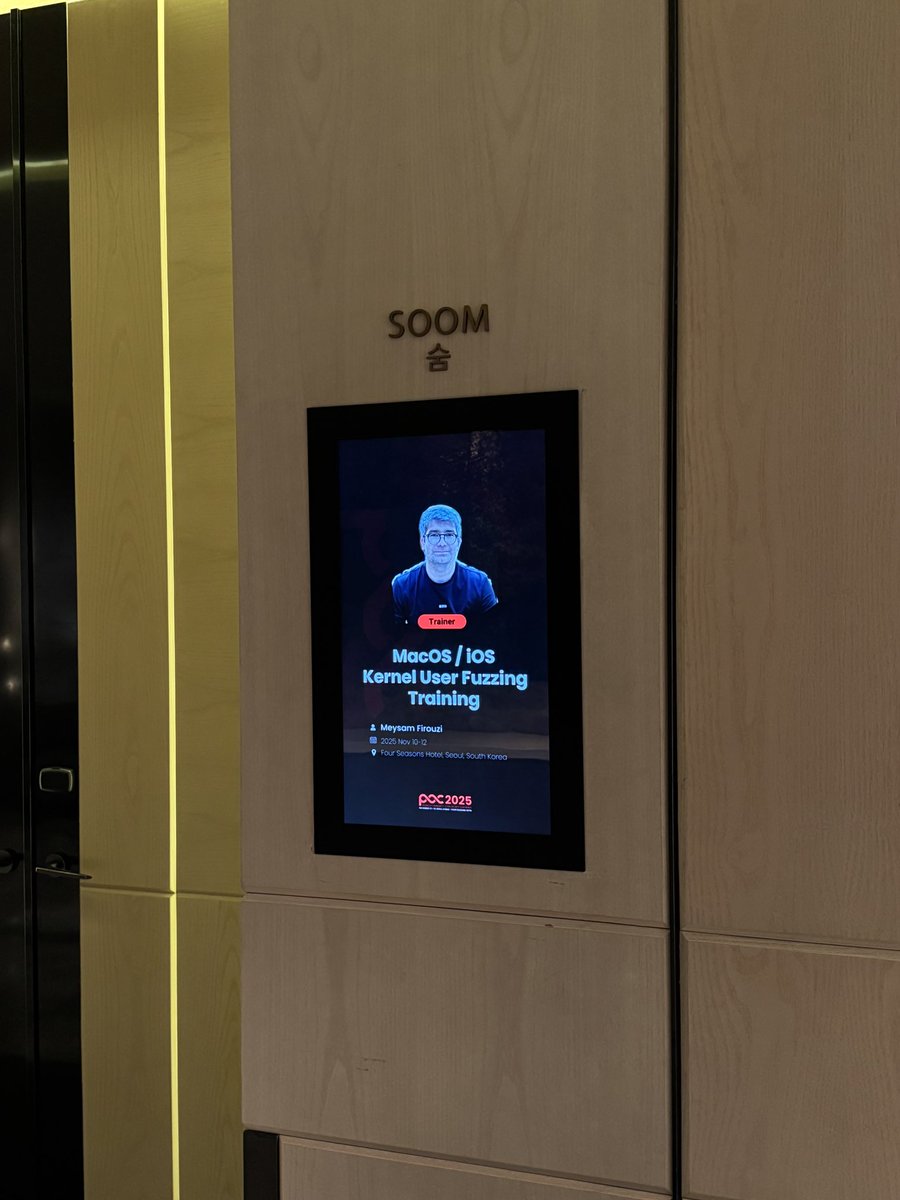
🛠️ [POC2025] TRAINING
MacOS/iOS Kernel User Fuzzing Training
by Meysam Firouzi (@R00tkitSMM)
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025
MacOS/iOS Kernel User Fuzzing Training
by Meysam Firouzi (@R00tkitSMM)
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025

🎯 [POC2025] TRAINING
Reversing Modern Binaries: Practical Rust & Go Analysis
by Nabih Benazzouz (@Raefko) & Daniel Frederic from @FuzzingLabs
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025
Reversing Modern Binaries: Practical Rust & Go Analysis
by Nabih Benazzouz (@Raefko) & Daniel Frederic from @FuzzingLabs
📅 Nov 10-12 (3 days)
📍 Four Seasons Hotel Seoul, South Korea
🔗 More info https://t.co/hdGfRfgx9k
#POC2025

Our crew has brought back a glimpse of the future from Greece 🇬🇷

Anyone here in Greece for OffensiveX?
Ping us up! Let's catch up!
Ping us up! Let's catch up!

[#POC2025 NOTICE]
20 Years. Reborn.
The brand evolved - The mission remains.
Welcome to a new era of POC.
⏰ Date: November 13–14, 2025
📍 Venue: Four Seasons Hotel, Seoul, South Korea 🇰🇷
🎤 CFP: June 5 – September 30
🧑💻 Training: June 5 – September 30
🎟️ Registration:
20 Years. Reborn.
The brand evolved - The mission remains.
Welcome to a new era of POC.
⏰ Date: November 13–14, 2025
📍 Venue: Four Seasons Hotel, Seoul, South Korea 🇰🇷
🎤 CFP: June 5 – September 30
🧑💻 Training: June 5 – September 30
🎟️ Registration:

We’re about to board our flight back to Korea. The SINCON2025 organizers(@Infosec_City) and staff were incredibly passionate, they’ll definitely need some well-deserved rest to recharge😉. Thank you so much for having us and running such an awesome conference! 🔥


Boarding now for SINCON(@Infosec_City) Singapore. If you’re around, let’s catch up over kopi or drinks 😉


Huge thanks to @offensive_con organizers for crafting such unforgettable and flawlessly organized experience.
Big shoutout to sponsors and the amazing researchers gathered from all around the world - you guys made this truly inspiring🙏
Already counting down to next edition!
Big shoutout to sponsors and the amazing researchers gathered from all around the world - you guys made this truly inspiring🙏
Already counting down to next edition!



Off to Berlin! Very excited to be part of the community and sponsor @offensive_con! If you are there, ping us up for long night drinks 🫠😏


[#Zer0Con2025] After Party ON! 🎉
Today, we shut down IDA.
And boot up memories we won’t debug tomorrow.
Massive thanks to @SAFATeamGmbH & @prdgmshift for making it happen.
The night is just getting started! 🪩🫧🍸🥂🫧✧˖°
Today, we shut down IDA.
And boot up memories we won’t debug tomorrow.
Massive thanks to @SAFATeamGmbH & @prdgmshift for making it happen.
The night is just getting started! 🪩🫧🍸🥂🫧✧˖°




[#Zer0Con2025]
🎙️ SPEAKER Highlight: @zblee_ / @zhz__6951 / @Mr_LiuYue
"vCenter Lost: How the DCERPC vulnerabilities Changed the Fate of ESXi" 🚀
🎙️ SPEAKER Highlight: @zblee_ / @zhz__6951 / @Mr_LiuYue
"vCenter Lost: How the DCERPC vulnerabilities Changed the Fate of ESXi" 🚀

[#Zer0Con2025]
🎙️ SPEAKER Highlight: @matteomalvica
"Breaking Chrome's V8: Type Confusion, WASM JIT-Spraying and Heap Sandbox Evasion" 💥
🎙️ SPEAKER Highlight: @matteomalvica
"Breaking Chrome's V8: Type Confusion, WASM JIT-Spraying and Heap Sandbox Evasion" 💥

[#Zer0Con2025]
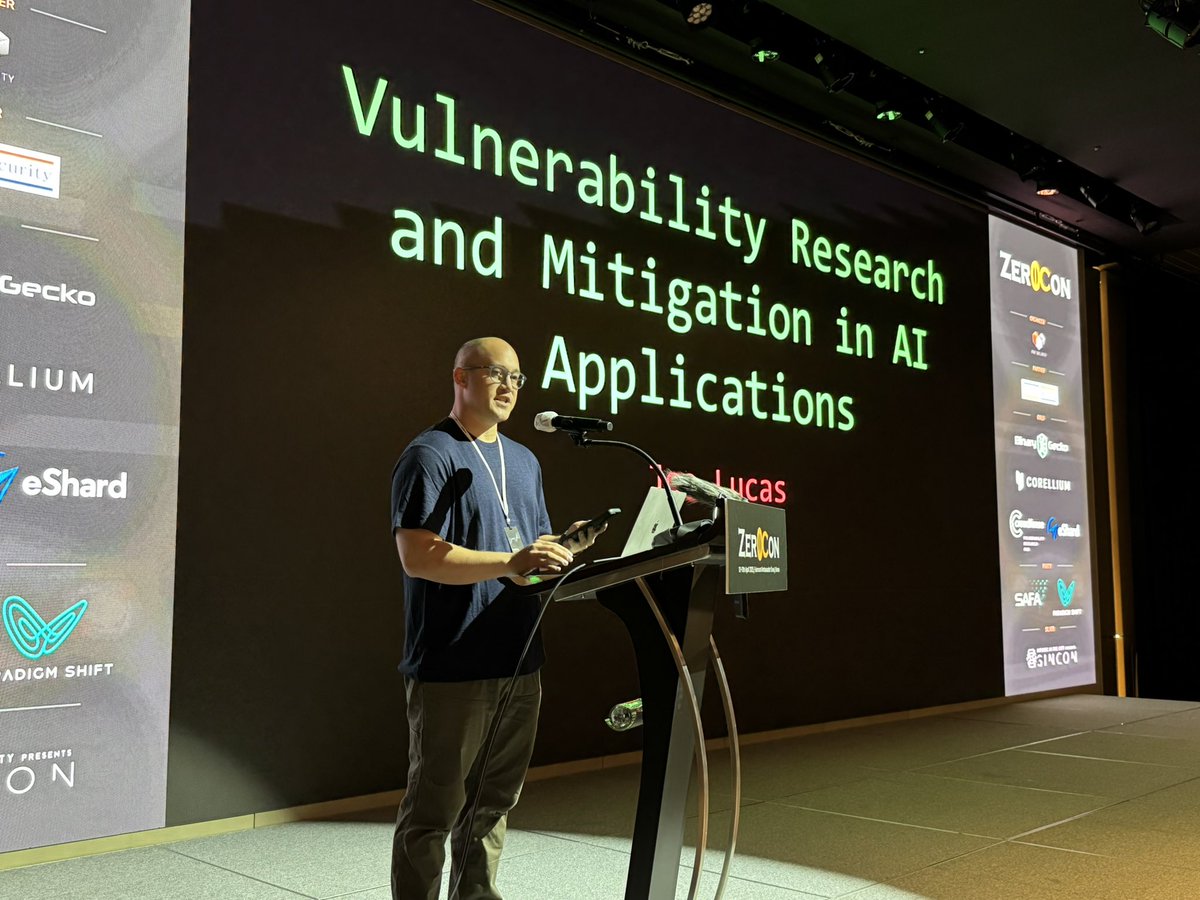
🎙️ SPEAKER Highlight: @josephtlucas
"Vulnerability Research and Mitigation in AI Applications" 🤖
🎙️ SPEAKER Highlight: @josephtlucas
"Vulnerability Research and Mitigation in AI Applications" 🤖
@azraelxuemo Interesting indeed😆
[#Zer0Con2025]
🎙️ SPEAKER Highlight: @lxt33r / @mhoste1
"Ethereum's Achilles' Heel: Attacking and Fuzzing EVMs for Fun (and Profits)" 💼
🎙️ SPEAKER Highlight: @lxt33r / @mhoste1
"Ethereum's Achilles' Heel: Attacking and Fuzzing EVMs for Fun (and Profits)" 💼

[#Zer0Con2025]
🎙️ SPEAKER Highlight: @azraelxuemo
"Who Moved My Account? OAuth Account Takeover Vulnerabilities in Many Famous Companies" 🚧
🎙️ SPEAKER Highlight: @azraelxuemo
"Who Moved My Account? OAuth Account Takeover Vulnerabilities in Many Famous Companies" 🚧

[#Zer0Con2025] Day1 Party! 🎉
Today, we exit() gracefully. No core dumps, just memories.
Enjoying Korean BBQ with awesome attendees from all around 🍖♨️🔥🥩🥓🍳
Today, we exit() gracefully. No core dumps, just memories.
Enjoying Korean BBQ with awesome attendees from all around 🍖♨️🔥🥩🥓🍳

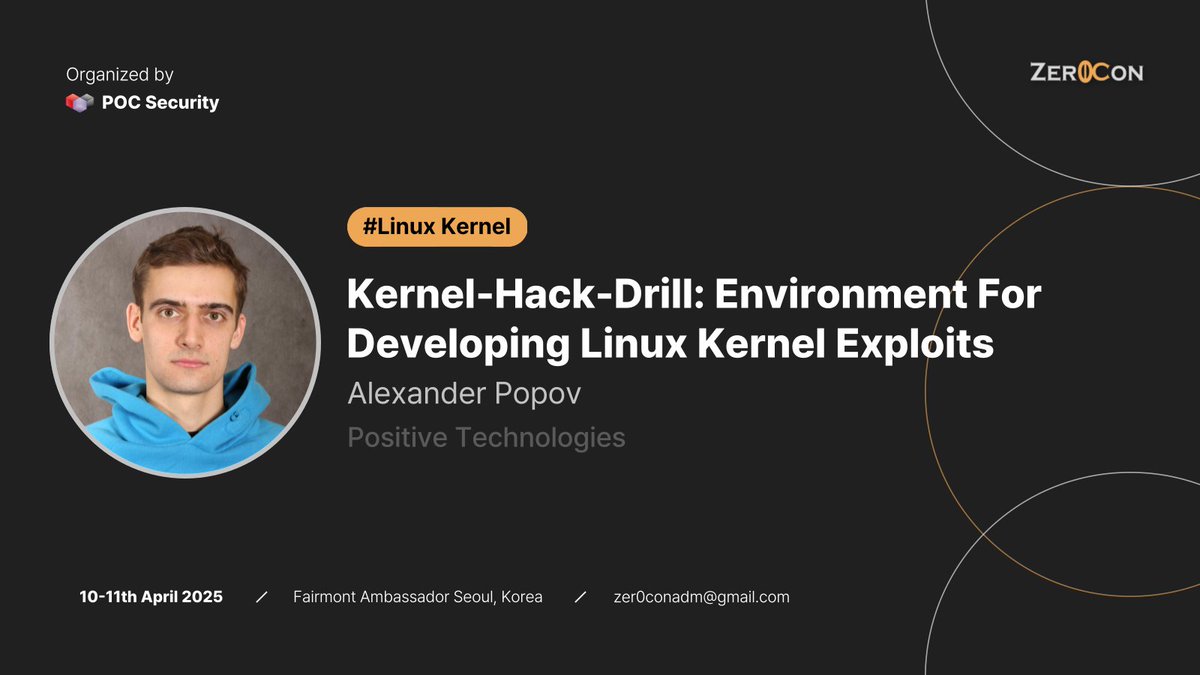
[#Zer0Con2025]
🎙️ SPEAKER Highlight: @a13xp0p0v
"Kernel-Hack-Drill: Environment For Developing Linux Kernel Exploits" 🐧
🎙️ SPEAKER Highlight: @a13xp0p0v
"Kernel-Hack-Drill: Environment For Developing Linux Kernel Exploits" 🐧

[#Zer0Con2025]
🎙️ SPEAKER Highlight: @slonser_
"Attacking Crypto Wallets: an In-Depth Look at Modern Browser Extension Security" 🥷
🎙️ SPEAKER Highlight: @slonser_
"Attacking Crypto Wallets: an In-Depth Look at Modern Browser Extension Security" 🥷

[#Zer0Con2025]
🎙️ SPEAKER Highlight: @ruikai
"Hardcore Inference Attack: Unraveling Llama.cpp’s RPC Heap Puzzle" 🦙
🎙️ SPEAKER Highlight: @ruikai
"Hardcore Inference Attack: Unraveling Llama.cpp’s RPC Heap Puzzle" 🦙

[#Zer0Con2025]
🎙️ SPEAKER Highlight: @R00tkitSMM
"Pishi Reloaded: Binary only address sanitizer for macOS KEXT." 🎣
🎙️ SPEAKER Highlight: @R00tkitSMM
"Pishi Reloaded: Binary only address sanitizer for macOS KEXT." 🎣

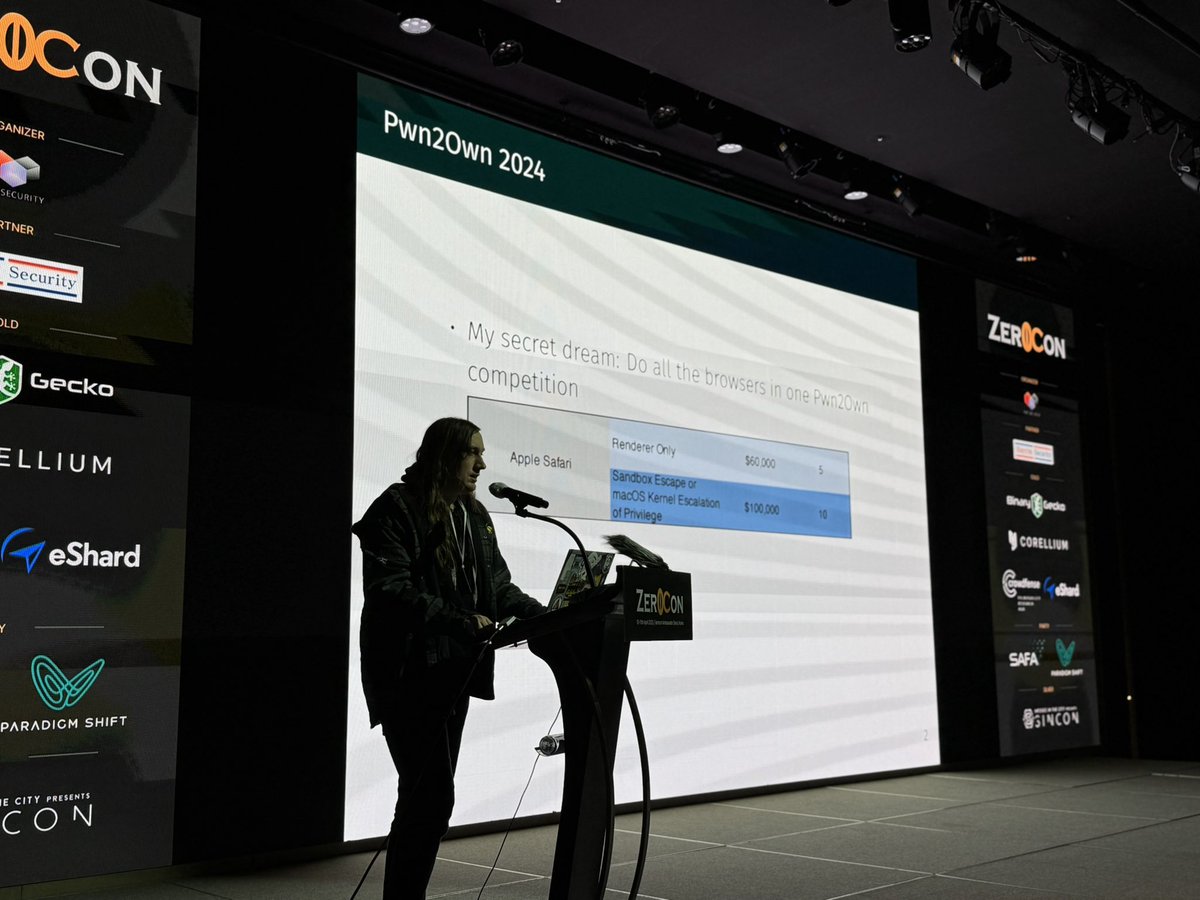
[#Zer0Con2025]
🎙️ SPEAKER Highlight: @_manfp
"PAC2Own: From Bug to Shellcode in modern Safari" 🌐
🎙️ SPEAKER Highlight: @_manfp
"PAC2Own: From Bug to Shellcode in modern Safari" 🌐
[#Zer0Con2025]
Packed, packed!
Just kicked off Day 1 conf 😎
Packed, packed!
Just kicked off Day 1 conf 😎

[#Zer0Con2025] Welcome Dinner with Early birds 🍽️
"Before we shared code, we shared the table"
Chilling with some Korean rice wine and local foods 😋
"Before we shared code, we shared the table"
Chilling with some Korean rice wine and local foods 😋

#Zer0Con2025 D-1

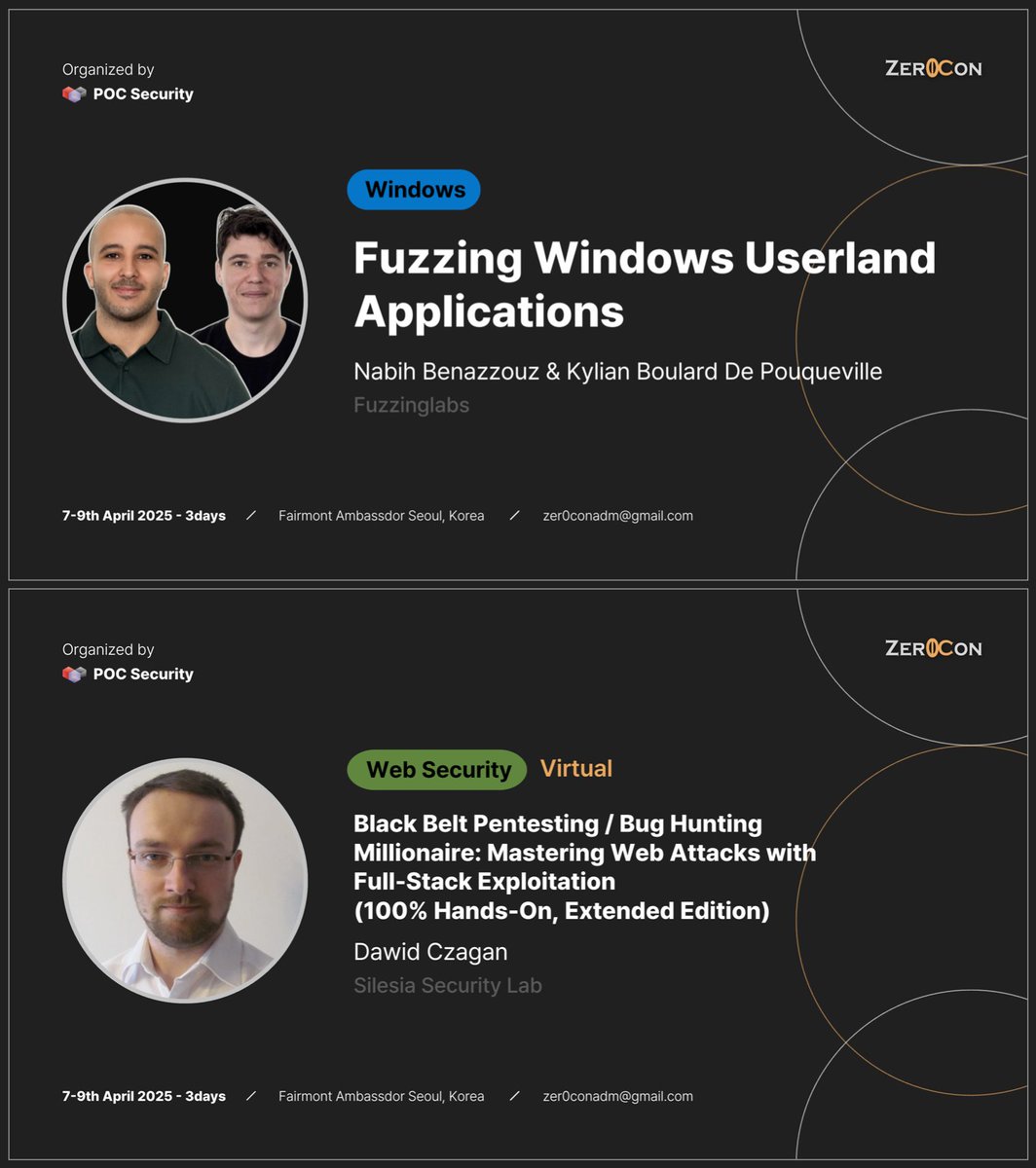
#Zer0Con2025 is getting closer, and the training sessions are going very smoothly.
👥 Nabih Benazzouz(@Raefko) & Kylian Boulard De Pouqueville(@0xKylm), “Fuzzing Windows Userland Applications” from @FuzzingLabs
👥 Nabih Benazzouz(@Raefko) & Kylian Boulard De Pouqueville(@0xKylm), “Fuzzing Windows Userland Applications” from @FuzzingLabs

[#Zer0Con2025] PARTY Sponsor 🥂🍹🍸🍷
Amazing sponsors we have for this edition's party
with amazing spot - another level
Featured by. @SAFATeamGmbH and @prdgmshift
Amazing sponsors we have for this edition's party
with amazing spot - another level
Featured by. @SAFATeamGmbH and @prdgmshift

GPT generated Ghibli vibed photo this is when @R00tkitSMM was speaking at #POC2024 🤣
It's dope! Thanks for featuring!
It's dope! Thanks for featuring!

[#Zer0Con2025] Gold Sponsor
Welcome aboard @eshard on a journey of Zer0Con! Much appreciated🙏
🔹Binary Analysis with Time Travel Analysis
🔹Chip Security testing Software
🔹Tools and Knowledge for security experts
Join us in shaping the future of cybersecurity. Explore
Welcome aboard @eshard on a journey of Zer0Con! Much appreciated🙏
🔹Binary Analysis with Time Travel Analysis
🔹Chip Security testing Software
🔹Tools and Knowledge for security experts
Join us in shaping the future of cybersecurity. Explore

[#Zer0Con2025] Gold Sponsor
@crowdfense is the go-to, trusted partner for top-tier zero-day exploits!
Submit your vulnerabilities through our VRH platform: https://t.co/1tlfJshcbh
We fuel offensive security. Are you in?🙌
@crowdfense is the go-to, trusted partner for top-tier zero-day exploits!
Submit your vulnerabilities through our VRH platform: https://t.co/1tlfJshcbh
We fuel offensive security. Are you in?🙌

[#Zer0Con2025] Gold Sponsor
@Binary_Gecko GmbH is an international security research company and the organizer of @offensive_con.
We offer our researchers:
🔹 An international and diverse company environment
🔹 Remote work options
🔹 The highest salaries in the industry
🔹
@Binary_Gecko GmbH is an international security research company and the organizer of @offensive_con.
We offer our researchers:
🔹 An international and diverse company environment
🔹 Remote work options
🔹 The highest salaries in the industry
🔹

[#Zer0Con2025] Gold Sponsor
We are with @CorelliumHQ once again at Zer0Con!
🔹 Enable mobile app security testing on virtualized hardware
🔹Automate OWASP testing & speed up routines by 50%
🔹 Seamlessly integrate with API & CLI tools
Come and say hi!👐
We are with @CorelliumHQ once again at Zer0Con!
🔹 Enable mobile app security testing on virtualized hardware
🔹Automate OWASP testing & speed up routines by 50%
🔹 Seamlessly integrate with API & CLI tools
Come and say hi!👐

[#Zer0Con2025] Silver Sponsor
SINCON 2025 is coming! 🚀#Zer0Con invites you to explore cutting-edge cybersecurity at SINCON 2025!
📅 22-23 May 2025 | 📍 voco Orchard, SG
💡 Use “SINCON25-SUPPORTER” for S$100 off!
🔗https://t.co/QiODpDIBMR
SINCON 2025 is coming! 🚀#Zer0Con invites you to explore cutting-edge cybersecurity at SINCON 2025!
📅 22-23 May 2025 | 📍 voco Orchard, SG
💡 Use “SINCON25-SUPPORTER” for S$100 off!
🔗https://t.co/QiODpDIBMR

#Zer0Con2025, Training
🗓️ Date: April 7-9, 2025
📍 Location: Fairmont Ambassador Seoul, South Korea
🔥 Don’t miss out on these unique opportunities to enhance your skills
Secure your spot now!(10% discounts on conference registration for those are registered for trainings)
➟
🗓️ Date: April 7-9, 2025
📍 Location: Fairmont Ambassador Seoul, South Korea
🔥 Don’t miss out on these unique opportunities to enhance your skills
Secure your spot now!(10% discounts on conference registration for those are registered for trainings)
➟
[#Zer0Con2025] 🌕Full line-up
Another great year for bug hunting and exploiting!
Proudly unveiling the complete line-up of speakers to rock at ZerCon2025.
This year, we're offering a broader spectrum of bug hunting and exploitation opportunities than ever before!
See you all
Another great year for bug hunting and exploiting!
Proudly unveiling the complete line-up of speakers to rock at ZerCon2025.
This year, we're offering a broader spectrum of bug hunting and exploitation opportunities than ever before!
See you all

[#Zer0Con2025] - SPEAKER 🔟
💁♂️@_manfp - PAC2Own: From Bug to Shellcode in modern Safari
💁♂️@_manfp - PAC2Own: From Bug to Shellcode in modern Safari

[#Zer0Con2025] - SPEAKER 9️⃣
💁♂️@ruikai - Hardcore Inference Attack: Unraveling Llama.cpp’s RPC Heap Puzzle
💁♂️@ruikai - Hardcore Inference Attack: Unraveling Llama.cpp’s RPC Heap Puzzle

[#Zer0Con2025] - SPEAKER 8️⃣
💁♂️@a13xp0p0v - Kernel-Hack-Drill: Environment For Developing Linux Kernel Exploits
💁♂️@a13xp0p0v - Kernel-Hack-Drill: Environment For Developing Linux Kernel Exploits
[#Zer0Con2025] - SPEAKER 7️⃣
💁♂️@slonser_ - Attacking Crypto Wallets: an In-Depth Look at Modern Browser Extension Security
💁♂️@slonser_ - Attacking Crypto Wallets: an In-Depth Look at Modern Browser Extension Security

[#Zer0Con2025] - SPEAKER 6⃣
💁♂️@josephtlucas - Vulnerability Research and Mitigation in AI Applications
💁♂️@josephtlucas - Vulnerability Research and Mitigation in AI Applications

[#Zer0Con2025] - SPEAKER 1⃣
💁♂️@R00tkitSMM - Pishi Reloaded: Binary only address sanitizer for macOS KEXT
💁♂️@R00tkitSMM - Pishi Reloaded: Binary only address sanitizer for macOS KEXT

[#Zer0Con2025] - SPEAKER5⃣
💁♂️ @matteomalvica - Breaking Chrome's V8: Type confusion, WASM JIT-Spraying and Heap Sandbox Evasion
💁♂️ @matteomalvica - Breaking Chrome's V8: Type confusion, WASM JIT-Spraying and Heap Sandbox Evasion

[#Zer0Con2025] - SPEAKER 4⃣
👬 Bryton Bernard & Mathieu Hoste from @FuzzingLabs - Ethereum's Achilles' Heel : Attacking and Fuzzing EVMs for FUN(and Profits)
👬 Bryton Bernard & Mathieu Hoste from @FuzzingLabs - Ethereum's Achilles' Heel : Attacking and Fuzzing EVMs for FUN(and Profits)

[#Zer0Con2025] - SPEAKER 3⃣
💁♂️@azraelxuemo - Who Moved My Account? OAuth Account Takeover Vulnerabilities in "Many Famous Companies"
💁♂️@azraelxuemo - Who Moved My Account? OAuth Account Takeover Vulnerabilities in "Many Famous Companies"

[#Zer0Con2025] - SPEAKER 2⃣
👨👦👦 @zhz__6951/@zblee_/@Mr_LiuYue - vCenter Lost: How the DCERPC vulnerabilities Changed the Fate of ESXi
👨👦👦 @zhz__6951/@zblee_/@Mr_LiuYue - vCenter Lost: How the DCERPC vulnerabilities Changed the Fate of ESXi
Few hours left until CFP closes!
We will be taking more edge CPFs for few days so if you have not submitted yours yet, now is the final call😎
AND
We will be releasing 1st line-up of Zer0Con this week!
Stay tuned🤜
#Zer0con2025
We will be taking more edge CPFs for few days so if you have not submitted yours yet, now is the final call😎
AND
We will be releasing 1st line-up of Zer0Con this week!
Stay tuned🤜
#Zer0con2025
Roughly 2 weeks left until #Zer0Con2025 CFP deadline
Interesting hardcore topics are coming through ☑️
And we looking for Ai, Aerospace, Browser, Blockchain, Web3, related topics!
Hop on the ship, let's sail out the history together!
🌕 CFP: until 5th March
Interesting hardcore topics are coming through ☑️
And we looking for Ai, Aerospace, Browser, Blockchain, Web3, related topics!
Hop on the ship, let's sail out the history together!
🌕 CFP: until 5th March

🫶 Special shoutout to @FuzzySec & @chompie1337 for supporting Korean security students by sponsoring and CTF challenges. 🎯💡 We have been running this camp in South Korea as a for 15 years, helping the community grow! 💜👏




🔥Unlock your potential with our expert-led training sessions at #Zer0Con2025!🔥
1️⃣ Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation (100% Hands-On, Extended Edition) by @dawidczagan
Dig into web attacks and full-stack
1️⃣ Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation (100% Hands-On, Extended Edition) by @dawidczagan
Dig into web attacks and full-stack



🥰We sincerely appreciate Ruben(@FuzzySec) & Valentina(@chompie1337) from the IBM XOR TEAM for their support of HackingCamp!
🔥HackingCamp is a non-profit event that we have been running for 15 years to support students studying cybersecurity in Korea.
Their contributions as a
🔥HackingCamp is a non-profit event that we have been running for 15 years to support students studying cybersecurity in Korea.
Their contributions as a

So proud of our buddy @0x10n for making waves at CMU! He's been featured for his outstanding contributions to cybersecurity!
[Zer0Con2024] TRAINING
"Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation
(100% Hands-On, Extended Edition)" by @dawidczagan
🗓️Date: 7th April ~ 9th April 2025 (3 DAYS)
- Fairmont Ambassador Seoul, South Korea
Sign up:
"Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation
(100% Hands-On, Extended Edition)" by @dawidczagan
🗓️Date: 7th April ~ 9th April 2025 (3 DAYS)
- Fairmont Ambassador Seoul, South Korea
Sign up:

[Zer0Con2024] TRAINING
"Fuzzing Windows Userland Applications" by Nabih Benazzouz & Kylian Boulard De Pouqueville
🗓️Date: 7th April ~ 9th April 2025 (3 DAYS)
- Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/OgoRfjNDvO
#Zer0Con2025
"Fuzzing Windows Userland Applications" by Nabih Benazzouz & Kylian Boulard De Pouqueville
🗓️Date: 7th April ~ 9th April 2025 (3 DAYS)
- Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/OgoRfjNDvO
#Zer0Con2025

[Zer0Con2024] TRAINING
"Fuzzing the Linux Kernel" by @andreyknvl
🗓️Date: 7th April ~ 9th April 2025 (3 DAYS)
- Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/OgoRfjNDvO
#Zer0Con2025
"Fuzzing the Linux Kernel" by @andreyknvl
🗓️Date: 7th April ~ 9th April 2025 (3 DAYS)
- Fairmont Ambassador Seoul, South Korea
Sign up: https://t.co/OgoRfjNDvO
#Zer0Con2025

[#Zer0con2025] - Registration is ON!
🌕Conference: 100 seats available (when reached, registration will automatically close down)
🌕Training: until maximum capacity filled
Sign up: https://t.co/2HQVEh8g5s
Looking forward to seeing you all there!
🌕Conference: 100 seats available (when reached, registration will automatically close down)
🌕Training: until maximum capacity filled
Sign up: https://t.co/2HQVEh8g5s
Looking forward to seeing you all there!

[#Zer0Con2025] - Announcements
'Challenge the norms, break boundaries'
Zer0Con2025 CFP / CFT is officially opened
📅Date: 10~11th April 2025
🏩 Venue: Fairmont Ambassdor Seoul, South Korea
🎟️Entry badge: 100 available
🌖 CFT status: Partially open due to limited space
🌕CFP
'Challenge the norms, break boundaries'
Zer0Con2025 CFP / CFT is officially opened
📅Date: 10~11th April 2025
🏩 Venue: Fairmont Ambassdor Seoul, South Korea
🎟️Entry badge: 100 available
🌖 CFT status: Partially open due to limited space
🌕CFP

[#POC2024] Slides are up NOW!
https://t.co/BXqF1wYUIO
Note that blank spaces will be updated shortly with the latest version of the slides 😘
https://t.co/BXqF1wYUIO
Note that blank spaces will be updated shortly with the latest version of the slides 😘

[POC2024] Charity Donation
Thank you @alexbirnberg for donating his honorarium to the charity! Massive thanks for his action towards helping the needs.
#POC2024
Thank you @alexbirnberg for donating his honorarium to the charity! Massive thanks for his action towards helping the needs.
#POC2024

Thank You Everyone!
We are sincerely grateful to all who attended #POC2024. Your participation and support were invaluable, and your contributions made this event a success! Thank you for bringing your knowledge, insights, and energy to us. We look forward to welcoming you on our
We are sincerely grateful to all who attended #POC2024. Your participation and support were invaluable, and your contributions made this event a success! Thank you for bringing your knowledge, insights, and energy to us. We look forward to welcoming you on our




2nd round party(Sponsored by @dfsec_com). Thanks a lot!! 🥳🥳

#POC2024
Are you guys ready? @dfsec_com
Are you guys ready? @dfsec_com


#POC2024
Pan Zhenpeng & Jheng Bing Jhong(@Peterpan980927, @st424204)
GPUAF : Two ways of rooting All Qualcomm based Android phones 🔫
Pan Zhenpeng & Jheng Bing Jhong(@Peterpan980927, @st424204)
GPUAF : Two ways of rooting All Qualcomm based Android phones 🔫


#POC2024
Meysam Firouzi(@R00tkitSMM)
Pishi: Coverage-Guided Fuzzing of the XNU Kernel and Arbitrary KEXT 🚧
Meysam Firouzi(@R00tkitSMM)
Pishi: Coverage-Guided Fuzzing of the XNU Kernel and Arbitrary KEXT 🚧


#POC2024
Jaewon Min & Kaan Ezder(@binerdd, @kaanezder)
Fake it till you make it: Bypassing V8 Sandbox by constructing a fake Isolate 🏎
Jaewon Min & Kaan Ezder(@binerdd, @kaanezder)
Fake it till you make it: Bypassing V8 Sandbox by constructing a fake Isolate 🏎


#POC2024
Andrey Konovalov(@andreyknvl)
Lights Out: Covertly turning off the ThinkPad webcam LED indicator ⚡️
Andrey Konovalov(@andreyknvl)
Lights Out: Covertly turning off the ThinkPad webcam LED indicator ⚡️


#POC2024
Haidar Kabibo(@haider_kabibo)
A journey into forgotten Null Session and MS-RPC interfaces 😉
Haidar Kabibo(@haider_kabibo)
A journey into forgotten Null Session and MS-RPC interfaces 😉


#POC2024
Csaba Fitzl(@theevilbit)
Apple Disk-O Party 🍎
Csaba Fitzl(@theevilbit)
Apple Disk-O Party 🍎


#POC2024
Hanqin Ling & Yutao Lu
Breaking through the cage: Get Android Universal Root by B-PUAF ☄️
Hanqin Ling & Yutao Lu
Breaking through the cage: Get Android Universal Root by B-PUAF ☄️


#POC2024
Party and party 🥂
Party and party 🥂




#POC2024
History begins, starts now!
History begins, starts now!

#POC2024
Day-1 party begins by @pksecurity_io
You will never know if you aren't here😝
Day-1 party begins by @pksecurity_io
You will never know if you aren't here😝

#POC2024
Sagi Tzadik(@sagitz_) - Uncovering Multitenancy Issues in AI-as-a-Service Providers 🦾
Sagi Tzadik(@sagitz_) - Uncovering Multitenancy Issues in AI-as-a-Service Providers 🦾


#POC2024
Alex Birnberg(@alexbirnberg) - Cloudy with a Chance of Bugs: Attacking the Windows Cloud Files API ☁️
Alex Birnberg(@alexbirnberg) - Cloudy with a Chance of Bugs: Attacking the Windows Cloud Files API ☁️
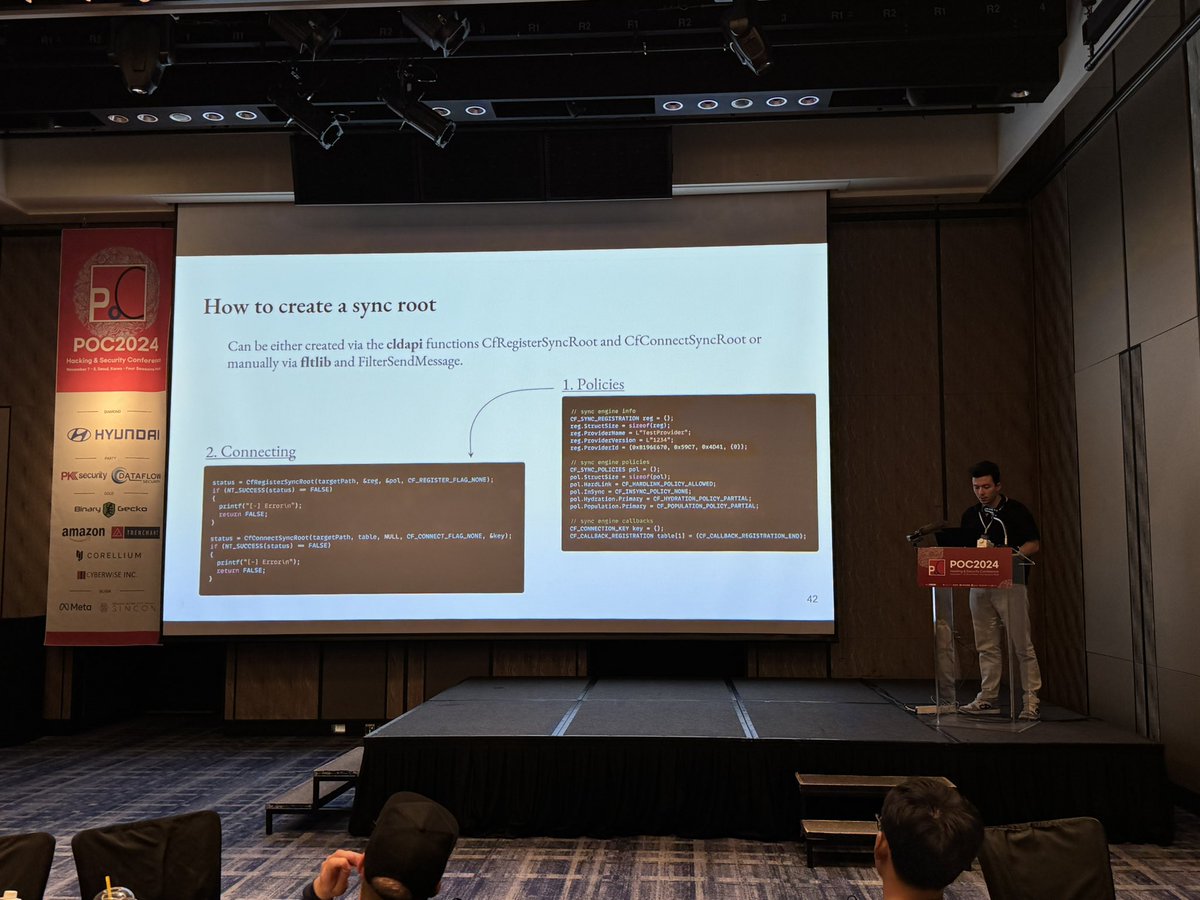

@0x10n nailed it😎
#POC2024
Heyi Wu - AI-Based Generation of Adversarial Malicious ELF Samples 🤖
Heyi Wu - AI-Based Generation of Adversarial Malicious ELF Samples 🤖
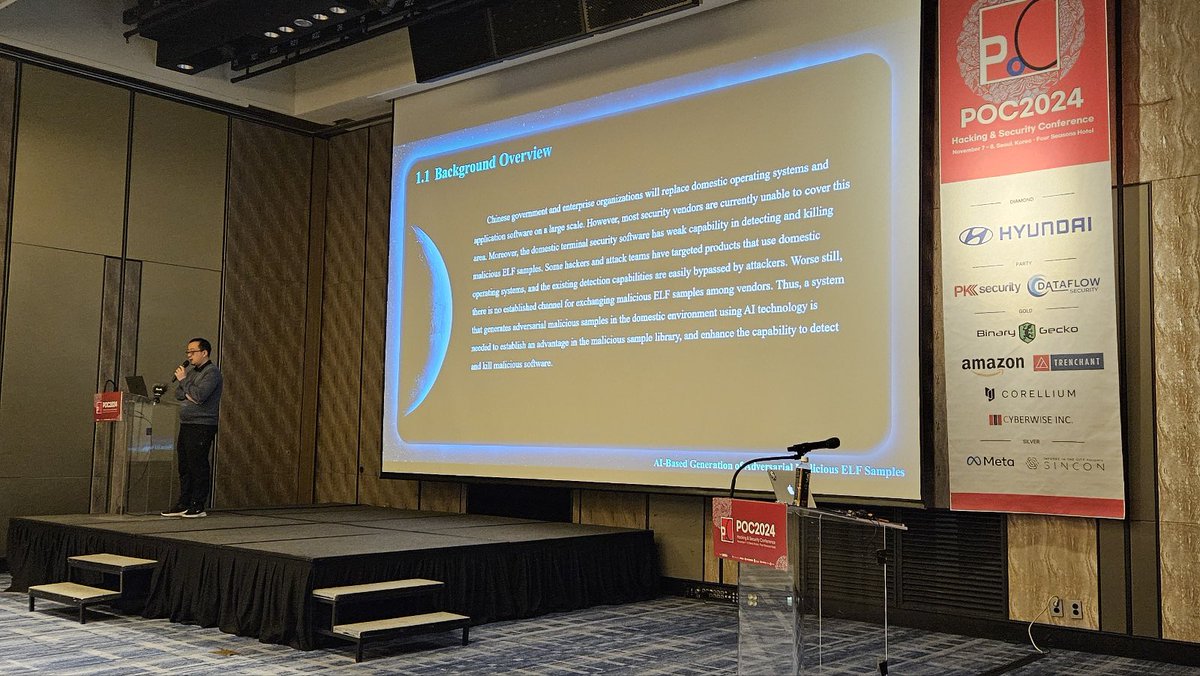

#POC2024
Chih-Yen Chang(@u1f383) - How I use a novel approach to exploit a limited OOB on Ubuntu at Pwn2Own Vancouver 2024 🤩
Chih-Yen Chang(@u1f383) - How I use a novel approach to exploit a limited OOB on Ubuntu at Pwn2Own Vancouver 2024 🤩


#POC2024
Seunghyun Lee(@0x10n) - WebAssembly Is All You Need: Exploiting Chrome and the V8 Sandbox 10+ times with WASM 🇰🇷
Seunghyun Lee(@0x10n) - WebAssembly Is All You Need: Exploiting Chrome and the V8 Sandbox 10+ times with WASM 🇰🇷

#POC2024
Zhaofeng Chen - A Single Transaction to Rule Them All: Attacking Blockchain Validators 👍
Zhaofeng Chen - A Single Transaction to Rule Them All: Attacking Blockchain Validators 👍


#POC2024
Nguyễn Hoàng Thạch(@hi_im_d4rkn3ss) - VMware Workstation: Escaping via a New Route - Virtual Bluetooth 😆
Nguyễn Hoàng Thạch(@hi_im_d4rkn3ss) - VMware Workstation: Escaping via a New Route - Virtual Bluetooth 😆


#POC2024
Mickey Jin(@patch1t) - "A New Era of macOS Sandbox Escapes: Diving into an Overlooked Attack Surface and Uncovering 10+ New Vulnerabilities"😆
Mickey Jin(@patch1t) - "A New Era of macOS Sandbox Escapes: Diving into an Overlooked Attack Surface and Uncovering 10+ New Vulnerabilities"😆
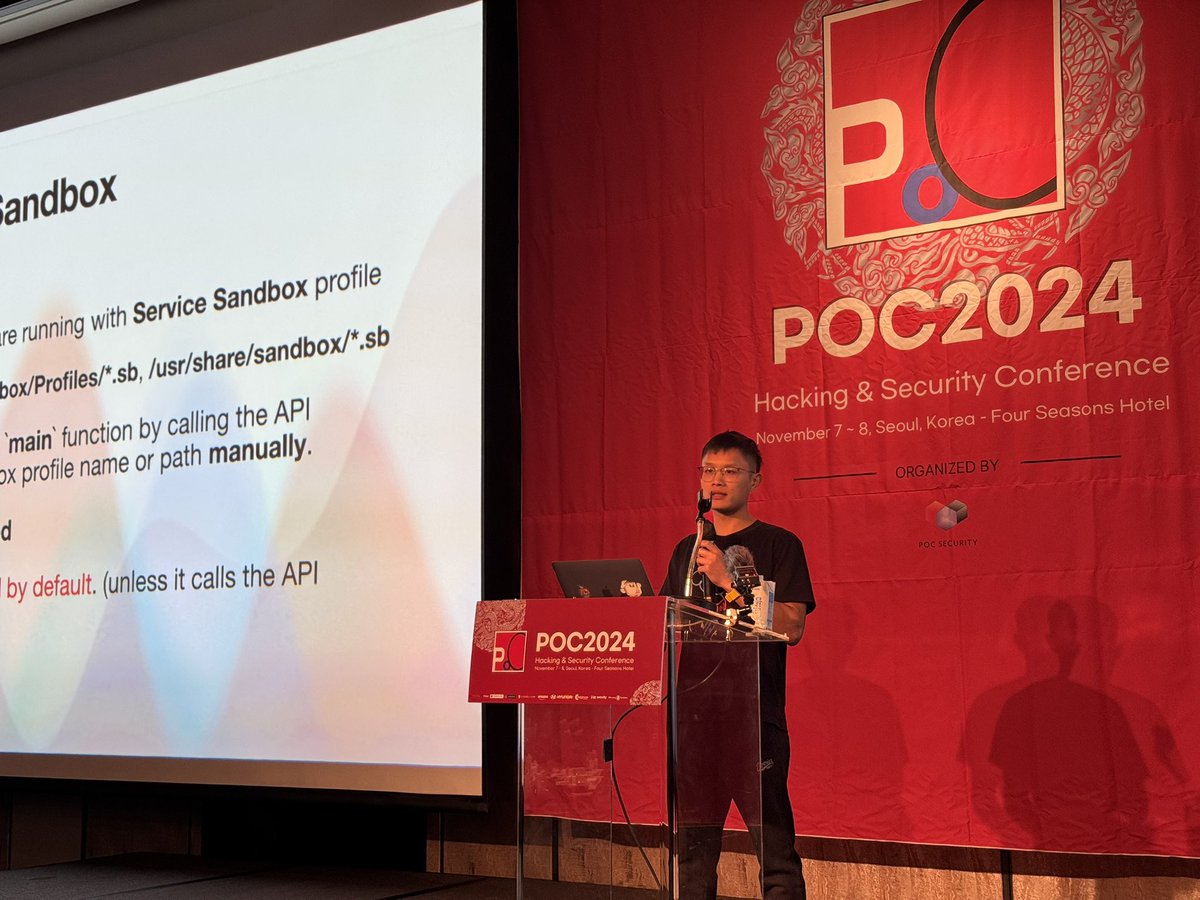

#POC2024
Carl smith(@cffsmith) - Fuzzing for complex bugs across languages in JavaScript Engines 🏎️
Carl smith(@cffsmith) - Fuzzing for complex bugs across languages in JavaScript Engines 🏎️


#POC2024 Ding-Dong 😎
Kicking off with @qwertyoruiopz with Keynote speech. We are fully packed
Kicking off with @qwertyoruiopz with Keynote speech. We are fully packed




Pre-drinks before initiating.
Thanks to @Binary_Gecko for the gifts:)
Gecko mode ready tomorrow😝
#POC2024
Thanks to @Binary_Gecko for the gifts:)
Gecko mode ready tomorrow😝
#POC2024

Ready for the conference ✅ #POC2024

[#POC2024 Training]
👥 @DrCh40s & @t0nvi - Modern Malware OPSEC & Anti-Reverse Technique Implementation and Reversing
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
👥 @DrCh40s & @t0nvi - Modern Malware OPSEC & Anti-Reverse Technique Implementation and Reversing
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea

[#POC2024 Training]
👤 @hardik05 - Practical Fuzzing
A Hands-On Learning Experience for Uncovering Vulnerabilities on Linux and Windows Platforms
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
👤 @hardik05 - Practical Fuzzing
A Hands-On Learning Experience for Uncovering Vulnerabilities on Linux and Windows Platforms
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea

Somaek (Soju and Beer) with the #POC2024 trainers! 🍻🥂
@DrCh40s & @t0nvi & @hardik05
@DrCh40s & @t0nvi & @hardik05

[POC2024] Diamond Sponsor
Thank you @hyundai_kor for sponsoring the conference!
“Driving Innovation : At the Forefront of Automotive Cybersecurity”
#POC2024
Thank you @hyundai_kor for sponsoring the conference!
“Driving Innovation : At the Forefront of Automotive Cybersecurity”
#POC2024

[POC2024] SPEAKER UPDATE - KEYNOTE
👤 @qwertyoruiopz - "An insider perspective on the offensive industry"
#POC2024
👤 @qwertyoruiopz - "An insider perspective on the offensive industry"
#POC2024

[POC2024] DAY-2 PARTY Sponsor
Ready for Day 2 Party? 🍻
@dfsec_com is making it happen again!
#POC2024
Ready for Day 2 Party? 🍻
@dfsec_com is making it happen again!
#POC2024

[POC2024] DAY-1 PARTY Sponsor
Thank you @pksecurity_io for sponsoring the conference!
"PKSecurity is cyber security company based in South Korea. We are focusing on various vulnerability research and looking forward to various collaborations"
#POC2024
Thank you @pksecurity_io for sponsoring the conference!
"PKSecurity is cyber security company based in South Korea. We are focusing on various vulnerability research and looking forward to various collaborations"
#POC2024

[POC2024] Gold Sponsor
Thank you @Binary_Gecko for sponsoring the conference!
Binary Gecko, the organizers of @offensive_con is a research-driven cyber security company focusing on vulnerability research and they are HIRING!
#POC2024
Thank you @Binary_Gecko for sponsoring the conference!
Binary Gecko, the organizers of @offensive_con is a research-driven cyber security company focusing on vulnerability research and they are HIRING!
#POC2024

[POC2024] Gold Sponsor
Thank you @CorelliumHQ for sponsoring the conference!
The R&D platform for the next generation of smart devices – iOS, Android, and Arm. Faster development, better security testing, and lower costs.
#POC2024
Thank you @CorelliumHQ for sponsoring the conference!
The R&D platform for the next generation of smart devices – iOS, Android, and Arm. Faster development, better security testing, and lower costs.
#POC2024

[POC2024] Gold Sponsor
Thank you @TrenchantARC for sponsoring the conference! Ready to tackle hardcore challenges?
They are HIRING!
#POC2024
Thank you @TrenchantARC for sponsoring the conference! Ready to tackle hardcore challenges?
They are HIRING!
#POC2024

[POC2024] Gold Sponsor
Thank you @amazon for sponsoring the conference!
Thrilled to have Amazon with us for the first time! Excited for what we can accomplish together.
#POC2024
Thank you @amazon for sponsoring the conference!
Thrilled to have Amazon with us for the first time! Excited for what we can accomplish together.
#POC2024

[POC2024] Gold Sponsor
Thank you CYBERWISE INC. for sponsoring the conference. Looking forward to our collaboration and future projects.
#POC2024
Thank you CYBERWISE INC. for sponsoring the conference. Looking forward to our collaboration and future projects.
#POC2024

[POC2024] Silver Sponsor
Thank you @Meta for sponsoring the conference!
Allowing us to pursue greater innovation and challenges. Excited to have you back again:)
#POC2024
Thank you @Meta for sponsoring the conference!
Allowing us to pursue greater innovation and challenges. Excited to have you back again:)
#POC2024

[POC2024] Silver Sponsor
Thank you @Infosec_City for sponsoring the conference! Looking forward to our collaboration.
#POC2024
Thank you @Infosec_City for sponsoring the conference! Looking forward to our collaboration.
#POC2024

[POC2024] TICKETS SOLD OUT
All available slots are sold out early this year.
We really can't take more demands for the conference tickets from now on.
The final keynote speaker will be announced at a later time.
Thanks everyone for your interest and see you very soon!🙏
All available slots are sold out early this year.
We really can't take more demands for the conference tickets from now on.
The final keynote speaker will be announced at a later time.
Thanks everyone for your interest and see you very soon!🙏

[POC2024] SPEAKER UPDATE 1⃣6⃣
👥 Hanqin Ling & Yutao Lu - "Breaking through the cage: Get Android Universal Root by B-PUAF"
#POC2024
👥 Hanqin Ling & Yutao Lu - "Breaking through the cage: Get Android Universal Root by B-PUAF"
#POC2024

[POC2024] SPEAKER UPDATE 1⃣5⃣
👥 @binerdd & @kaanezder - "Fake it till you make it: Bypassing V8 Sandbox by constructing a fake Isolate"
#POC2024
👥 @binerdd & @kaanezder - "Fake it till you make it: Bypassing V8 Sandbox by constructing a fake Isolate"
#POC2024

[POC2024] SPEAKER UPDATE 1⃣4⃣
👤 @cffsmith - "Fuzzing for complex bugs across languages in JavaScript Engines"
#POC2024
👤 @cffsmith - "Fuzzing for complex bugs across languages in JavaScript Engines"
#POC2024

[POC2024] SPEAKER UPDATE 1⃣3⃣
👤@alexbirnberg - "Cloudy with a Chance of Bugs: Attacking the Windows Cloud Files API"
#POC2024
👤@alexbirnberg - "Cloudy with a Chance of Bugs: Attacking the Windows Cloud Files API"
#POC2024

[POC2024] SPEAKER UPDATE 1⃣2⃣
👤 @sagitz_ - "Uncovering Multitenancy Issues in AI-as-a-Service Providers"
#POC2024
👤 @sagitz_ - "Uncovering Multitenancy Issues in AI-as-a-Service Providers"
#POC2024

Already feel so empty after coming back from Hexacon.
@hexacon_fr It is indeed you guys did a great job again with another successful edition. You all deserve a long lasting rest!
Thanks again for accommodating such fantastic event!
@hexacon_fr It is indeed you guys did a great job again with another successful edition. You all deserve a long lasting rest!
Thanks again for accommodating such fantastic event!

[POC2024] SPEAKER UPDATE 🔟
👥@Peterpan980927 & @st424204 - "GPUAF : Two ways of rooting All Qualcomm based Android phones"
#POC2024
👥@Peterpan980927 & @st424204 - "GPUAF : Two ways of rooting All Qualcomm based Android phones"
#POC2024

Just released the 1st line-up of speakers for upcoming #POC2024 💪💪
For more:
For more:
[POC2024] SPEAKER UPDATE 1⃣1⃣
👤 @patch1t - "A New Era of macOS Sandbox Escapes: Diving into an Overlooked Attack Surface and Uncovering 10+ New Vulnerabilities"
#POC2024
👤 @patch1t - "A New Era of macOS Sandbox Escapes: Diving into an Overlooked Attack Surface and Uncovering 10+ New Vulnerabilities"
#POC2024

[POC2024] SPEAKER UPDATE 9⃣
👤 @0x10n - "WebAssembly Is All You Need: Exploiting Chrome and the V8 Sandbox 10+ times with WASM"
#POC2024
👤 @0x10n - "WebAssembly Is All You Need: Exploiting Chrome and the V8 Sandbox 10+ times with WASM"
#POC2024
[POC2024] SPEAKER UPDATE 8⃣
👤 @hi_im_d4rkn3ss - "VMware Workstation: Escaping via a New Route - Virtual Bluetooth"
#POC2024
👤 @hi_im_d4rkn3ss - "VMware Workstation: Escaping via a New Route - Virtual Bluetooth"
#POC2024
[POC2024] SPEAKER UPDATE 7⃣
👤 @R00tkitSMM - "Pishi: Coverage-Guided Fuzzing of the XNU Kernel and Arbitrary KEXT"
#POC2024
👤 @R00tkitSMM - "Pishi: Coverage-Guided Fuzzing of the XNU Kernel and Arbitrary KEXT"
#POC2024

[POC2024] SPEAKER UPDATE 6⃣
👤@andreyknvl - "Lights Out: Covertly turning off the ThinkPad webcam LED indicator"
#POC2024
👤@andreyknvl - "Lights Out: Covertly turning off the ThinkPad webcam LED indicator"
#POC2024
Find us! 👋🏻 #defcon32

🛫 We're heading to Las Vegas soon!
If you're curious about the #POC2024 conference this November, feel free to reach out to us! 👋🏻
If you're curious about the #POC2024 conference this November, feel free to reach out to us! 👋🏻

[POC2024] SPEAKER UPDATE 5⃣
👤Zhaofeng Chen - "A Single Transaction to Rule Them All: Attacking Blockchain Validators"
#POC2024
👤Zhaofeng Chen - "A Single Transaction to Rule Them All: Attacking Blockchain Validators"
#POC2024
[POC2024] SPEAKER UPDATE 4⃣
👤Heyi Wu - "AI-Based Generation of Adversarial Malicious ELF Samples"
#POC2024
👤Heyi Wu - "AI-Based Generation of Adversarial Malicious ELF Samples"
#POC2024

[POC2024] SPEAKER UPDATE 3⃣
👤@haider_kabibo - "A journey into forgotten Null Session and MS-RPC interaces"
#POC2024
👤@haider_kabibo - "A journey into forgotten Null Session and MS-RPC interaces"
#POC2024
[POC2024] SPEAKER UPDATE 2⃣
👤 @u1f383 - "How I use a novel approach to exploit a limited OOB on Ubuntu at Pwn2Own Vancouver 2024"
#POC2024
👤 @u1f383 - "How I use a novel approach to exploit a limited OOB on Ubuntu at Pwn2Own Vancouver 2024"
#POC2024

[POC2024] SPEAKER UPDATE 1⃣
👤 @theevilbit - "Apple Disk-O Party"
#POC2024
👤 @theevilbit - "Apple Disk-O Party"
#POC2024

[#POC2024 Training]
👤 @dawidczagan - Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation (Extended)
📅Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️Registration ends on the "20th Sept"
👤 @dawidczagan - Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation (Extended)
📅Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️Registration ends on the "20th Sept"

[#POC2024 Training]
👥 @DrCh40s & @t0nvi - Modern Malware OPSEC & Anti-Reverse Technique Implementation and Reversing
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️ Registration ends on the "20th Sept"
👥 @DrCh40s & @t0nvi - Modern Malware OPSEC & Anti-Reverse Technique Implementation and Reversing
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️ Registration ends on the "20th Sept"

[#POC2024 Training]
👤 @pulsoid & @tieknimmers - The Art of Fault Injection: Advanced Techniques & Attacks
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️Registration ends on the "20th Sept"
👤 @pulsoid & @tieknimmers - The Art of Fault Injection: Advanced Techniques & Attacks
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️Registration ends on the "20th Sept"

[#POC2024 Training]
👤 @hardik05 - Practical Fuzzing
A Hands-On Learning Experience for Uncovering Vulnerabilities on Linux and Windows Platforms
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️Registration ends on the "20th Sept"
👤 @hardik05 - Practical Fuzzing
A Hands-On Learning Experience for Uncovering Vulnerabilities on Linux and Windows Platforms
📅 Date: 4th ~ 6th Nov (3days)
🇰🇷 Venue: Four Seasons Hotel, Seoul, South Korea
‼️Registration ends on the "20th Sept"

[#POC2024 NOTICE]
⏰Date: 7-8th November, 2024
🇰🇷Venue: Four Seasons Hotel, Seoul, South Korea
🎟️Registration: 2nd Sept ~
[CFP & CFT is opened]
CFP - until 5th Oct
CFT - until 31st July
For more: https://t.co/bd1GAHfois
⏰Date: 7-8th November, 2024
🇰🇷Venue: Four Seasons Hotel, Seoul, South Korea
🎟️Registration: 2nd Sept ~
[CFP & CFT is opened]
CFP - until 5th Oct
CFT - until 31st July
For more: https://t.co/bd1GAHfois

It's always sad to leave friends behind. Such a short time to enjoy really.
Congrats on another successful conference @offensive_con . Your conference and the hospitality was amazing as always😍 We shall see you all in POC on November:)
Have a safe trip back home everyone!
Congrats on another successful conference @offensive_con . Your conference and the hospitality was amazing as always😍 We shall see you all in POC on November:)
Have a safe trip back home everyone!



Heading out to Berlin for some fun!
See you around at @offensive_con!
Keep us posted if you are there:)
Always looking foward to see @LukasHermannBFS and have decent chat around🙌
See you around at @offensive_con!
Keep us posted if you are there:)
Always looking foward to see @LukasHermannBFS and have decent chat around🙌

Pew, just came back to work from the long journey.
Thanks everyone for making another great success on #Zer0Con2024! Wish you all safe travel back home and most importantly take a good rest!
We will be around at the @offensive_con, if you are there, let's grab a drink 🙌
Thanks everyone for making another great success on #Zer0Con2024! Wish you all safe travel back home and most importantly take a good rest!
We will be around at the @offensive_con, if you are there, let's grab a drink 🙌




#Zer0Con2024
Endless party. ☠️
Day2 sponsored by @dfsec_com
(🤫 This is the second round)
Endless party. ☠️
Day2 sponsored by @dfsec_com
(🤫 This is the second round)


[#Zer0con2024]
Thank you for decorating the last talk of the conference!
@Dawuge3
"A Deep Dive in Android closed-source ROMs"
Thank you for decorating the last talk of the conference!
@Dawuge3
"A Deep Dive in Android closed-source ROMs"
[#Zer0Con2024]
Hard wallets are not hard as you think
@0xslipper, @nwmonster, @Offside_Labs
"Revealing One Key Security Insight for Hardware Wallets"
Hard wallets are not hard as you think
@0xslipper, @nwmonster, @Offside_Labs
"Revealing One Key Security Insight for Hardware Wallets"

[#Zer0con2024]
@0x3C3E
"The Userland Maze — Revealing macOS's Logic Bugs and Security Bypasses"
@0x3C3E
"The Userland Maze — Revealing macOS's Logic Bugs and Security Bypasses"

[#Zer0Con2024]
Very interesting technique and hardcore
Jinbum Park 🇰🇷
"Bypassing ARM MTE with Speculative Execution"
Very interesting technique and hardcore
Jinbum Park 🇰🇷
"Bypassing ARM MTE with Speculative Execution"
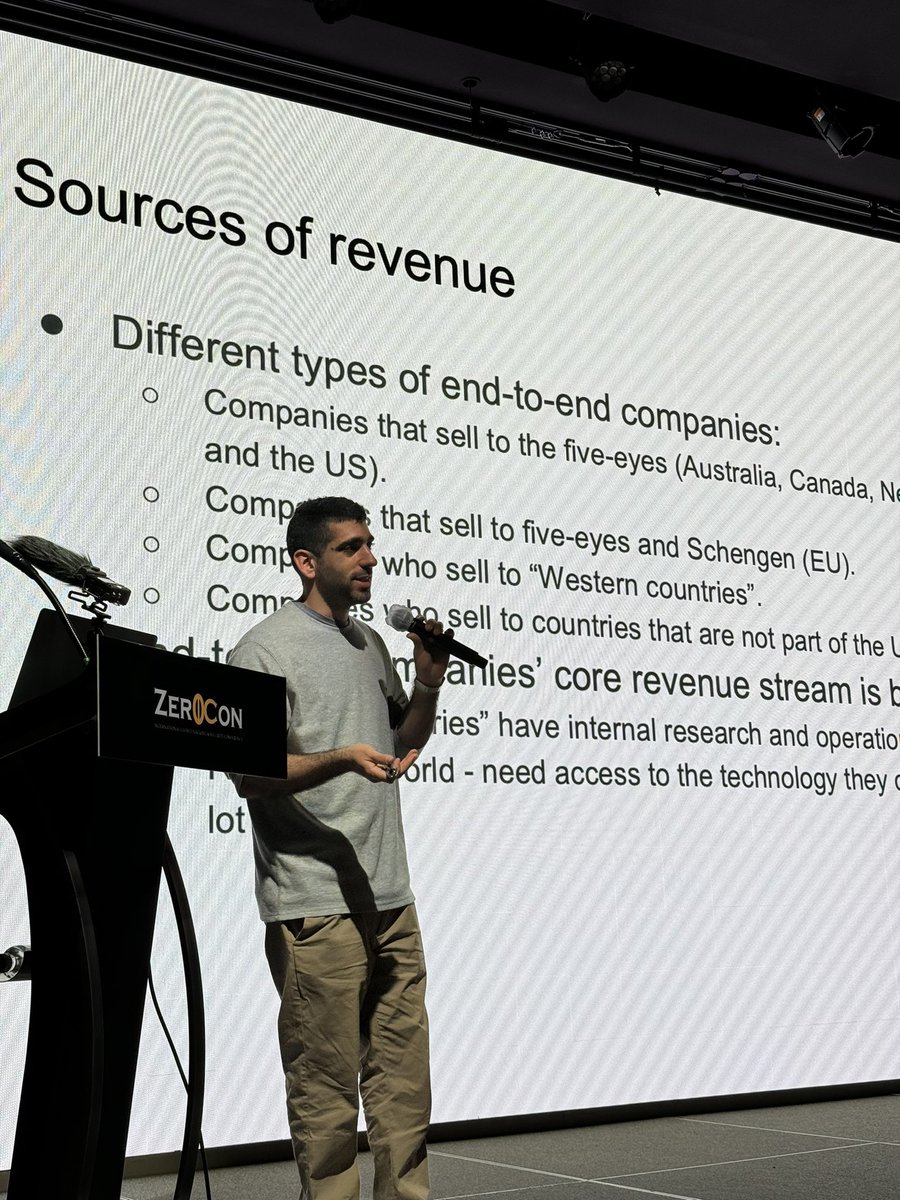
[#Zer0Con2024]
Day2 kicks off with
@malltos92
"The Boom, the bust, the adjust and the unknown"
Day2 kicks off with
@malltos92
"The Boom, the bust, the adjust and the unknown"
#Zer0Con2024
His research will bring great light this year 🎆
Mingi Cho 🇰🇷 of @theori_io
"Exploiting a Missed Linux Kernel Patch in a KernelCTF Instance"
His research will bring great light this year 🎆
Mingi Cho 🇰🇷 of @theori_io
"Exploiting a Missed Linux Kernel Patch in a KernelCTF Instance"
#Zer0con2024
He has a cool DEMO 😎
@cr0wtom
"Back to the Future: Old Vulnerabilities Becoming New Again"
He has a cool DEMO 😎
@cr0wtom
"Back to the Future: Old Vulnerabilities Becoming New Again"


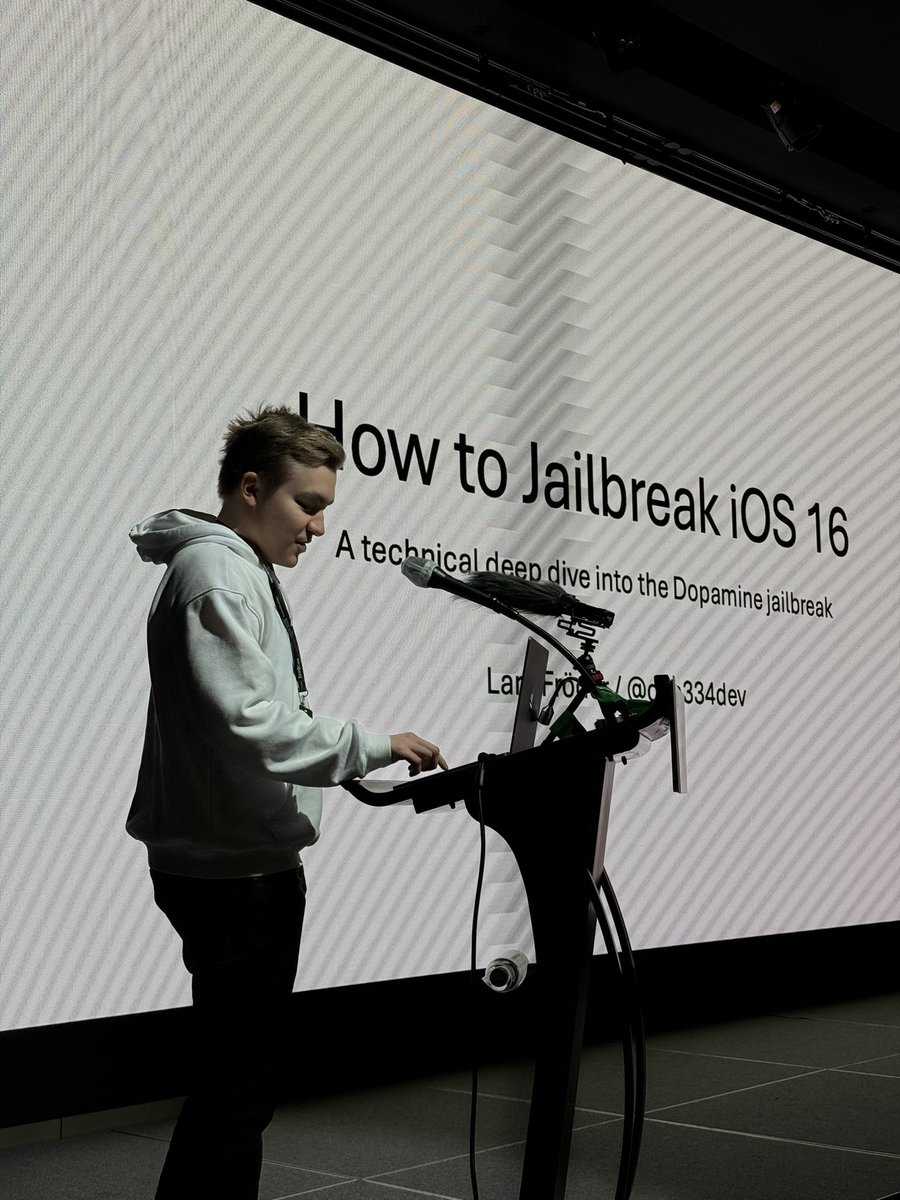
[#Zer0Con2024]
First time in S.Korea, totally loving it😆
@opa334dev
"How to Jailbreak iOS 16"
First time in S.Korea, totally loving it😆
@opa334dev
"How to Jailbreak iOS 16"
[#Zer0Con2024]
Another 0day to be revealed...?
Yes, stay tuned😆
@eternalsakura13 & @Kipreyyy
"Attacking Chrome from Runtime to JIT Once Again"
Another 0day to be revealed...?
Yes, stay tuned😆
@eternalsakura13 & @Kipreyyy
"Attacking Chrome from Runtime to JIT Once Again"

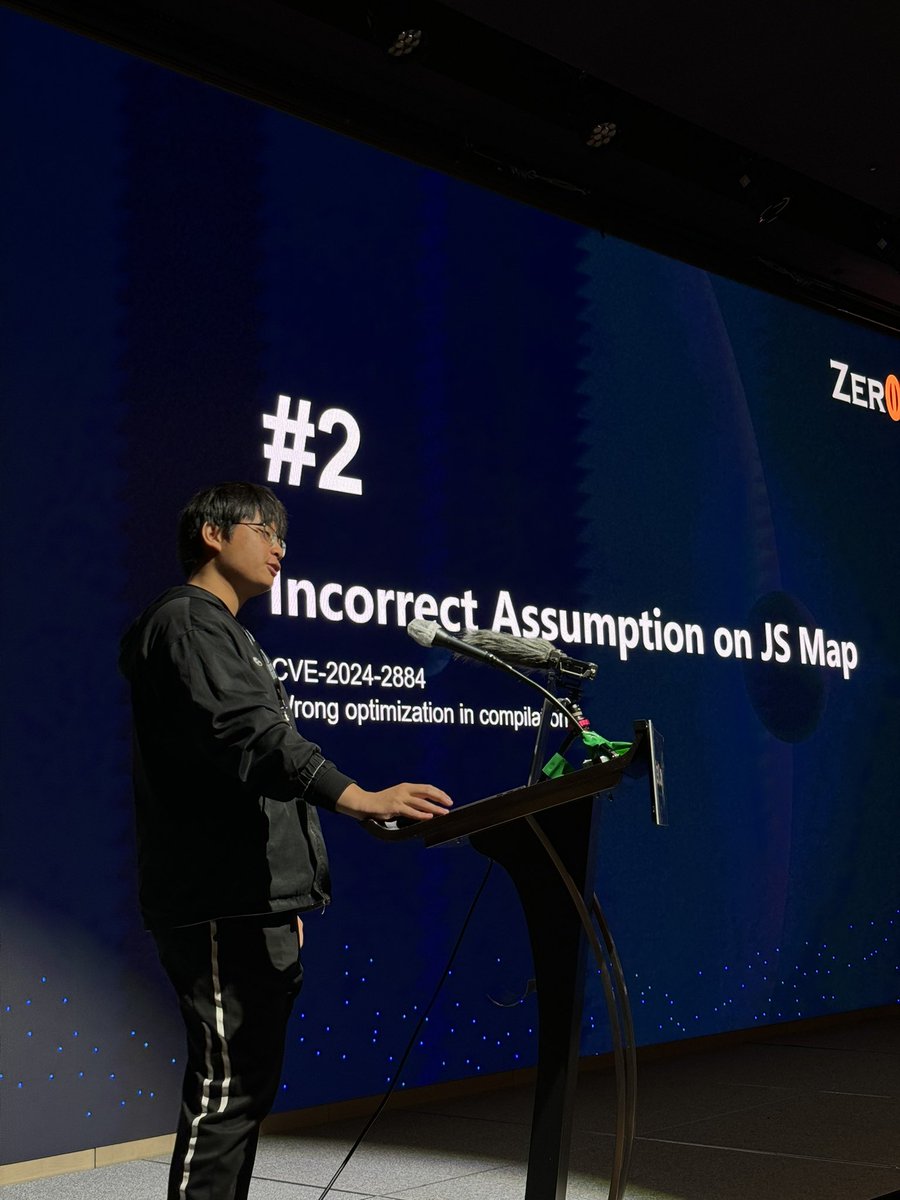
#Zer0Con2024
First 0day dropped 🤣
@munmap, @patateQbool
Guess what device it is
First 0day dropped 🤣
@munmap, @patateQbool
Guess what device it is
#Zer0Con2024
First Day, First Speakers!
They are planning to drop 0day on-site now😆
@munmap, @patateQbool
"Beyond Android MTE: Navigating OEM's Logic Labyrinths"
Stay tuned!
First Day, First Speakers!
They are planning to drop 0day on-site now😆
@munmap, @patateQbool
"Beyond Android MTE: Navigating OEM's Logic Labyrinths"
Stay tuned!




[#Zer0Con2024] He is back! 😎
“Exploiting the Linux Kernel”
Andrey Konovalov @andreyknvl
🗓️Date: 01/04/2024 ~ 03/04/2024
(3 DAYS) at CONRAD Seoul
“Exploiting the Linux Kernel”
Andrey Konovalov @andreyknvl
🗓️Date: 01/04/2024 ~ 03/04/2024
(3 DAYS) at CONRAD Seoul

[#Zer0Con2024] TRAINING Started! 🫨
"Attacking Instant Messaging Applications"
by Iddo ELDOR & Jacob BECH
🗓️Date: 31/03/2024 ~ 03/04/2024
(4 DAYS)
at CONRAD Seoul
"Attacking Instant Messaging Applications"
by Iddo ELDOR & Jacob BECH
🗓️Date: 31/03/2024 ~ 03/04/2024
(4 DAYS)
at CONRAD Seoul

[Zer0Con2024] SPONSOR
Huge thanks to @Binary_Gecko for sponsoring the con!
"Binary Gecko is an offensive cyber-security company with high end security researchers worldwide. We are currently hiring researchers who want to tackle complex challenges"
#Zer0Con2024
Huge thanks to @Binary_Gecko for sponsoring the con!
"Binary Gecko is an offensive cyber-security company with high end security researchers worldwide. We are currently hiring researchers who want to tackle complex challenges"
#Zer0Con2024

[Zer0Con2024] SPONSOR
Thank you @ENKI_official_X for supporting the con!
“Exploring history, securing today, and nurturing the future—our mission is to empower businesses with cutting-edge security services for seamless growth”
#Zer0Con2024
Thank you @ENKI_official_X for supporting the con!
“Exploring history, securing today, and nurturing the future—our mission is to empower businesses with cutting-edge security services for seamless growth”
#Zer0Con2024

[Zer0Con2024] SPONSOR
Thank you @hayyim_lab for sponsoring the con!
"We conduct vulnerability research on complex and challenging targets, such as browsers, antivirus software, mobile and more"
#Zer0Con2024
Thank you @hayyim_lab for sponsoring the con!
"We conduct vulnerability research on complex and challenging targets, such as browsers, antivirus software, mobile and more"
#Zer0Con2024

[Zer0Con2024]
Entry Tickets are all "SOLD-OUT"
Checking eligibilities on attendees in process
Thank you everyone for your support🙌🙌
Entry Tickets are all "SOLD-OUT"
Checking eligibilities on attendees in process
Thank you everyone for your support🙌🙌
[Zer0Con2024] SPONSOR
Thank you @TrenchantARC for sponsoring the con!
"We are looking for senior VR researchers and we’re excited to be on the way to Zer0con!”
#Zer0Con2024
Thank you @TrenchantARC for sponsoring the con!
"We are looking for senior VR researchers and we’re excited to be on the way to Zer0con!”
#Zer0Con2024

[Zer0Con2024] SPONSOR
Thank you @Meta for sponsoring us!
"If you believe you have found a security vulnerability on Meta (or another member of the Meta family of companies), we encourage you to let us know right away"
#Zer0Con2024
Thank you @Meta for sponsoring us!
"If you believe you have found a security vulnerability on Meta (or another member of the Meta family of companies), we encourage you to let us know right away"
#Zer0Con2024

[Zer0Con2024] "The Dignity"
We present you the Full list of Zer0con SPEAKERS
SEE YOU ALL SOON 🙌🙌
#Zer0Con2024
We present you the Full list of Zer0con SPEAKERS
SEE YOU ALL SOON 🙌🙌
#Zer0Con2024

[Zer0Con2024⬛️🟨Speaker#11]
Jinbum Park - Bypassing ARM MTE with Speculative Execution
#Zer0Con2024
Jinbum Park - Bypassing ARM MTE with Speculative Execution
#Zer0Con2024

[Zer0Con2024⬛️🟨Speaker#10]
Mingi Cho - Exploiting a Missed Linux Kernel Patch in a KernelCTF Instance
#Zer0Con2024
Mingi Cho - Exploiting a Missed Linux Kernel Patch in a KernelCTF Instance
#Zer0Con2024

[Zer0Con2024] SPONSOR
Thank you @df_forensics for sponsoring the con!
Looking forward to meeting you all soon
"Leveraging 0-days to detect the most sophisticated cyber-attacks on mobile devices."
#Zer0Con2024
Thank you @df_forensics for sponsoring the con!
Looking forward to meeting you all soon
"Leveraging 0-days to detect the most sophisticated cyber-attacks on mobile devices."
#Zer0Con2024

[Zer0Con2024⬛️🟨Speaker#9]
@Offside_Labs - Revealing One Key Security Insight for Hardware Wallets
#Zer0Con2024
@Offside_Labs - Revealing One Key Security Insight for Hardware Wallets
#Zer0Con2024

[Zer0Con2024] SPONSOR
Day 2 party is on me - huge thanks to @dfsec_com for supporting the con.
“Ready to party at zer0con? @dfsec_com is going to give us a fun night!”
#Zer0Con2024
Day 2 party is on me - huge thanks to @dfsec_com for supporting the con.
“Ready to party at zer0con? @dfsec_com is going to give us a fun night!”
#Zer0Con2024
[Zer0Con2024⬛️🟨Speaker#8]
@0x3C3E - The Userland Maze — Revealing macOS's Logic Bugs and Security Bypasses
#Zer0con2024
@0x3C3E - The Userland Maze — Revealing macOS's Logic Bugs and Security Bypasses
#Zer0con2024

[Zer0Con2024⬛️🟨Speaker#7]
@Dawuge3 - A Deep Dive in Android closed-source ROMs
#Zer0con2024
@Dawuge3 - A Deep Dive in Android closed-source ROMs
#Zer0con2024

🔊[Zer0Con2024] - UPDATES
🗓️Date: 4~5th April 2024
🏨 Venue: Fairmont Ambassador Seoul
🎟️Entry badge: Trust me, really not much available
🌘CFP status: Almost - TBA
🌑 Training status: "Seouled-out"
🌑 Sponsor status: Packed - TBA
For more: zer0conadm at gmail
#Zer0Con2024
🗓️Date: 4~5th April 2024
🏨 Venue: Fairmont Ambassador Seoul
🎟️Entry badge: Trust me, really not much available
🌘CFP status: Almost - TBA
🌑 Training status: "Seouled-out"
🌑 Sponsor status: Packed - TBA
For more: zer0conadm at gmail
#Zer0Con2024

[Zer0Con2024⬛️🟨Speaker#6]
@malltos92 - The boom, the bust, the adjust and the unknown
#Zer0con2024
@malltos92 - The boom, the bust, the adjust and the unknown
#Zer0con2024

[Zer0Con2024⬛️🟨Speaker#5]
@cr0wtom - Back to the Future: Old Vulnerabilities Becoming New Again
#Zer0con2024
@cr0wtom - Back to the Future: Old Vulnerabilities Becoming New Again
#Zer0con2024

Releasing final line-up in two weeks ⬛️🟨
(6 more speakers to be released)
CFP: until 5th March
Stay tuned!
(6 more speakers to be released)
CFP: until 5th March
Stay tuned!
[Zer0Con2024⬛️🟨Speaker#4]
👨👦 @eternalsakura13 & @Kipreyyy - Attacking Chrome from Runtime to JIT Once Again
#Zer0Con2024
👨👦 @eternalsakura13 & @Kipreyyy - Attacking Chrome from Runtime to JIT Once Again
#Zer0Con2024
[Zer0Con2024⬛️🟨Speaker#3]
👨👩👦👦 @munmap, @patateQbool, @MateuszFruba & @maxpl0it - Beyond Android MTE: Navigating OEM's Logic Labyrinths
#Zer0Con2024
👨👩👦👦 @munmap, @patateQbool, @MateuszFruba & @maxpl0it - Beyond Android MTE: Navigating OEM's Logic Labyrinths
#Zer0Con2024

[Zer0Con2024⬛️🟨Speaker#2]
👨👦 @edwardzpeng & R4nger & Q4n - Escaping the Sandbox (Chrome and Adobe PDF reader) on Windows
#Zer0Con2024
👨👦 @edwardzpeng & R4nger & Q4n - Escaping the Sandbox (Chrome and Adobe PDF reader) on Windows
#Zer0Con2024
[Zer0Con2024⬛️🟨Speaker#1]
🙋♂️@opa334dev - How to Jailbreak iOS 16
#Zer0Con2024
🙋♂️@opa334dev - How to Jailbreak iOS 16
#Zer0Con2024

yall ready for the line-up?
dropping 0day goons soon
#Zer0Con2024
dropping 0day goons soon
#Zer0Con2024
[Zer0Con2024] Sponsor
Day1 party is on their hands, thrilled to have @bluefrostsec as party sponsor at Zer0Con2024!
""BlueFrost Security, organizers of @offensive_con, is a research-driven cyber security company focusing on vulnerability research and we are hiring"
#Zer0Con2024
Day1 party is on their hands, thrilled to have @bluefrostsec as party sponsor at Zer0Con2024!
""BlueFrost Security, organizers of @offensive_con, is a research-driven cyber security company focusing on vulnerability research and we are hiring"
#Zer0Con2024

[Zer0Con2024] Sponsor
Delighted to announce @crowdfense as our Gold sponsor for Zer0Con2024!
"Crowdfense is a world-leading research hub and acquisition platform for high-quality zero-day exploits and advanced vulnerability research"
#Zer0Con2024
Delighted to announce @crowdfense as our Gold sponsor for Zer0Con2024!
"Crowdfense is a world-leading research hub and acquisition platform for high-quality zero-day exploits and advanced vulnerability research"
#Zer0Con2024

[Zer0con2024] Sponsor
Thank you @SecuriTeam_SSD for supporting the conference.
"SSD provides the knowledge, experience and tools needed to find and disclose vulnerabilities and advanced attack vectors"
#Zer0Con2024
Thank you @SecuriTeam_SSD for supporting the conference.
"SSD provides the knowledge, experience and tools needed to find and disclose vulnerabilities and advanced attack vectors"
#Zer0Con2024

CFP is still open though :)
Coming up next: #Zer0con2024
3rd Week of Feb: releasing sponsors for Zer0Con2024
4th Week of Feb: releasing the 1st speaker line-up
3rd Week of Feb: releasing sponsors for Zer0Con2024
4th Week of Feb: releasing the 1st speaker line-up

[Zer0Con2024] TRAINING
"Android Internals: The Hacker's View" by @Morpheus______
🗓️Date: 1/04/2024 ~ 03/04/2024 (3 DAYS) at Fairmont Ambassador Seoul, South Korea
For more: https://t.co/6cUC0ODFXm
#Zer0Con2024
"Android Internals: The Hacker's View" by @Morpheus______
🗓️Date: 1/04/2024 ~ 03/04/2024 (3 DAYS) at Fairmont Ambassador Seoul, South Korea
For more: https://t.co/6cUC0ODFXm
#Zer0Con2024


[Zer0Con2024] TRAINING
"Exploiting the Linux Kernel (purely on exploitation)"
by @andreyknvl
🗓️Date: 1/04/2024 ~ 03/04/2024 (3 DAYS)
at Fairmont Ambassador Seoul, South Korea
For more: https://t.co/6cUC0ODFXm
#Zer0Con2024
"Exploiting the Linux Kernel (purely on exploitation)"
by @andreyknvl
🗓️Date: 1/04/2024 ~ 03/04/2024 (3 DAYS)
at Fairmont Ambassador Seoul, South Korea
For more: https://t.co/6cUC0ODFXm
#Zer0Con2024
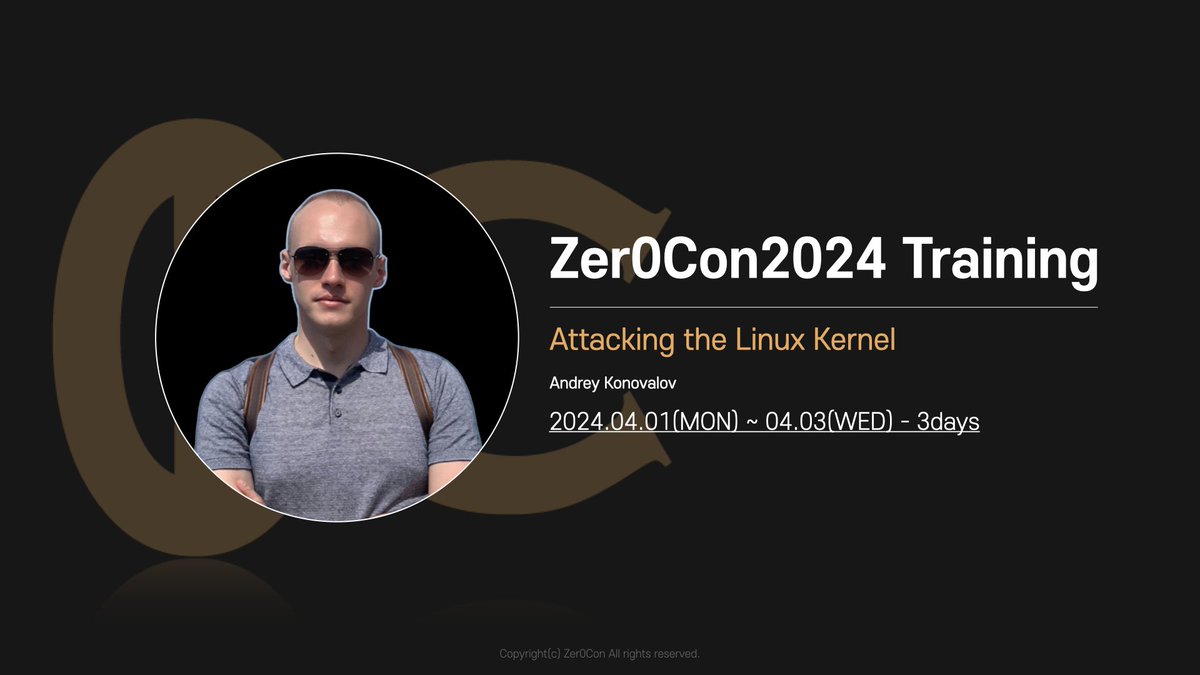
[Zer0Con2024] TRAINING
"Attacking Instant Messaging Applications"
by Iddo ELDOR & Jacob BECH
🗓️Date: 31/03/2024 ~ 03/04/2024 (4 DAYS)
at Fairmont Ambassador Seoul, South Korea
For more: https://t.co/6cUC0ODFXm
#Zer0Con2024
"Attacking Instant Messaging Applications"
by Iddo ELDOR & Jacob BECH
🗓️Date: 31/03/2024 ~ 03/04/2024 (4 DAYS)
at Fairmont Ambassador Seoul, South Korea
For more: https://t.co/6cUC0ODFXm
#Zer0Con2024
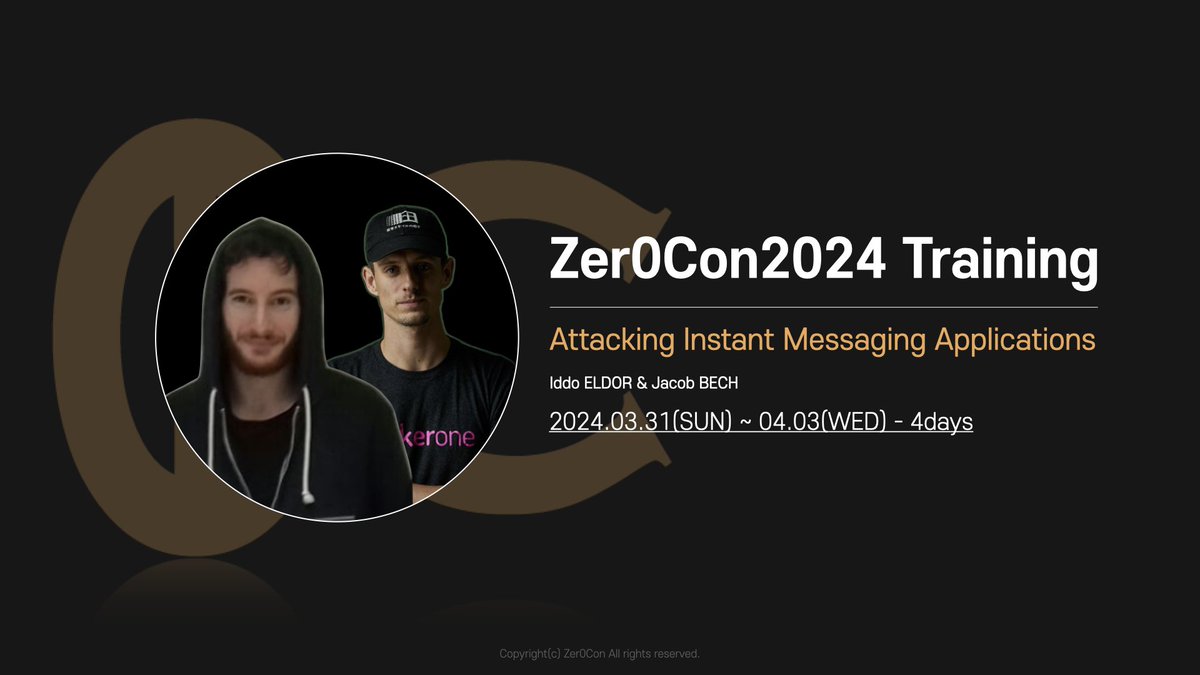
New Year and New vulnerabilties
Who's going to be the first one to exploit at #Zer0Con2024?
Who's going to be the first one to exploit at #Zer0Con2024?
🔊[Zer0Con2024] - UPDATES
Enjoyed POC2023? Have better experience at #Zer0Con2024
🗓️Date: 4~5th April 2024
🏨Venue: Fairmont Ambassdor Seoul
🎟️Entry badge: 120 avail
🌕CFP status: Open
🌗Training status: To be updated
🌕Sponsor status: Open
For more: "zer0conadm at gmail"
Enjoyed POC2023? Have better experience at #Zer0Con2024
🗓️Date: 4~5th April 2024
🏨Venue: Fairmont Ambassdor Seoul
🎟️Entry badge: 120 avail
🌕CFP status: Open
🌗Training status: To be updated
🌕Sponsor status: Open
For more: "zer0conadm at gmail"

Drinking hell is on!!!! 🥂 Thanks to the @dfsec_com for sponsoring👊
#POC2023
#POC2023
[POC2023]
The Last speaker, wrapping up conference finale with Mark brand😎
He is talking about “MTE as Tested”
#POC2023
The Last speaker, wrapping up conference finale with Mark brand😎
He is talking about “MTE as Tested”
#POC2023



[POC2023]
We have a Korean team, @c0m0r1 & @0x10n
They are going to talk about “One shot, Triple kill : Pwning all three Google Kernel CTF with single 1day linux vulnerability”
#POC2023
We have a Korean team, @c0m0r1 & @0x10n
They are going to talk about “One shot, Triple kill : Pwning all three Google Kernel CTF with single 1day linux vulnerability”
#POC2023

[POC2023]
It's an honor to listen to @__sethJenkins first ever talk at a conference 😁
He is talking about "Exploiting null-derefs: Doing the impossible in the Linux kernel"
#POC2023
It's an honor to listen to @__sethJenkins first ever talk at a conference 😁
He is talking about "Exploiting null-derefs: Doing the impossible in the Linux kernel"
#POC2023



[POC2023], Track A
Many people came to hear @ThomasKing2014 presentation! 👍
He is talking about “Simple bug but not easy exploit: Rooting Android devices in one shot”
#POC2023
Many people came to hear @ThomasKing2014 presentation! 👍
He is talking about “Simple bug but not easy exploit: Rooting Android devices in one shot”
#POC2023
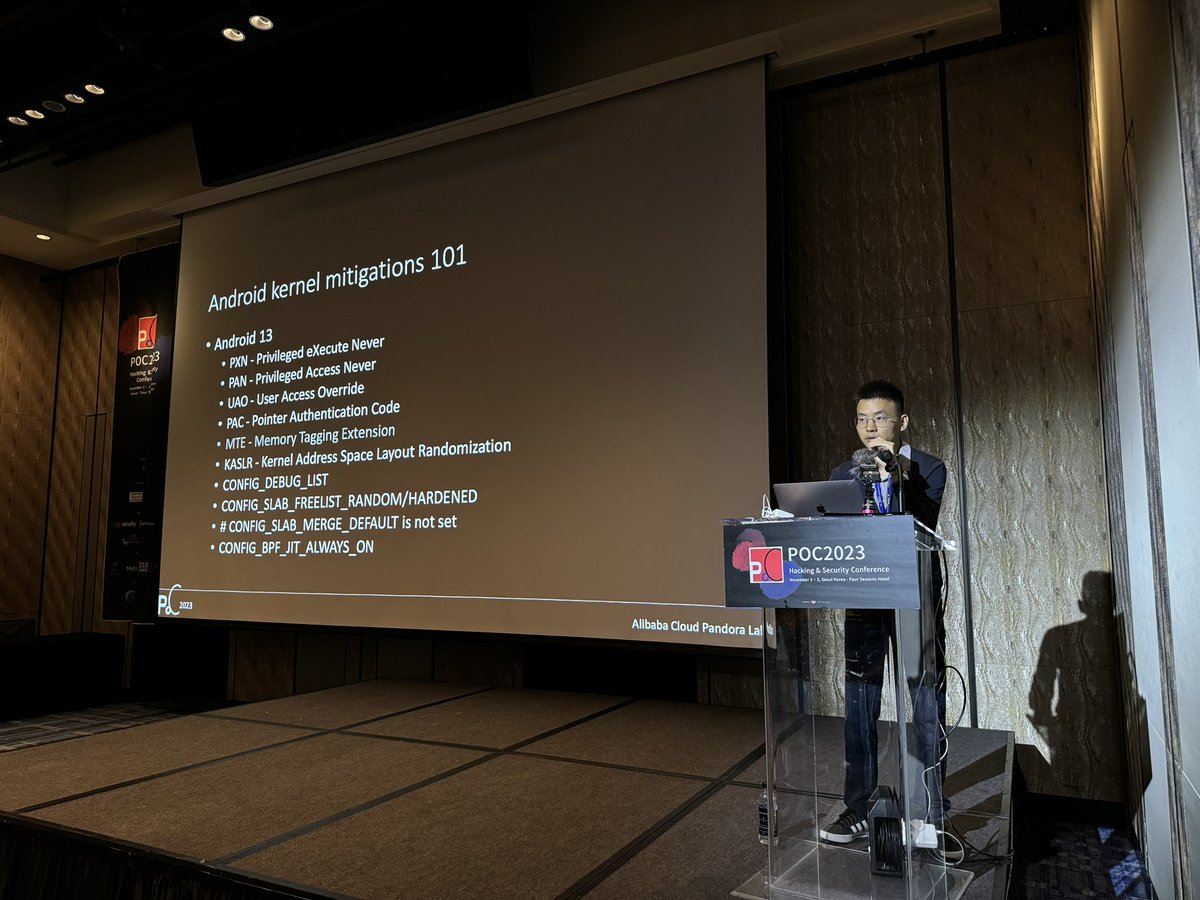


@4zure9 sorry for the tag 😅
[POC2023] D2 Track B
N.K expert here, @R_Sherstobitoff talking about “Tracking APT’s through Advanced SIGINT techniques”
#POC2023
N.K expert here, @R_Sherstobitoff talking about “Tracking APT’s through Advanced SIGINT techniques”
#POC2023


[POC2023] D2 - Track B
No MSMQ related talk was discussed before but now it is!
@guhe120 @KeyZ3r0, Azure are talking about “Bug Hunting and Exploiting in Microsoft's Message Queuing(MSMQ) Components"
#POC2023
No MSMQ related talk was discussed before but now it is!
@guhe120 @KeyZ3r0, Azure are talking about “Bug Hunting and Exploiting in Microsoft's Message Queuing(MSMQ) Components"
#POC2023
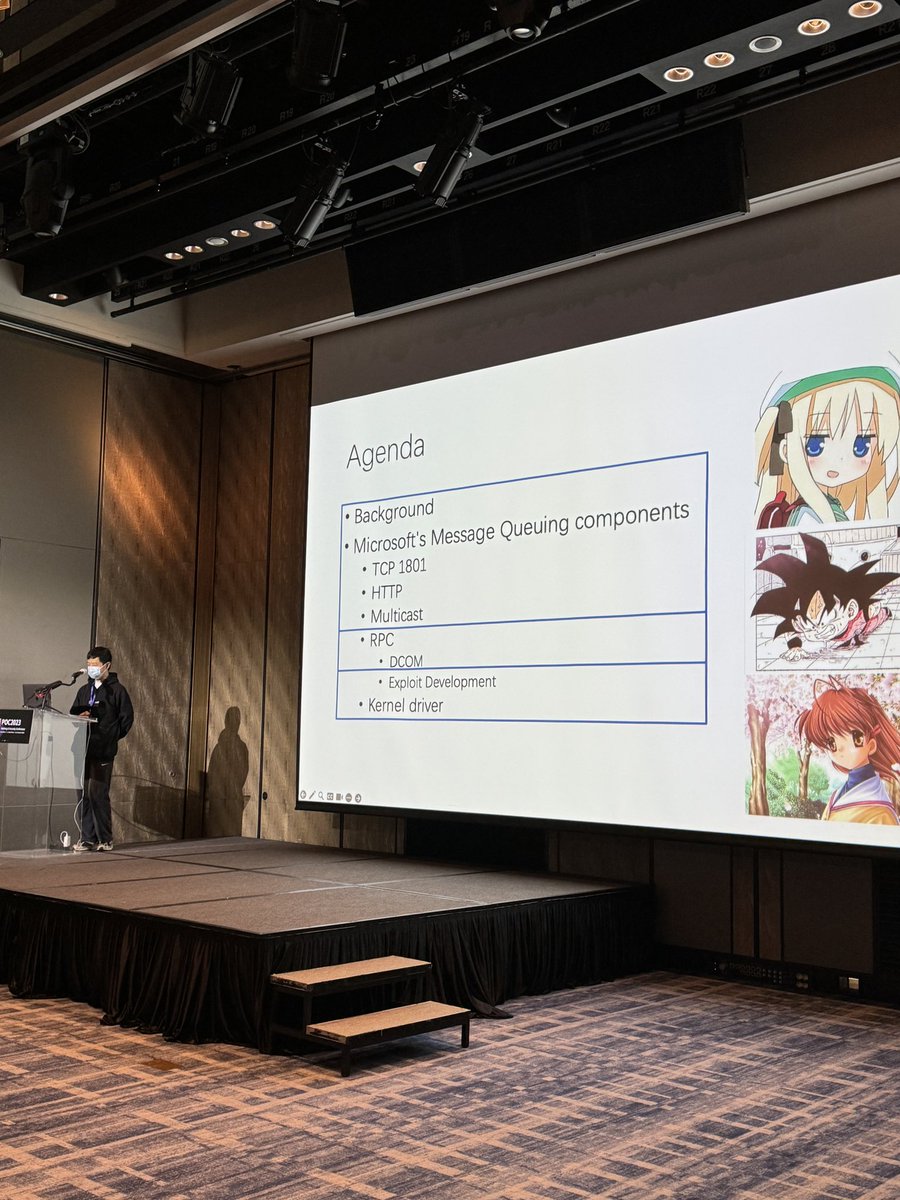

[POC2023], Track A
Our friend @NedWilliamson is back!
He is talking about “Fuzzing as Reinforcement Learning”
After this talk, he is ready to enjoy POC party 🔥🔥
#POC2023
Our friend @NedWilliamson is back!
He is talking about “Fuzzing as Reinforcement Learning”
After this talk, he is ready to enjoy POC party 🔥🔥
#POC2023



[POC2023], Track A
Zhaofeng Chen is presenting at our conference for the first time! 😄
He will present on the topic “Attack Move Verifiers: Our Experiences of Exploiting and Enhancing Move-based Blockchain”
#POC2023
Zhaofeng Chen is presenting at our conference for the first time! 😄
He will present on the topic “Attack Move Verifiers: Our Experiences of Exploiting and Enhancing Move-based Blockchain”
#POC2023
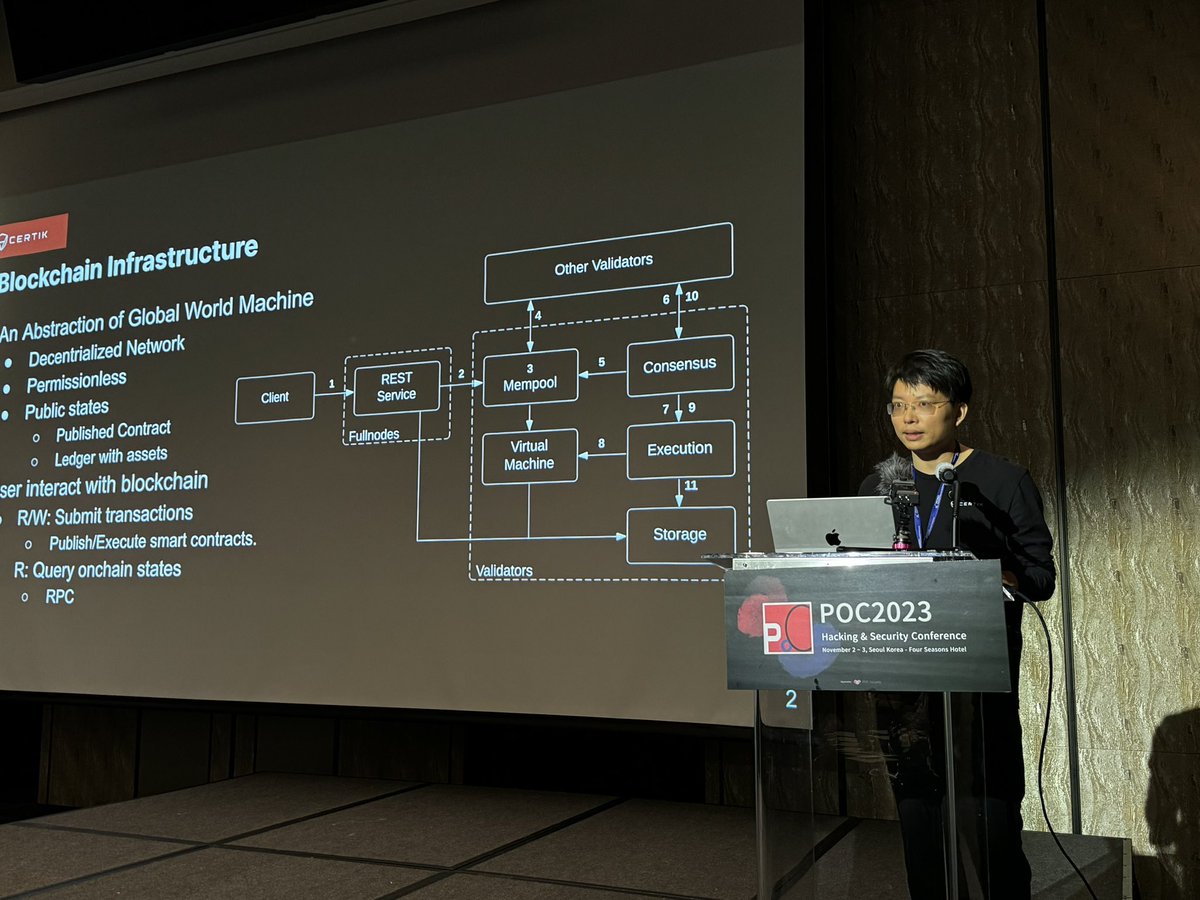
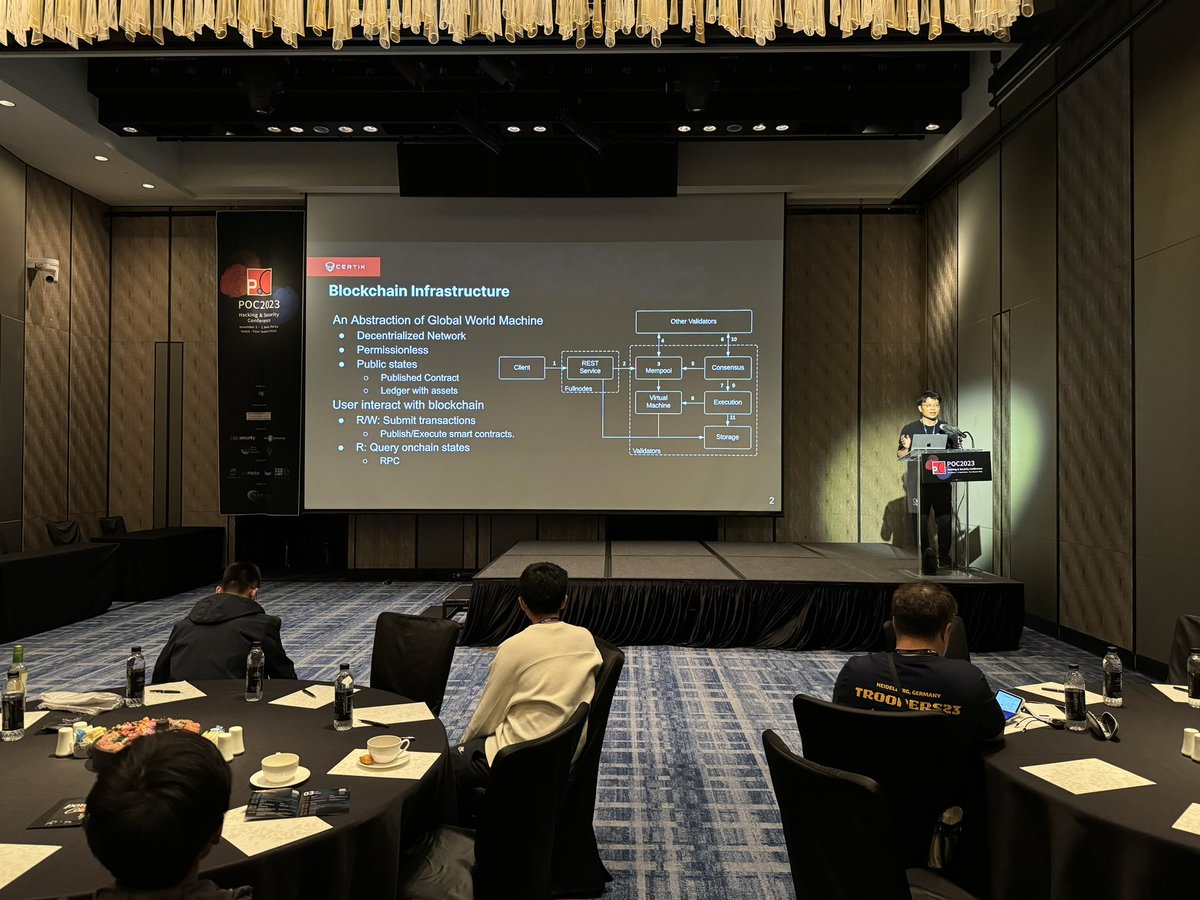
[POC2023] Decorating the 1st day with our last speaker @splinter_code
“10 years of Windows Privilege Escalation with Potatoes”
#POC2023
“10 years of Windows Privilege Escalation with Potatoes”
#POC2023

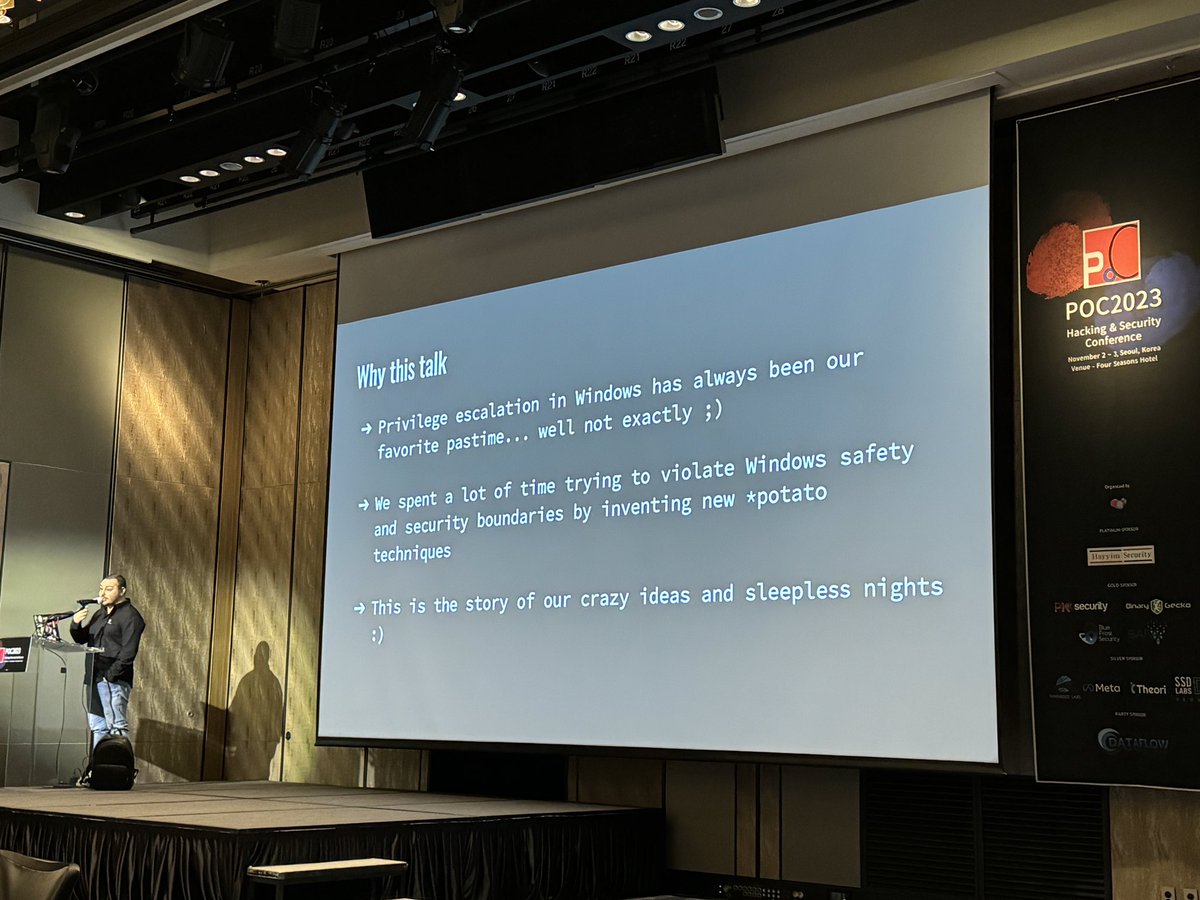
[POC2023]
@ignatkn hardcore Linux master, giving his talk on “Linux user namespaces: a blessing and a curse”
#POC2023
@ignatkn hardcore Linux master, giving his talk on “Linux user namespaces: a blessing and a curse”
#POC2023
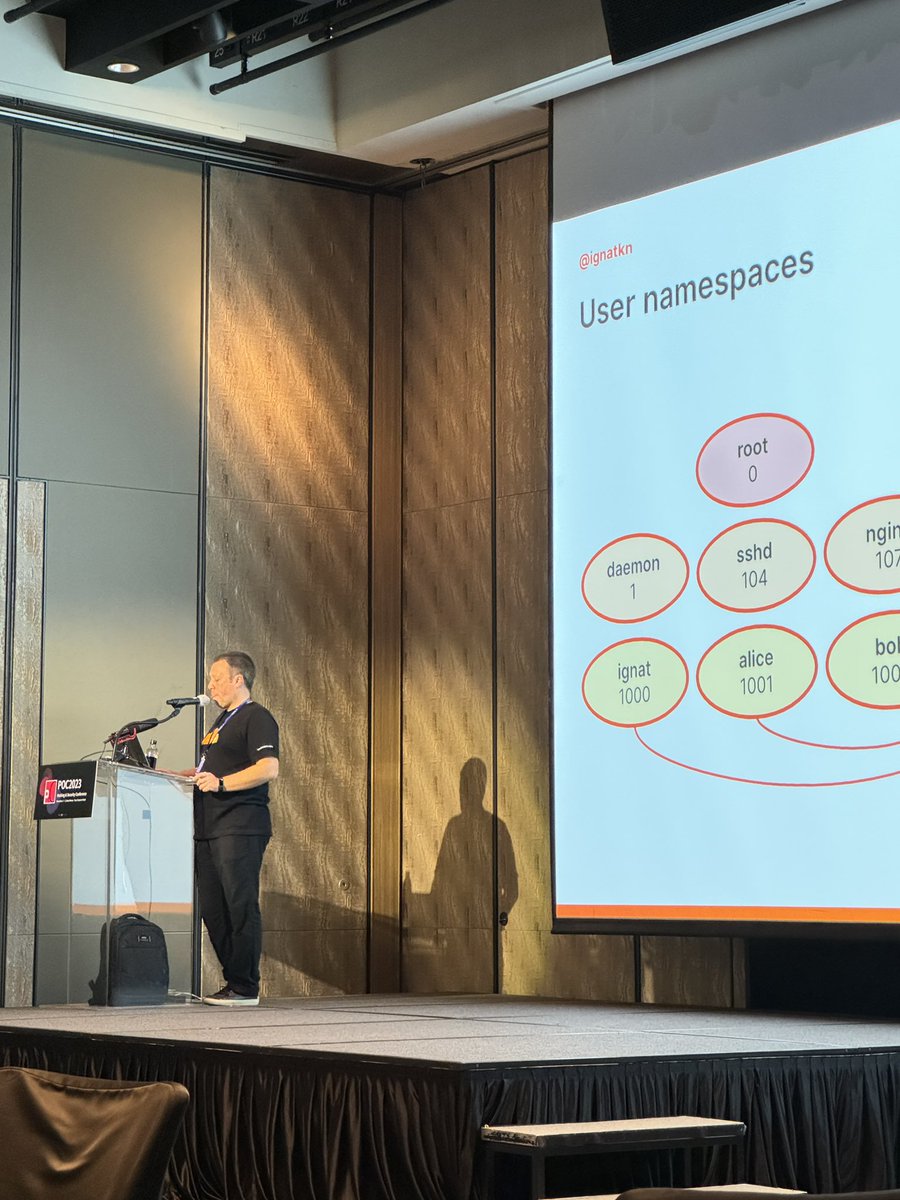
[POC2023], Track A
We have new friends Yingjie Cao & Zhe Jing!
They are talking about "A roadmap to $50,000 at Pwn2Own Vehicle 2024: Dissecting QNX and exploiting its vulnerabilities" 🚗
#POC2023
We have new friends Yingjie Cao & Zhe Jing!
They are talking about "A roadmap to $50,000 at Pwn2Own Vehicle 2024: Dissecting QNX and exploiting its vulnerabilities" 🚗
#POC2023


Thanks to @SAFATeamGmbH @justandrijana for the special gifts😍and “ракија” Come to their booth for a shot and opportunities
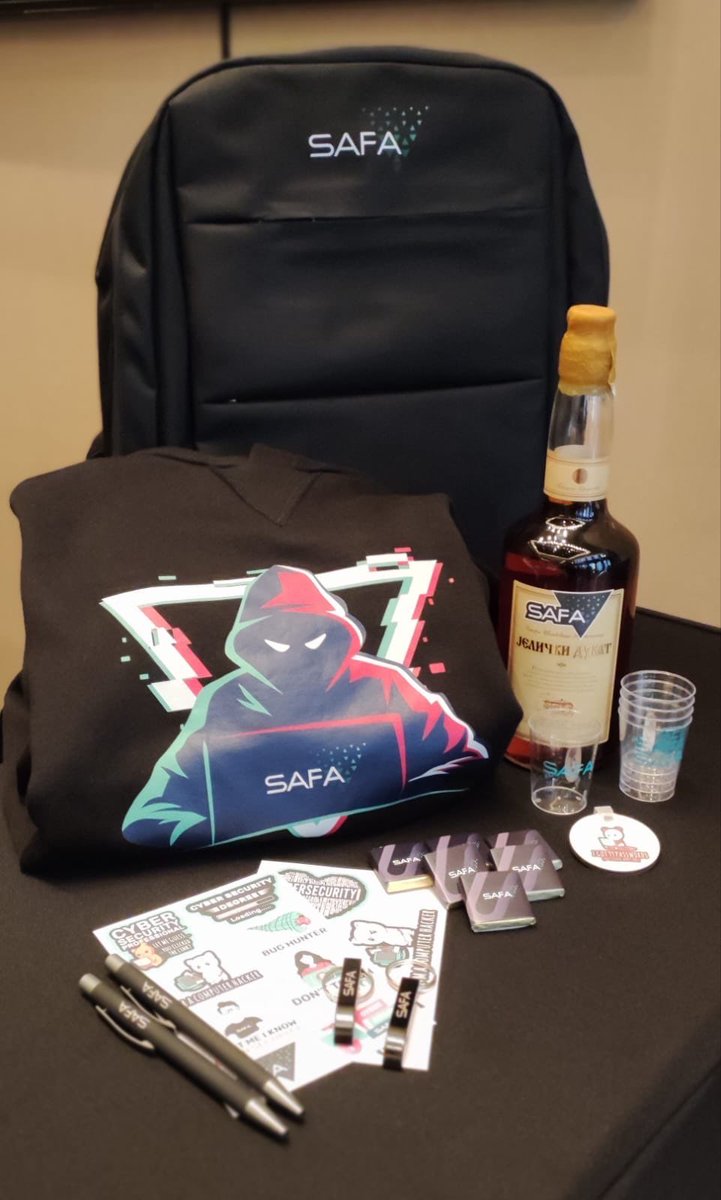
[POC2023], Track A
We have @edwardzpeng & @wh1tc talking about OLE object are still dangerous today — Exploiting Microsoft Office
#POC2023
We have @edwardzpeng & @wh1tc talking about OLE object are still dangerous today — Exploiting Microsoft Office
#POC2023


[POC2023] Tracks divided, on Track B
We have Nikita Pupyshev talking about Evolution of Safari mitigations and bypasses in 2022
#POC2023
We have Nikita Pupyshev talking about Evolution of Safari mitigations and bypasses in 2022
#POC2023
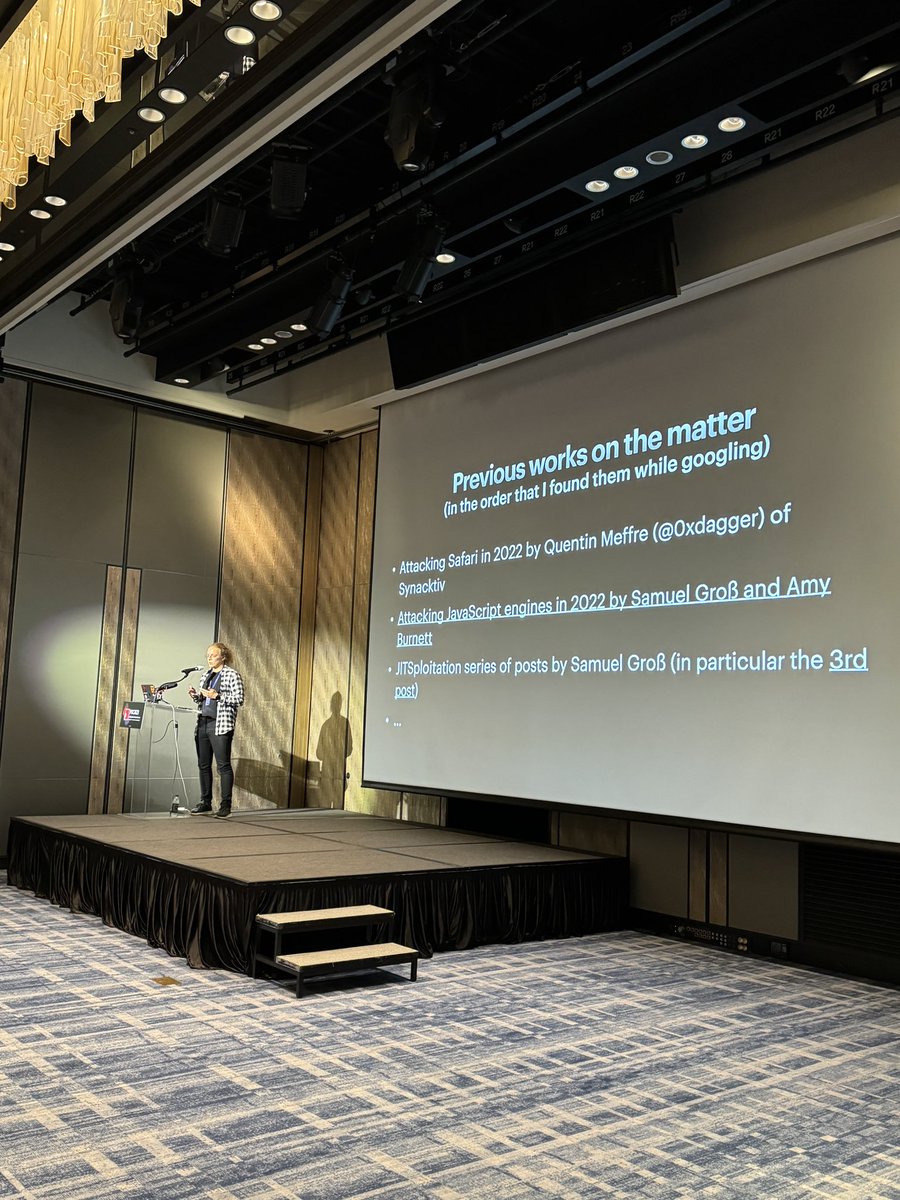


Shout out to @Binary_Gecko @Ronkeybiz @kawarei0 for such great gift all the way from Germany😍
Long time favorite!
Long time favorite!

[POC2023] Second talk
just bypassed V8 SBX(latest) using WASM > disclosing at POC
@frust93717815 @ yyjb “Modern Chrome Exploitation”
#POC2023
just bypassed V8 SBX(latest) using WASM > disclosing at POC
@frust93717815 @ yyjb “Modern Chrome Exploitation”
#POC2023


[POC2023] “First speaker”
The living legend @tiraniddo is giving out his talk on “Building More Windows RPC Tooling for Security Research”
#POC2023
The living legend @tiraniddo is giving out his talk on “Building More Windows RPC Tooling for Security Research”
#POC2023



[POC2023] Keynote on vulnerability insights
@mj0011sec giving his talk on “Navigating the light and darkness in the world of vulnerabilities”
#POC2023
@mj0011sec giving his talk on “Navigating the light and darkness in the world of vulnerabilities”
#POC2023



[POC2023] has just started!
Starting off with Jinwook’s opening remarks
#POC2023
Starting off with Jinwook’s opening remarks
#POC2023


[POC2023] D-1
ARE YOU READY?
#POC2023
ARE YOU READY?
#POC2023



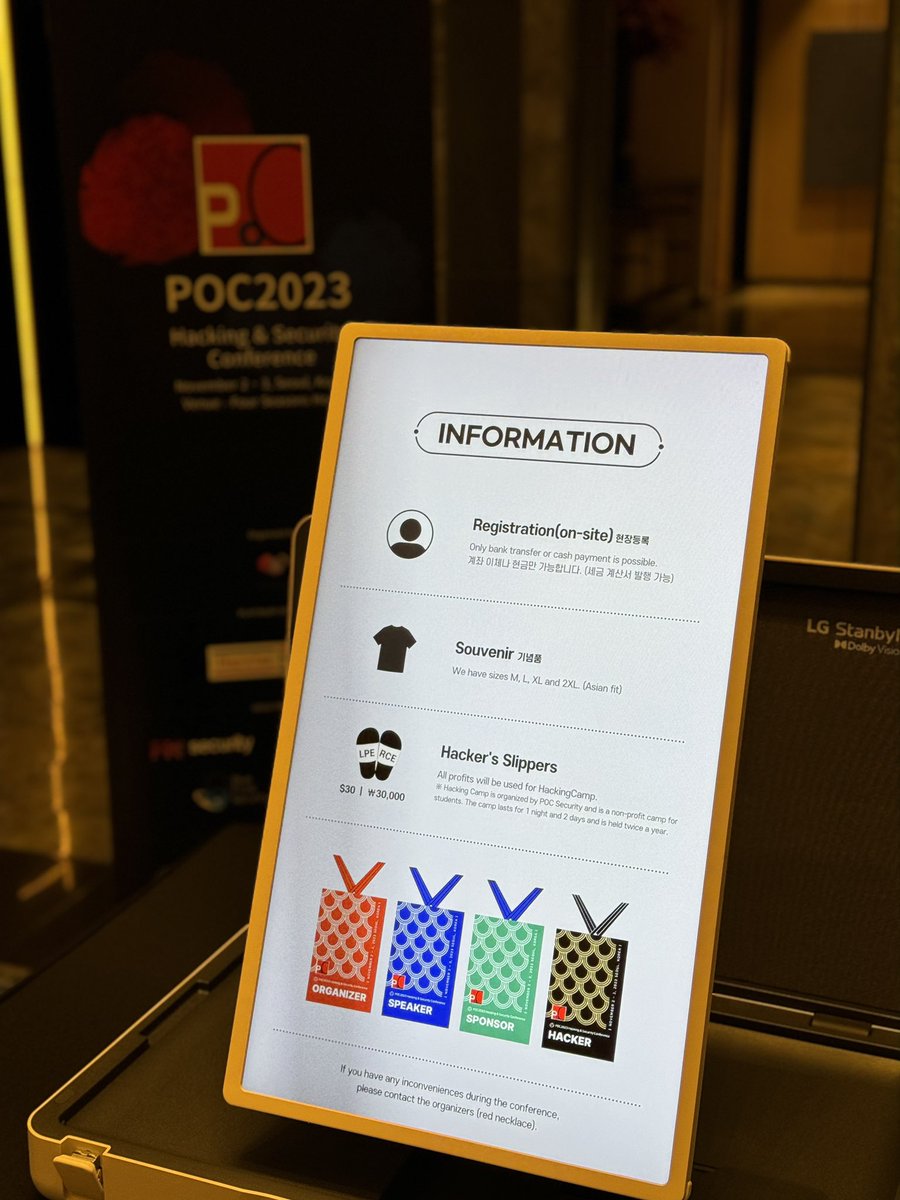
[POC2023] Trainings going smooth✌️
More trainings will be filled up in next upcoming #Zer0con2024
#POC2023
More trainings will be filled up in next upcoming #Zer0con2024
#POC2023


[POC2023] Trainer dinner is on!
@dawidczagan @prateekg147 @Din3zh enjoying Korean pork before the training starts tomorrow!
#POC2023
@dawidczagan @prateekg147 @Din3zh enjoying Korean pork before the training starts tomorrow!
#POC2023


[POC2023] FULL LINE-UP
See you all at #POC2023!
Looking forward to meeting old & new friends😍
Just about a week ahead 👊👊
Date: 2-3 November 2023
See you all at #POC2023!
Looking forward to meeting old & new friends😍
Just about a week ahead 👊👊
Date: 2-3 November 2023

[POC2023] PLATINUM SPONSOR
🔵@hayyim_lab
🔊 "We conduct vulnerability research on complex and challenging targets, such as browsers, antivirus software, mobile and more"
🔵@hayyim_lab
🔊 "We conduct vulnerability research on complex and challenging targets, such as browsers, antivirus software, mobile and more"
[POC2023] PARTY PLANNER SPONSOR
🟣 @dfsec_com
🔊 "We are driven by our curiosity to understand systems and how they interact, and use this advantage to deliver unique research to our clients"
🟣 @dfsec_com
🔊 "We are driven by our curiosity to understand systems and how they interact, and use this advantage to deliver unique research to our clients"
[POC2023] GOLD SPONSOR
🟡 @Binary_Gecko
🔊 "We offer a range of services, including defensive products designed to protect our clients from cyber threats as well as our own specialized Security Research Division: Binary Gecko Labs"
🟡 @Binary_Gecko
🔊 "We offer a range of services, including defensive products designed to protect our clients from cyber threats as well as our own specialized Security Research Division: Binary Gecko Labs"
[POC2023] GOLD SPONSOR
🟡@pksecurity_io
🔊 "We are a vulnerability research company which digs into hidden faults in various software.
Make the impossible possible. Any difficult cyber security challenge will eventually be solved by us"
🟡@pksecurity_io
🔊 "We are a vulnerability research company which digs into hidden faults in various software.
Make the impossible possible. Any difficult cyber security challenge will eventually be solved by us"
[POC2023] GOLD SPONSOR
🟡 @bluefrostsec
🔊"BlueFrost Security, organizers of @offensive_con, is a research-driven cyber security company focusing on vulnerability research and they are hiring!"
🟡 @bluefrostsec
🔊"BlueFrost Security, organizers of @offensive_con, is a research-driven cyber security company focusing on vulnerability research and they are hiring!"
[POC2023] GOLD SPONSOR
🟡@SAFATeamGmbH
🔊"From Europe to Korea, we are a research lab leveraging its extensive experience to provide high-end deliverables. Always looking for experienced researchers, keep calm and join us"
🟡@SAFATeamGmbH
🔊"From Europe to Korea, we are a research lab leveraging its extensive experience to provide high-end deliverables. Always looking for experienced researchers, keep calm and join us"
[POC2023] - SILVER SPONSOR
⚪️ @theori_io
🔊 "It is a cybersecurity R&D startup that aims to identify and improve difficult security problems and create a safe cyber world through creative and innovative research and development based on world-class technology."
⚪️ @theori_io
🔊 "It is a cybersecurity R&D startup that aims to identify and improve difficult security problems and create a safe cyber world through creative and innovative research and development based on world-class technology."
[POC2023] - SPEAKER UPDATE1⃣5️⃣
@R_Sherstobitoff - Tracking APTs through Advanced SIGINT techniques
#POC2023
@R_Sherstobitoff - Tracking APTs through Advanced SIGINT techniques
#POC2023
[POC2023] - SILVER SPONSOR
⚪️ @Meta
🔊 "If you believe you have found a security vulnerability on Meta (or another member of the Meta family of companies), we encourage you to let us know right away"
⚪️ @Meta
🔊 "If you believe you have found a security vulnerability on Meta (or another member of the Meta family of companies), we encourage you to let us know right away"
[POC2023] - SILVER SPONSOR
⚪️@SecuriTeam_SSD
🔊 "A premium hub for security researchers, looking to collaborate on complex findings, specific research niche or higher-tiered projects"
⚪️@SecuriTeam_SSD
🔊 "A premium hub for security researchers, looking to collaborate on complex findings, specific research niche or higher-tiered projects"
[POC2023] - SILVER SPONSOR
⚪️Synthesize Labs
🔊"We are always looking forward to working with talented vuln researchers and exploit developers"
⚪️Synthesize Labs
🔊"We are always looking forward to working with talented vuln researchers and exploit developers"
[POC2023] - KEYNOTE SPEAKER
💁♂️ @mj0011sec Navigating the Light and Darkness in the World of Vulnerabilities
#POC2023
💁♂️ @mj0011sec Navigating the Light and Darkness in the World of Vulnerabilities
#POC2023
[POC2023] - SPEAKER UPDATE1⃣4⃣
💁♂️@frust93717815, yyjb - Modern Chrome Exploit Chain Development
#POC2023
💁♂️@frust93717815, yyjb - Modern Chrome Exploit Chain Development
#POC2023
Kudos to @hexacon_fr with another successful conference!
Had lots fun during our stays. Awesome hospitality with amazing events!
Had lots fun during our stays. Awesome hospitality with amazing events!

[TDB]
T: @TrenchantARC
D: Drinks
B: Best (BaskinRobbins31)
#Hexacon2023
T: @TrenchantARC
D: Drinks
B: Best (BaskinRobbins31)
#Hexacon2023


Thanks for the gift!❤️ @hexacon_fr
Refreshing our liver with this
Refreshing our liver with this

[POC2023] - SPEAKER UPDATE1⃣4️⃣
💁♂️ @guhe120, @KeyZ3r0, Azure Yang - Bug Hunting and Exploiting in Microsoft's Message Queuing (MSMQ) Components
#POC2023
💁♂️ @guhe120, @KeyZ3r0, Azure Yang - Bug Hunting and Exploiting in Microsoft's Message Queuing (MSMQ) Components
#POC2023

[POC2023] - SPEAKER UPDATE1⃣3️⃣
💁♂️ Yingjie Cao, Zhe Jing - A roadmap to $50,000 at Pwn2Own Vehicle 2024: Dissecting QNX, and exploiting its vulnerabilities
#POC2023
💁♂️ Yingjie Cao, Zhe Jing - A roadmap to $50,000 at Pwn2Own Vehicle 2024: Dissecting QNX, and exploiting its vulnerabilities
#POC2023
[POC2023] - SPEAKER UPDATE1⃣2️⃣
💁♂️ @c0m0r1, @Xion One shot, Triple kill: Pwning all three Google kernelCTF instances with a single 1-day Linux vulnerability
#POC2023
💁♂️ @c0m0r1, @Xion One shot, Triple kill: Pwning all three Google kernelCTF instances with a single 1-day Linux vulnerability
#POC2023
[POC2023] - SPEAKER UPDATE1⃣1️⃣
💁♂️ @NedWilliamson Fuzzing as Reinforcement Learning
#POC2023
💁♂️ @NedWilliamson Fuzzing as Reinforcement Learning
#POC2023

[POC2023] - SPEAKER UPDATE1⃣0⃣
💁♂️ @splinter_code 10 years of Windows Privilege Escalation with Potatoes
#POC2023
💁♂️ @splinter_code 10 years of Windows Privilege Escalation with Potatoes
#POC2023
[POC2023] - SPEAKER UPDATE9⃣
💁♂️Zhaofeng Chen - Attack Move Verifiers: Our Experiences of Exploiting and Enhancing Move-based Blockchain
#POC2023
💁♂️Zhaofeng Chen - Attack Move Verifiers: Our Experiences of Exploiting and Enhancing Move-based Blockchain
#POC2023

[POC2023] - SPEAKER UPDATE8⃣
💁♂️@ignatkn Linux user namespaces: a blessing and a curse
#POC2023
💁♂️@ignatkn Linux user namespaces: a blessing and a curse
#POC2023
[POC2023] - SPEAKER UPDATE7⃣
💁♂️ Nikita Pupyshev - Evolution of Safari mitigation and bypasses in 2022.
#POC2023
💁♂️ Nikita Pupyshev - Evolution of Safari mitigation and bypasses in 2022.
#POC2023
[POC2023] - SPEAKER UPDATE6⃣
💁♂️ @ThomasKing2014 Simple bug but not easy exploit: Rooting Android devices in one shot
#POC2023
💁♂️ @ThomasKing2014 Simple bug but not easy exploit: Rooting Android devices in one shot
#POC2023

[POC2023] - SPEAKER UPDATE5⃣
💁♂️Mark Brand - MTE as Tested
#POC2023
💁♂️Mark Brand - MTE as Tested
#POC2023

[POC2023] - SPEAKER UPDATE4⃣
💁♂️ @__sethJenkins Exploiting null-derefs: Doing the impossible in the Linux kernel
#POC2023
💁♂️ @__sethJenkins Exploiting null-derefs: Doing the impossible in the Linux kernel
#POC2023
[POC2023] - SPEAKER UPDATE3⃣
💁♂️@nachoskrnl Windows Paths Unveiled: Journey Into Parsing Errors
#POC2023
💁♂️@nachoskrnl Windows Paths Unveiled: Journey Into Parsing Errors
#POC2023
[POC2023] - SPEAKER UPDATE2⃣
💁♂️@wh1tc @edwardzpeng OLE object are still dangerous today - Exploiting Microsoft Office
#POC2023
💁♂️@wh1tc @edwardzpeng OLE object are still dangerous today - Exploiting Microsoft Office
#POC2023
[POC2023] - SPEAKER UPDATE1⃣
💁♂️@tiraniddo Building More Windows RPC Tooling for Security Research
#POC2023
💁♂️@tiraniddo Building More Windows RPC Tooling for Security Research
#POC2023

[POC2023] Registration is OPEN!
📍First line-up of POC2023 will be uploaded next
week (5th Sept)
For more: https://t.co/LfQX3mQQeZ
Get ready & Stay tuned 🙏
#POC2023
📍First line-up of POC2023 will be uploaded next
week (5th Sept)
For more: https://t.co/LfQX3mQQeZ
Get ready & Stay tuned 🙏
#POC2023
[POC2023] "Training deadline extended"
📅 Registration Deadline: Until 20th September
‼️ More training courses to be filled in upcoming days
For more: https://t.co/efBfYIgAjG
#POC2023
📅 Registration Deadline: Until 20th September
‼️ More training courses to be filled in upcoming days
For more: https://t.co/efBfYIgAjG
#POC2023
The crew is here at the VEGAS! for both @BlackHatEvents & @defcon
let us know if you are around
Who's up for drink all night long?
let us know if you are around
Who's up for drink all night long?



[POC2023 REMINDER]
CFP - Until 15th Oct
* lots of CFPs coming through, don't forget to submit yours if you have not done yet ‼️
CFT - Trainings uploaded on the website, few more to come 🫶
#POC2023
CFP - Until 15th Oct
* lots of CFPs coming through, don't forget to submit yours if you have not done yet ‼️
CFT - Trainings uploaded on the website, few more to come 🫶
#POC2023
📣 POC2023 - Training
@dawidczagan is giving "Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation (100% Hands-On, Extended Edition)
📅Date: 29th Oct(Sun) - 1st Nov(Wed) - 4 days
Register: https://t.co/efBfYIgAjG…
#POC2023
@dawidczagan is giving "Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation (100% Hands-On, Extended Edition)
📅Date: 29th Oct(Sun) - 1st Nov(Wed) - 4 days
Register: https://t.co/efBfYIgAjG…
#POC2023
📣 POC2023 - Training
@prateekg147 & @Din3zh are giving "Master Class on Mobile Security" - Platform Internals and InSecurity
Now is your chance to master your Mobile skills
📅 Date: 29th Oct(Sun) - 1st Nov(Wed) - 4 days
Register: https://t.co/efBfYIgAjG
#POC2023
@prateekg147 & @Din3zh are giving "Master Class on Mobile Security" - Platform Internals and InSecurity
Now is your chance to master your Mobile skills
📅 Date: 29th Oct(Sun) - 1st Nov(Wed) - 4 days
Register: https://t.co/efBfYIgAjG
#POC2023

Great conference indeed @0x41con Thanks to the organizers @xerub @f_roncari @Simone_Ferrini @jndok for making such wonderful atmosphere with everyone👊

[POC2023 NOTICE]
⏰Date: 2-3rd November, 2023
🇰🇷Venue: Four Seasons Hotel, Gwanghwamun
‼️ Entry Tickets: $800 (early bird)
- Early bird: 1st Sept ~ 1st Oct
[CFP & CFT is opened]
CFP - until 15th Oct
CFT - until 31st July
Send us your bio & abstract to "pocadm at gmail"
⏰Date: 2-3rd November, 2023
🇰🇷Venue: Four Seasons Hotel, Gwanghwamun
‼️ Entry Tickets: $800 (early bird)
- Early bird: 1st Sept ~ 1st Oct
[CFP & CFT is opened]
CFP - until 15th Oct
CFT - until 31st July
Send us your bio & abstract to "pocadm at gmail"
Thank you @dfsec_com and @TrenchantARC for amazing parties
Had a massive pleasure time!
Look forward to have you all in Korea next time :)
Had a massive pleasure time!
Look forward to have you all in Korea next time :)




Congratulations on your another successful @offensive_con conference!
Huge thanks to @LukasHermannBFS
@yubiguel Always stays on top-notch management, warm welcomed hospitality, great old/new people and new opportunities!
See you all in MOSEC2023 and POC2023!
Huge thanks to @LukasHermannBFS
@yubiguel Always stays on top-notch management, warm welcomed hospitality, great old/new people and new opportunities!
See you all in MOSEC2023 and POC2023!




OFF TO BERLIN TOMORROW
MEET US AT #OFFENSIVECON👊
MEET US AT #OFFENSIVECON👊
[Zer0Con2023] Donation
We are pleased to congrat Maddie Stone(@maddiestone) for donating her honorarium to the charity!
She has shaped so many lives with her act of charity.
Full of appreciation for you!
We are pleased to congrat Maddie Stone(@maddiestone) for donating her honorarium to the charity!
She has shaped so many lives with her act of charity.
Full of appreciation for you!
[Zer0con2023]
Last talk of Zer0con2023🙏🏻
Valentina Palmiotti(@chompie1337) giving her talk on “SPNEGO for Windows Authentication - A Ubiquitous Attack Surface with No Vulnerabilities?”
#Zer0con2023
Last talk of Zer0con2023🙏🏻
Valentina Palmiotti(@chompie1337) giving her talk on “SPNEGO for Windows Authentication - A Ubiquitous Attack Surface with No Vulnerabilities?”
#Zer0con2023


[Zer0con2023]
Bugs in JS and V8
Gengming Liu(@dmxcsnsbh) & Zhutian Feng(@FengPolaris) giving their talk on Find and exploit race condition bugs in modern JS engines
#Zer0con2023
Bugs in JS and V8
Gengming Liu(@dmxcsnsbh) & Zhutian Feng(@FengPolaris) giving their talk on Find and exploit race condition bugs in modern JS engines
#Zer0con2023


[Zer0con2023]
Great Samsung talk from Hao Xiong(@t1n_mar) & Qinming Dai(@zraxxdd) - “Fuzzing Samsung’s closed-source libraries as if on a real device”
#Zer0con2023
Great Samsung talk from Hao Xiong(@t1n_mar) & Qinming Dai(@zraxxdd) - “Fuzzing Samsung’s closed-source libraries as if on a real device”
#Zer0con2023

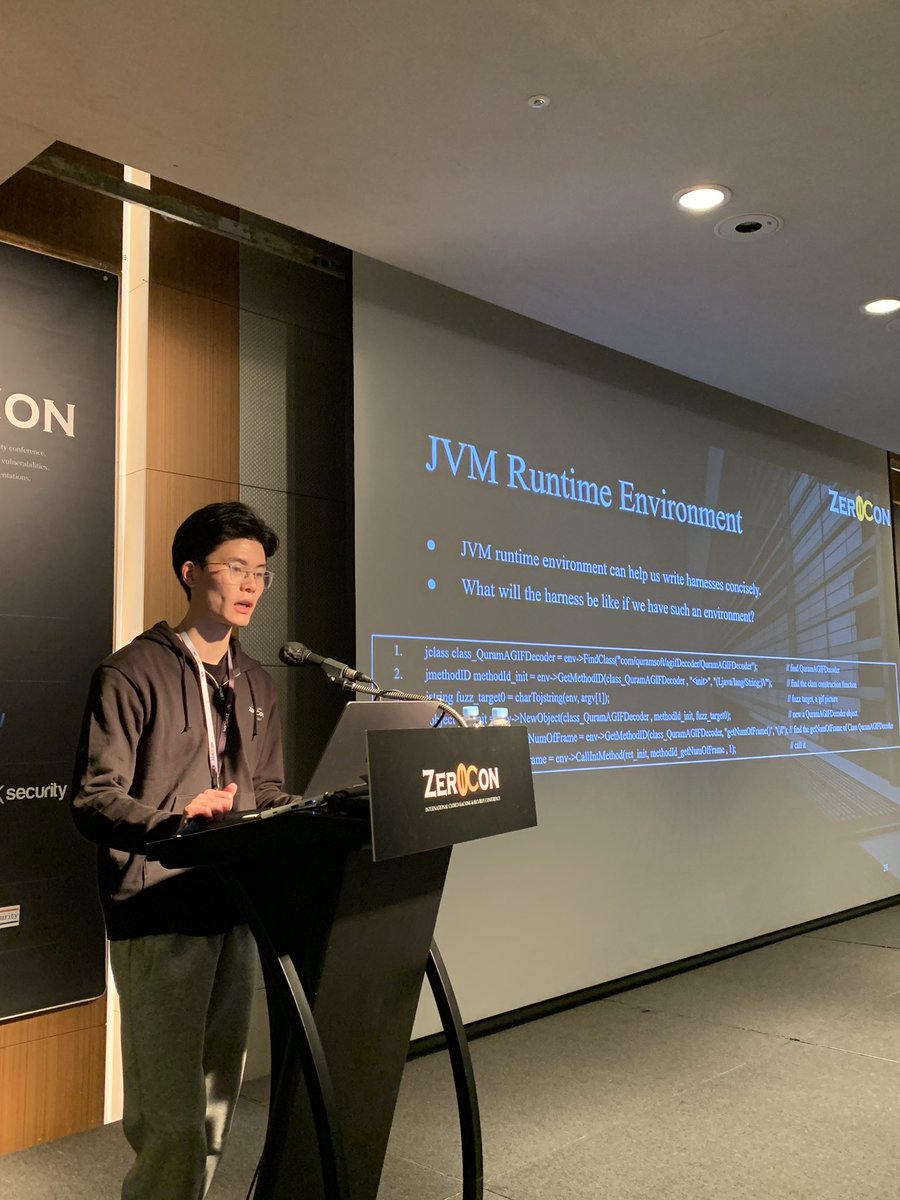
[Zer0con2023]
Last day kicks off with Maddie Stone(@maddiestone) - “A year in review of 0days exploited in the wild in 2022”
#Zer0con2023
Last day kicks off with Maddie Stone(@maddiestone) - “A year in review of 0days exploited in the wild in 2022”
#Zer0con2023

[Zer0con2023]
Last speaker of the 1st day
Amat Cama(@amatcama) - ASN1 and Done : A journey of exploiting ASN.1 parsers in the baseband
#Zer0con2023
Last speaker of the 1st day
Amat Cama(@amatcama) - ASN1 and Done : A journey of exploiting ASN.1 parsers in the baseband
#Zer0con2023


[Zer0con2023]
Sina Karvandi(@Intel80x86) rocks on “chasing bugs with/in Hypervisor”
#Zer0con2023
Sina Karvandi(@Intel80x86) rocks on “chasing bugs with/in Hypervisor”
#Zer0con2023

[Zer0con2023]
Jun Luo(De4dcr0w) & Yanfeng Wang giving their talk on Busy2Nice : A New Way to Win the Race for Tiny Windows in the Linux
#Zer0con2023
Jun Luo(De4dcr0w) & Yanfeng Wang giving their talk on Busy2Nice : A New Way to Win the Race for Tiny Windows in the Linux
#Zer0con2023
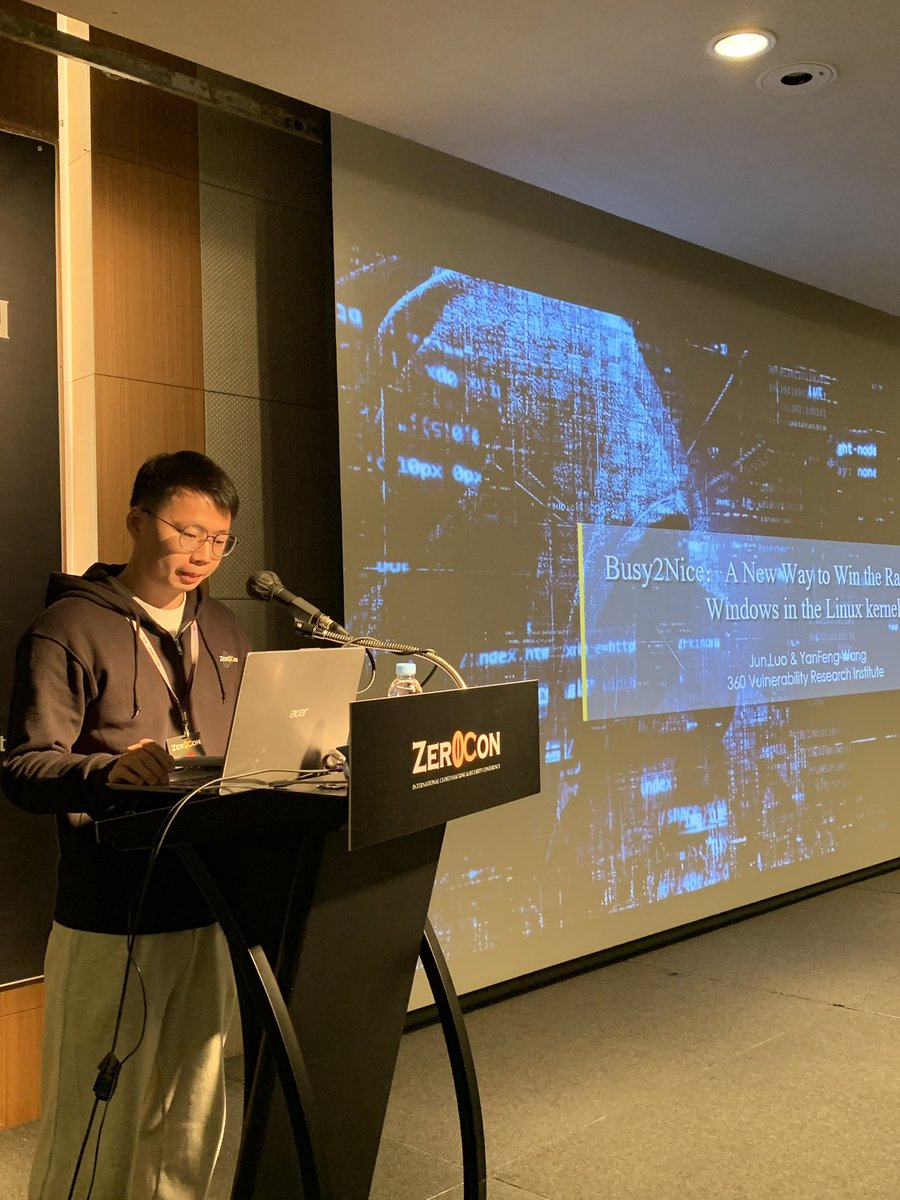

[Zer0con2023]
Thomas Corley(@Fire30_) giving out his talk on “Generic Exploitation of three Android GPU Kernel Driver Vulnerabilties” with demos
#Zer0Con2023
Thomas Corley(@Fire30_) giving out his talk on “Generic Exploitation of three Android GPU Kernel Driver Vulnerabilties” with demos
#Zer0Con2023


[Zer0con2023]
Fully packed feat. Mobile exploitation - the past, present and the future
#Zer0con2023
Fully packed feat. Mobile exploitation - the past, present and the future
#Zer0con2023

[Zer0con2023]
The day kicks off with Jinwook, the organizer giving out the opening speech
#Zer0con2023
The day kicks off with Jinwook, the organizer giving out the opening speech
#Zer0con2023

[Zer0con2023]
It is on!
Starting off with opening keynote from Externalist(@Externalist)🤟
#Zer0con2023
It is on!
Starting off with opening keynote from Externalist(@Externalist)🤟
#Zer0con2023

It is happening!
#Zer0con2023
#Zer0con2023

D-2
#Zer0con2023
#Zer0con2023
[Zer0Con2023] "Gold Sponsor"
Thanks to BlueFrost Security(@bluefrostsec) for Sponsoring the Gold!
BlueFrost Security, organizers of @offensive_con)
is a research-driven cyber security company focusing on vulnerability research and they are hiring!
#Zer0Con2023
Thanks to BlueFrost Security(@bluefrostsec) for Sponsoring the Gold!
BlueFrost Security, organizers of @offensive_con)
is a research-driven cyber security company focusing on vulnerability research and they are hiring!
#Zer0Con2023
[Zer0Con2033] Training is on!
More to be updated soon!
#Zer0con2023
More to be updated soon!
#Zer0con2023
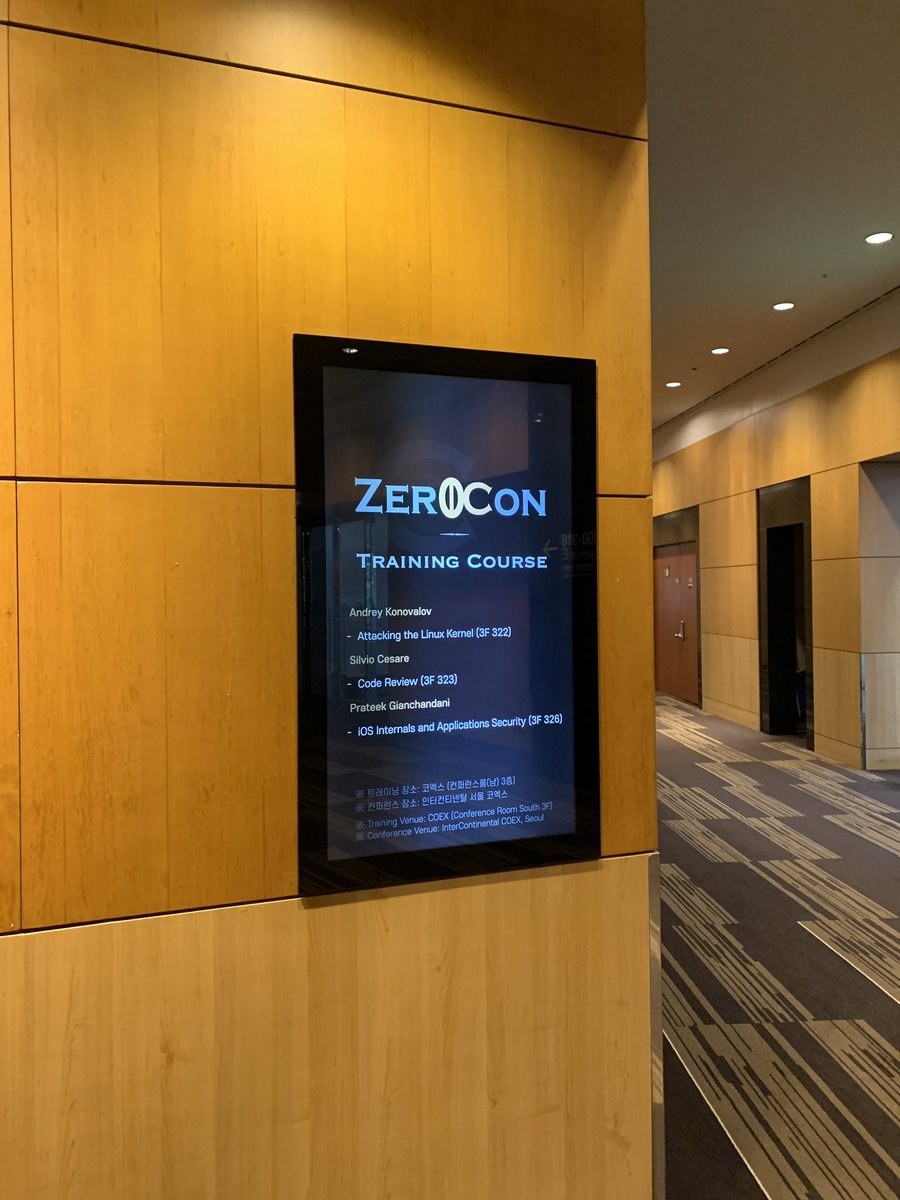
[Zer0Con2023] "Silver Sponsor"
Thanks to Secfence(@secfence) for sponsoring the "Silver"
Secfence is an Offensive Security company specialising in vulnerability research & turnkey platforms.
#Zer0Con2023
Thanks to Secfence(@secfence) for sponsoring the "Silver"
Secfence is an Offensive Security company specialising in vulnerability research & turnkey platforms.
#Zer0Con2023
[Zer0Con2023] Registration
Registration ends in 5 days!
Deadline: 5th April
If you have not registered yet, make it quick!
It's almost reached the limit
#Zer0Con2023
Registration ends in 5 days!
Deadline: 5th April
If you have not registered yet, make it quick!
It's almost reached the limit
#Zer0Con2023

[Zer0Con2023] "Gold Sponsor"
Thanks to PK Security(@pksecurity_io) for sponsoring the "Gold" 👊
PKSecurity is an offensive research company focusing on OS and Application vulnerability research.
#Zer0Con2023
Thanks to PK Security(@pksecurity_io) for sponsoring the "Gold" 👊
PKSecurity is an offensive research company focusing on OS and Application vulnerability research.
#Zer0Con2023
[Zer0con2023] Speaker Update
Jun Luo(De4dcr0w) & Yanfeng Wang - Busy2Nice : A New Way to Win the Race for Tiny Windows in the Linux
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
Jun Luo(De4dcr0w) & Yanfeng Wang - Busy2Nice : A New Way to Win the Race for Tiny Windows in the Linux
‼️Debut stage for the first time in S.Korea
#Zer0Con2023

[Zer0Con2023] "Gold Sponsor"
Thanks to Corellium(@CorelliumHQ) for sponsoring the "Gold" 👊
Virtual Arm-based devices with real-world accuracy. We ensure that developers and engineers are well-equipped to research, work, and test Arm-based technologies.
#Zer0Con2023
Thanks to Corellium(@CorelliumHQ) for sponsoring the "Gold" 👊
Virtual Arm-based devices with real-world accuracy. We ensure that developers and engineers are well-equipped to research, work, and test Arm-based technologies.
#Zer0Con2023
[Zer0con2023] Speaker Update
Nikita Tarakanov(@NikitaTarakanov) & Arsenii Kostromin(@0x3C3E) - DEP/NX, ASLR, SMEP/PXN, SMAP/PAN, CFG/XFG/PAC, CET... Security technology/mitigation A, B, C. Secure SDLC!
Aga, hold my beer bro...
#Zer0Con2023
Nikita Tarakanov(@NikitaTarakanov) & Arsenii Kostromin(@0x3C3E) - DEP/NX, ASLR, SMEP/PXN, SMAP/PAN, CFG/XFG/PAC, CET... Security technology/mitigation A, B, C. Secure SDLC!
Aga, hold my beer bro...
#Zer0Con2023

[Zer0con2023] Speaker Update
Gengming Liu(@dmxcsnsbh) & Zhutian Feng(@FengPolaris) - Find and exploit race condition bugs in modern JS engines
#Zer0Con2023
Gengming Liu(@dmxcsnsbh) & Zhutian Feng(@FengPolaris) - Find and exploit race condition bugs in modern JS engines
#Zer0Con2023

[Zer0con2023] Speaker Update
Amat Cama(@amatcama) - ASN.1 and Done: A journey of exploiting ASN.1 parsers in the baseband
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
Amat Cama(@amatcama) - ASN.1 and Done: A journey of exploiting ASN.1 parsers in the baseband
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
[Zer0con2023] Speaker Update
Hao Xiong & Qinming Dai - Fuzzing Samsung's closed-source libraries as if on a real device
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
Hao Xiong & Qinming Dai - Fuzzing Samsung's closed-source libraries as if on a real device
‼️Debut stage for the first time in S.Korea
#Zer0Con2023

[Zer0con2023] Speaker Update
Sina Karvandi(@Intel80x86) - Chasing Bugs With/In Hypervisors
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
Sina Karvandi(@Intel80x86) - Chasing Bugs With/In Hypervisors
‼️Debut stage for the first time in S.Korea
#Zer0Con2023

[Zer0Con2023] Diamond Sponsor
Huge thanks to Dataflow Security(@dfsec_com) for sponsoring the "Diamond"
Biggest partner - sponsoring third time in a row 🫶
#Zer0Con2023
Huge thanks to Dataflow Security(@dfsec_com) for sponsoring the "Diamond"
Biggest partner - sponsoring third time in a row 🫶
#Zer0Con2023
[Zer0con2023] Keynote Speaker Update
Ki Chan Ahn(@Externalist) - Mobile Exploitation - The past, present, and the future
#Zer0Con2023
Ki Chan Ahn(@Externalist) - Mobile Exploitation - The past, present, and the future
#Zer0Con2023
[Zer0con2023] Speaker Update
Maddie Stone(@maddiestone) - A Year in Review of 0-days Exploited in-the-wild in 2022
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
Maddie Stone(@maddiestone) - A Year in Review of 0-days Exploited in-the-wild in 2022
‼️Debut stage for the first time in S.Korea
#Zer0Con2023

[Zer0con2023] Speaker Update
Valentina Palmiotti(@chompie1337) - SPNEGO for Windows Authentication - A Ubiquitous Attack Surface with No Vulnerabilities?
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
Valentina Palmiotti(@chompie1337) - SPNEGO for Windows Authentication - A Ubiquitous Attack Surface with No Vulnerabilities?
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
[Zer0con2023] Speaker Update
Thomas Corley - Generic Exploitation of Three Android GPU Kernel Driver Vulnerabilities
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
Thomas Corley - Generic Exploitation of Three Android GPU Kernel Driver Vulnerabilities
‼️Debut stage for the first time in S.Korea
#Zer0Con2023
[Zer0con2023 Training] - Registration date extended!
Registration deadline: 16th March 2023
link: https://t.co/6cUC0ODFXm
#Zer0con2023
Registration deadline: 16th March 2023
link: https://t.co/6cUC0ODFXm
#Zer0con2023

[Zer0Con2023] - Speakers updated
Please find more details at https://t.co/9wFYy2zQEq
More speakers will be updated soon
#Zer0con2023
Please find more details at https://t.co/9wFYy2zQEq
More speakers will be updated soon
#Zer0con2023
[Zer0Con2023 Training] - "On-Spot, 3days course"
Cristofaro Mune(@pulsoid) & Niek Timmers(@tieknimmers),
"TEEPwn: Breaking TEE bY Experience"
Register: https://t.co/p2cDduqQuS
#Zer0con2023
Cristofaro Mune(@pulsoid) & Niek Timmers(@tieknimmers),
"TEEPwn: Breaking TEE bY Experience"
Register: https://t.co/p2cDduqQuS
#Zer0con2023

[Zer0Con2023 Training] - "On-Spot, 3days course"
Prateek(@prateekg147) & Dinesh(@Din3zh),
"iOS Internals and Application Security"
Register: https://t.co/p2cDduqQuS
#Zer0con2023
Prateek(@prateekg147) & Dinesh(@Din3zh),
"iOS Internals and Application Security"
Register: https://t.co/p2cDduqQuS
#Zer0con2023


[Zer0Con2023 Training] - "On-Spot, 4days course"
Andrey Konovalov(@andreyknvl), "Attacking the Linux Kernel - Advanced"
Register: https://t.co/p2cDduqQuS
#Zer0con2023
Andrey Konovalov(@andreyknvl), "Attacking the Linux Kernel - Advanced"
Register: https://t.co/p2cDduqQuS
#Zer0con2023
[Zer0Con2023 Training] - "VIRTUAL, 2days course"
Dawid Czagan(@dawidczagan), "Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation
Register: https://t.co/p2cDduqQuS
#Zer0con2023
Dawid Czagan(@dawidczagan), "Black Belt Pentesting / Bug Hunting Millionaire: Mastering Web Attacks with Full-Stack Exploitation
Register: https://t.co/p2cDduqQuS
#Zer0con2023

[Zer0Con2023 Training] - "On-Spot, 4days course"
Silvio Cesare(@silviocesare), "Code Review"
Register: https://t.co/p2cDduqQuS
#Zer0Con2023
Silvio Cesare(@silviocesare), "Code Review"
Register: https://t.co/p2cDduqQuS
#Zer0Con2023

[Zer0Con2023]
- Date changed to "13th ~ 14th April"
- "NEW" Venue: InterContinental Seoul COEX (finally)
This year will be huge!
If you have not submitted CFP, please do so
#Zer0Con2023
- Date changed to "13th ~ 14th April"
- "NEW" Venue: InterContinental Seoul COEX (finally)
This year will be huge!
If you have not submitted CFP, please do so
#Zer0Con2023
Coming up next,
Zer0Con2023 trainings will be up soon
Stay tuned!
#Zer0Con2023
Zer0Con2023 trainings will be up soon
Stay tuned!
#Zer0Con2023
Upcoming, #Zer0Con2023 on April
If you are interested in speaking at Zer0Con2023,
Details are at: https://t.co/61Vh1ldHfk
Look forward to your huge interests 🫶
If you are interested in speaking at Zer0Con2023,
Details are at: https://t.co/61Vh1ldHfk
Look forward to your huge interests 🫶
🇰🇷🇰🇷🇰🇷🇰🇷🇰🇷
round of 16!!!
Go Korea!
round of 16!!!
Go Korea!
OK. We have the winner of the drinkin hell…🤣🤣
Time for some drinkin hell!!
Thank you all🤟🙏🏻
#POC2022
#POC2022

[POC2022]
Last talk of the #POC2022!!!
Man Yue Mo(@mmolgtm), "Controlled chaos: Predicting object addresses in Chrome (without breaking a sweat)"
Last talk of the #POC2022!!!
Man Yue Mo(@mmolgtm), "Controlled chaos: Predicting object addresses in Chrome (without breaking a sweat)"

[POC2022]
Interesting talk on blockchain
Shaked Reiner(@ShakReiner), "RCEing Your Way Into the Blockchain: Uncovering a critical vulnerability and taking over Decentralized Identity (DID) networks"
#POC2022
Interesting talk on blockchain
Shaked Reiner(@ShakReiner), "RCEing Your Way Into the Blockchain: Uncovering a critical vulnerability and taking over Decentralized Identity (DID) networks"
#POC2022


[POC2022]
First time talk! Congrats! Nice debut at #POC2022
Manfred Paul(@_manfp), "Time-Traveling JIT Bugs"
First time talk! Congrats! Nice debut at #POC2022
Manfred Paul(@_manfp), "Time-Traveling JIT Bugs"


[POC2022]
Web app talk is on!
Temel Demir & Ozan Yigen, "-compRCEssed:Compressed File Manipulation @WebApps"
#POC2022
Web app talk is on!
Temel Demir & Ozan Yigen, "-compRCEssed:Compressed File Manipulation @WebApps"
#POC2022


[POC2022]
Half way through! We have Zhenpeng Pan(@Peterpan980927), "The Journey To Hybrid Apple Driver Fuzzing"
#POC2022
Half way through! We have Zhenpeng Pan(@Peterpan980927), "The Journey To Hybrid Apple Driver Fuzzing"
#POC2022


[POC2022]
Bien Pham(@bienpnn) & Howard Nguyen(@ngtrh1eu), in-depth talk on "Exploiting cross table object reference in Linux Netfilter table module"
#POC2022
Bien Pham(@bienpnn) & Howard Nguyen(@ngtrh1eu), in-depth talk on "Exploiting cross table object reference in Linux Netfilter table module"
#POC2022


[POC2022]
The Fugu 15 exploitation!
Linus Henze(@LinusHenze) giving a talk about “Fugu15 - A deep dive into iOS 15 exploitation”
#POC2022
The Fugu 15 exploitation!
Linus Henze(@LinusHenze) giving a talk about “Fugu15 - A deep dive into iOS 15 exploitation”
#POC2022


[POC2022]
On the other side of the conf. room, we have Mickey Jin(@patch1t), "Package Disaster: Diving Deep into macOS PackageKit and Discovering 15+ New SIP-Bypass Vulnerabilities"
#POC2022
On the other side of the conf. room, we have Mickey Jin(@patch1t), "Package Disaster: Diving Deep into macOS PackageKit and Discovering 15+ New SIP-Bypass Vulnerabilities"
#POC2022


[POC2022]
G’day folks! 2nd day just started
Sergey Toshin(@_bagipro), Brightening the opening with “Discovering vendor-specific vulnerabilities in Android"
#POC2022
G’day folks! 2nd day just started
Sergey Toshin(@_bagipro), Brightening the opening with “Discovering vendor-specific vulnerabilities in Android"
#POC2022


[POC2022]
Last talk of the day(Track B)😎
Qian Chen(@cq674350529), "MikroTik RouterOS Security: The Forgotten IPC Message
#POC2022
Last talk of the day(Track B)😎
Qian Chen(@cq674350529), "MikroTik RouterOS Security: The Forgotten IPC Message
#POC2022


[POC2022]
Last talk of the day😎
Dr.Shinjo Park(@ad_ili_rai_en) & Dr.Altaf Shaik, “API wars in 5G networks”
#POC2022
Last talk of the day😎
Dr.Shinjo Park(@ad_ili_rai_en) & Dr.Altaf Shaik, “API wars in 5G networks”
#POC2022

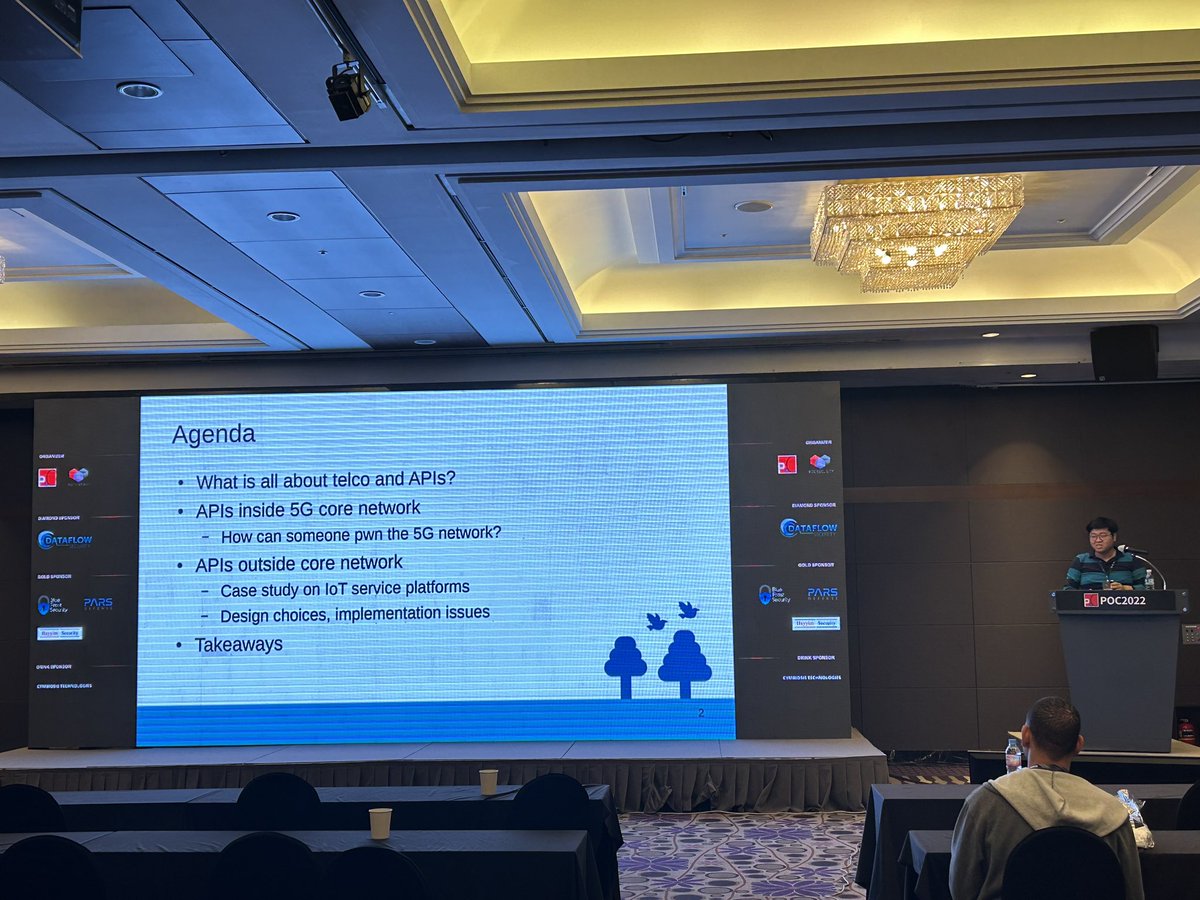
[POC2022]
Chen Nan, Chongyang Bao, Jiaming Tao are presenting about "Explore ’BUS’ Mysteries via Automotive fuzzing"
#POC2022
Chen Nan, Chongyang Bao, Jiaming Tao are presenting about "Explore ’BUS’ Mysteries via Automotive fuzzing"
#POC2022
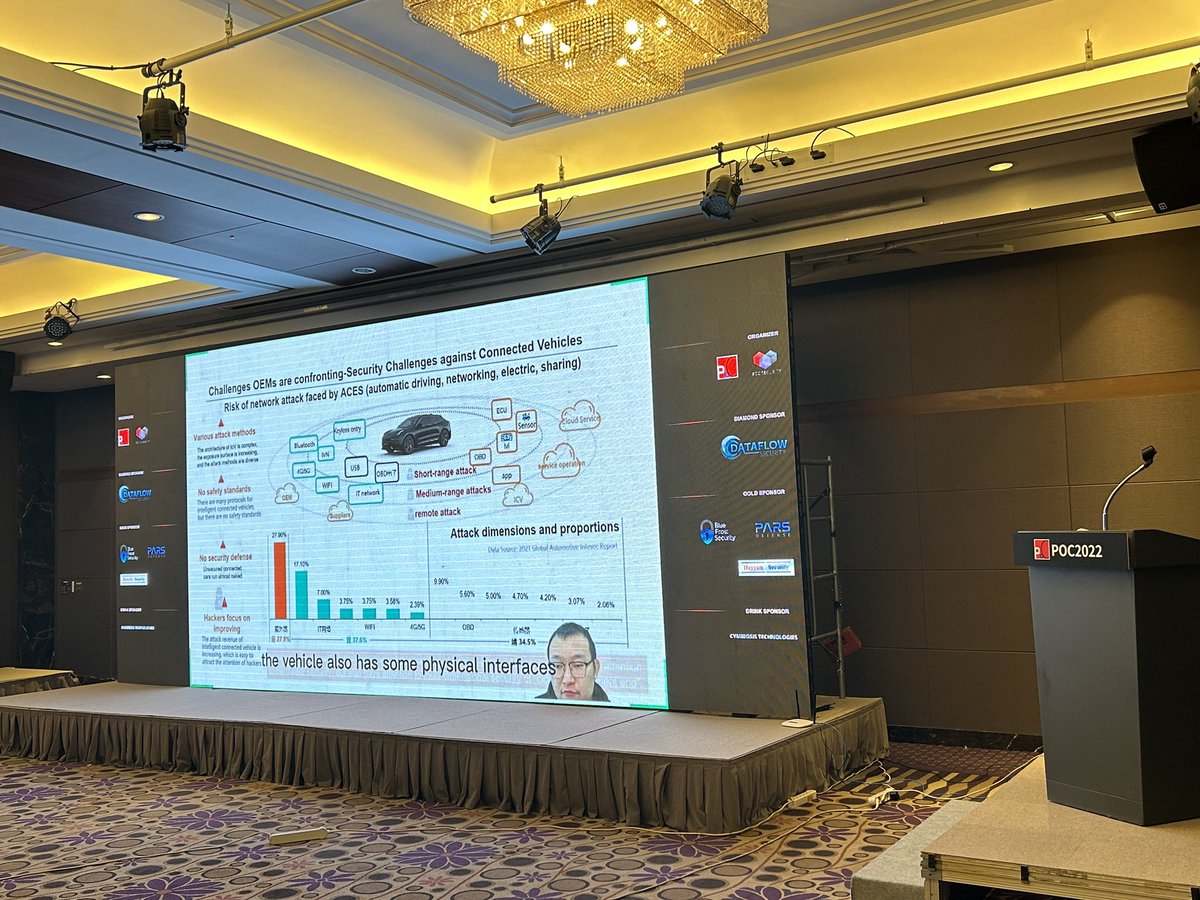

[POC2022]
ChangSeon Lee(@crattack), giving us a talk about “Blockchain events and accidents”
#POC2022
ChangSeon Lee(@crattack), giving us a talk about “Blockchain events and accidents”
#POC2022
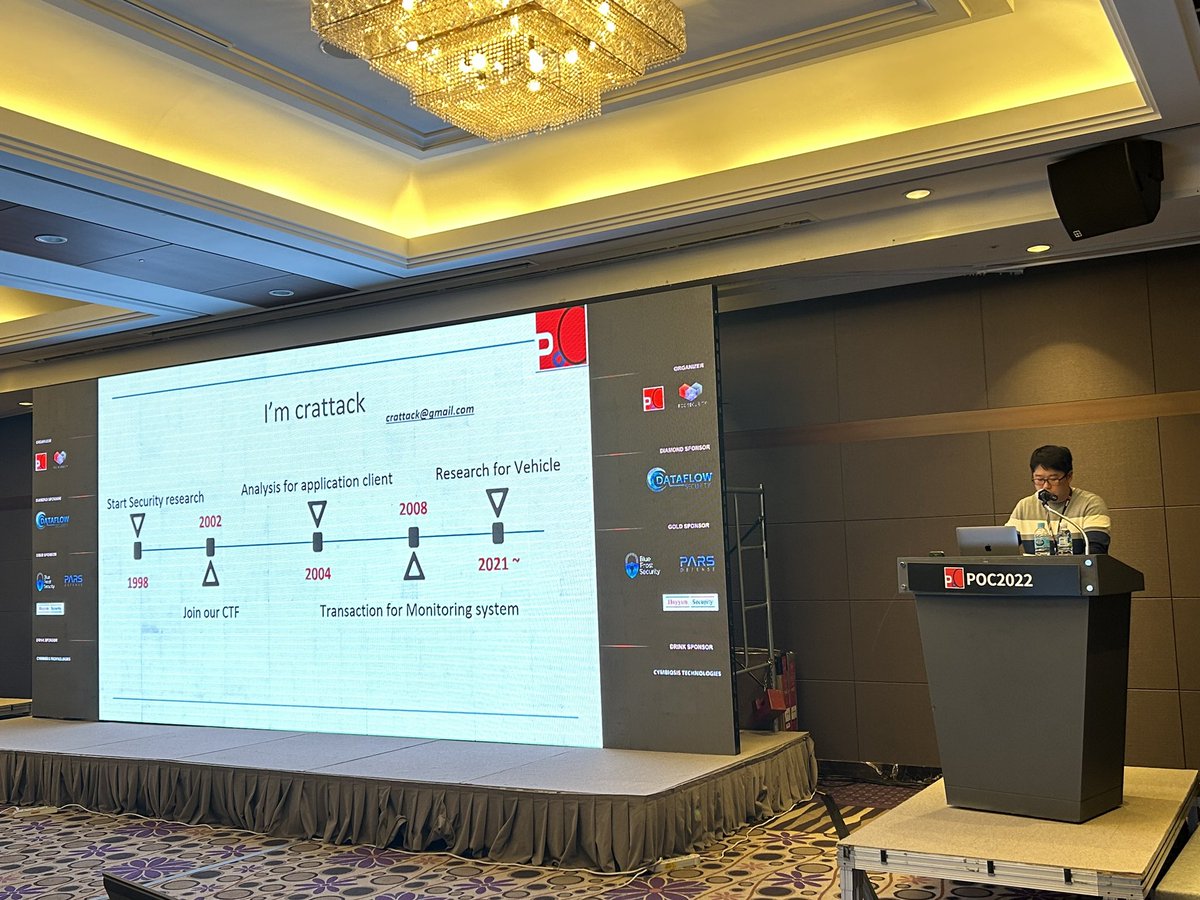
[POC2022]
Pwning.eth(@PwningEth), fully veiled:)
Giving us a talk about “"Rainbow Bridge to the Aurora"
#POC2022
Pwning.eth(@PwningEth), fully veiled:)
Giving us a talk about “"Rainbow Bridge to the Aurora"
#POC2022


[POC2022]
Nguyễn Hoàng Thạch(@hi_im_d4rkn3ss), giving the talk about "How to Backup and Pwn using Time Machine"
#POC2022
Nguyễn Hoàng Thạch(@hi_im_d4rkn3ss), giving the talk about "How to Backup and Pwn using Time Machine"
#POC2022


[POC2022]
Zhanglin He & Royce Lu, interesting talk has been started “DiDe - Build a pattern-based detection module from scratch”
#POC2022
Zhanglin He & Royce Lu, interesting talk has been started “DiDe - Build a pattern-based detection module from scratch”
#POC2022


[POC2022]
We are moving, we have Hector Peralta(@Hperalta89), talking about “Expanding attack surface to bypass security in Electron framework”
#POC2022
We are moving, we have Hector Peralta(@Hperalta89), talking about “Expanding attack surface to bypass security in Electron framework”
#POC2022


[POC2022]
Xuefeng Li & Dr.Zhiniang Peng(@edwardzpeng), giving us a talk about “Exploiting errors in Windows error reporting service in 2022”
#POC2022
Xuefeng Li & Dr.Zhiniang Peng(@edwardzpeng), giving us a talk about “Exploiting errors in Windows error reporting service in 2022”
#POC2022


[POC2022]
@_simo36 giving us a talk regarding “Apple’s Neural Engine” how vulnerable it was to attack
#POC2022
@_simo36 giving us a talk regarding “Apple’s Neural Engine” how vulnerable it was to attack
#POC2022


[POC2022]
Ivan Fratric(@ifsecure), giving us more updates and adventures on “Zoom and XMPP application hacking”
#POC2022
Ivan Fratric(@ifsecure), giving us more updates and adventures on “Zoom and XMPP application hacking”
#POC2022



[POC2022]
Matt Suiche(@msuiche), opening the the atmosphere at #POC2022
Giving us a keynote on “how unsafe() is Rust?”
Matt Suiche(@msuiche), opening the the atmosphere at #POC2022
Giving us a keynote on “how unsafe() is Rust?”



[POC2022]
@rootack making welcome remarks
We’re on!
#POC2022
@rootack making welcome remarks
We’re on!
#POC2022



[POC2022] D-2
- Casual Korean cuisine ahead tomorrow with speakers, sponsors, VIPs
- Speaker dinner the day after
- “Drinking Hell” on the last day
#POC2022
- Casual Korean cuisine ahead tomorrow with speakers, sponsors, VIPs
- Speaker dinner the day after
- “Drinking Hell” on the last day
#POC2022
[POC2022] Attacking the Linux kernel training is on!
@andreyknvl is making an introduction and starting with full of passion!
#POC2022
@andreyknvl is making an introduction and starting with full of passion!
#POC2022

[POC2022] 4-day course has just started!
@Pat_Ventuzelo is giving a training at POC2022. He marks the start!
Fully packed and we are starting!
#POC2022
@Pat_Ventuzelo is giving a training at POC2022. He marks the start!
Fully packed and we are starting!
#POC2022


[MOSEC2022] is also happening in Shanghai, China!
Jinwook(@rootack), our colleague is greeting security folks remotely!
#MOSEC2022
Jinwook(@rootack), our colleague is greeting security folks remotely!
#MOSEC2022

[POC2022] is just around the corner!
If you have not registered yet, we suggest you get'em quick!
3 days left till registration closes
#POC2022
If you have not registered yet, we suggest you get'em quick!
3 days left till registration closes
#POC2022
[POC2022] Linux training update
Registration date extended.
For those who have not registered yet, hop on quickly.
2 more spots left!
#POC2022
Registration date extended.
For those who have not registered yet, hop on quickly.
2 more spots left!
#POC2022
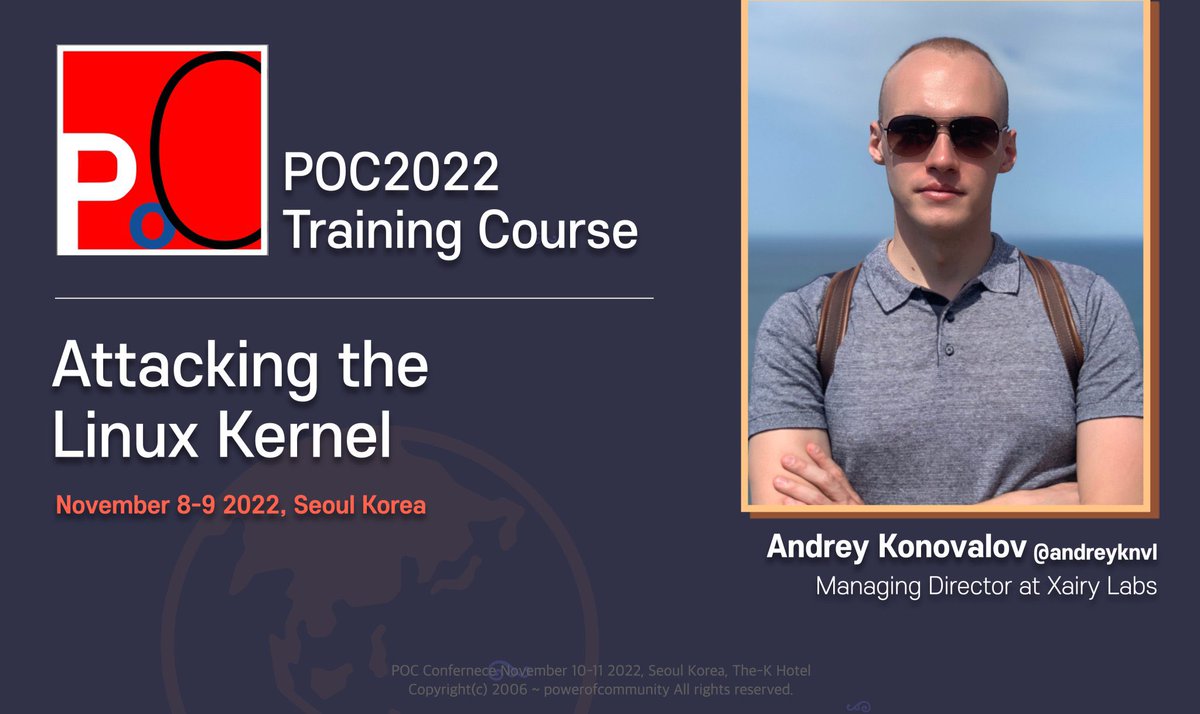
[POC2022] THE FINAL LINE-UP
Proud to announce our final line-up for #POC2022
- 4 more speaker have hop on the ultimate POC bus
- Schedule is out: https://t.co/mkvQJhVgEA
- Registration closes on "4th November"
Proud to announce our final line-up for #POC2022
- 4 more speaker have hop on the ultimate POC bus
- Schedule is out: https://t.co/mkvQJhVgEA
- Registration closes on "4th November"
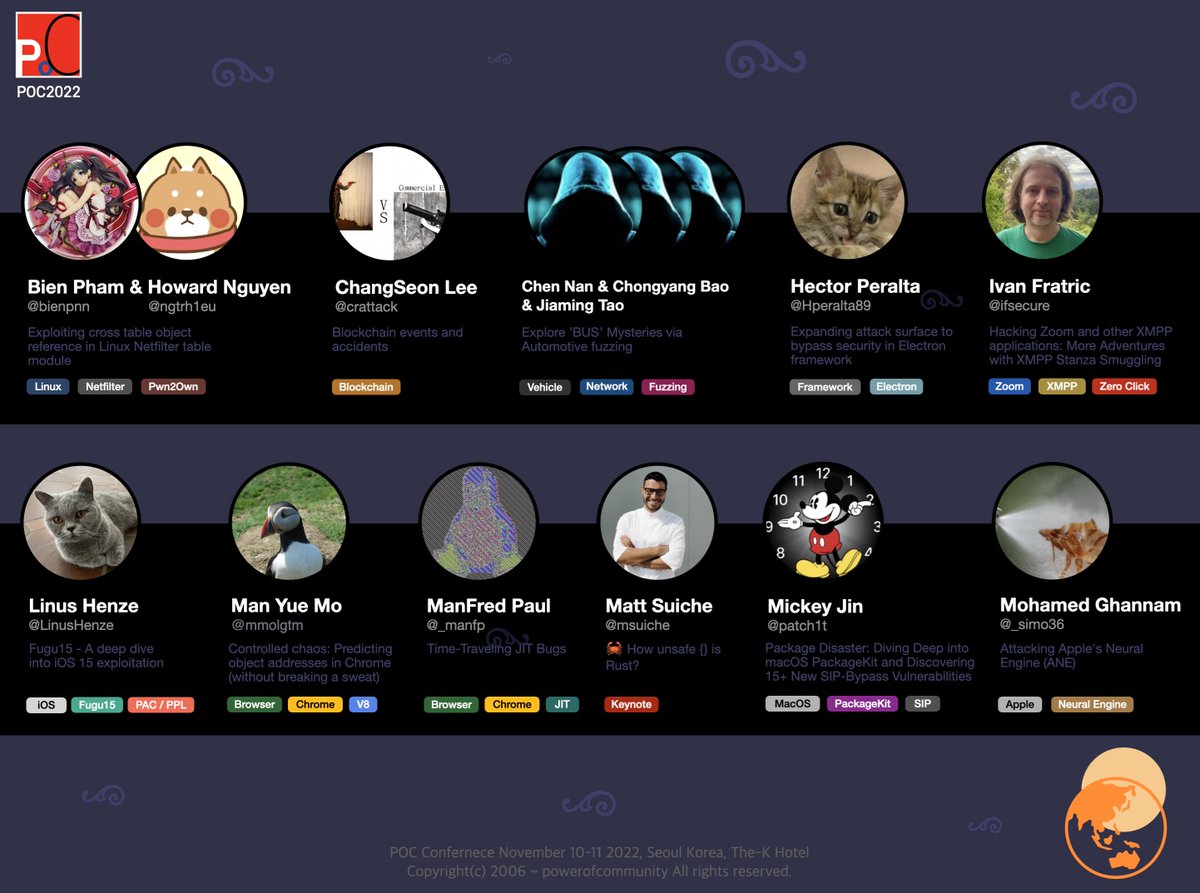
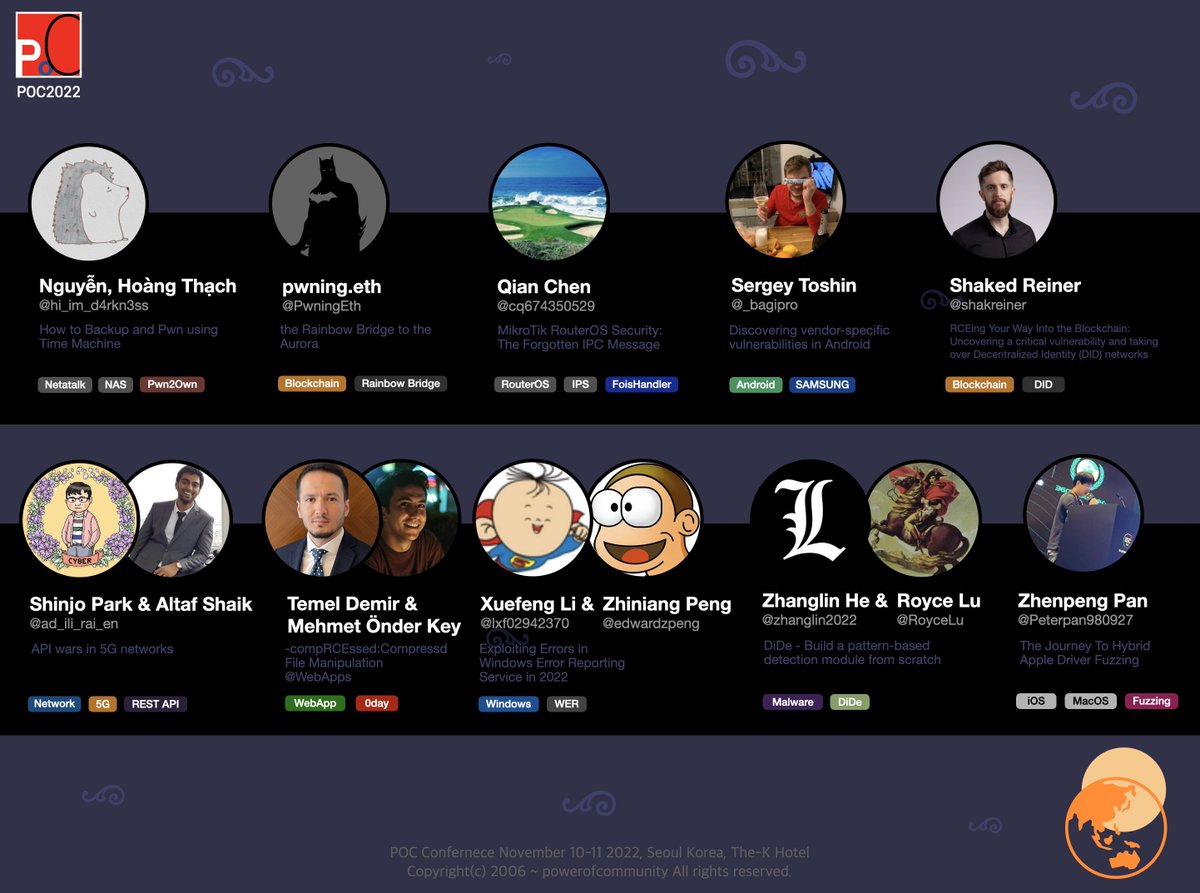
Thanks to Hayyim Security for sponsoring the Gold at #POC2022
One of offensive security companies in S.Korea
Hayyim Security, is a offensive research company focusing on Automatic Exploit Generation(AEG), vulnerability research and they're hiring!
One of offensive security companies in S.Korea
Hayyim Security, is a offensive research company focusing on Automatic Exploit Generation(AEG), vulnerability research and they're hiring!
Thanks to BlueFrost Security(@bluefrostsec) for Sponsoring the Gold at #POC2022
Looking forward to a huge collaboration!
BlueFrost Security, organizers of @offensive_con
is a research-driven cyber security company focusing on vulnerability research and they are hiring!
Looking forward to a huge collaboration!
BlueFrost Security, organizers of @offensive_con
is a research-driven cyber security company focusing on vulnerability research and they are hiring!
Huge thanks to PARS Defense(@ParsDefense) for Sponsoring the Gold at #POC2022!
Come find out what they are offering!
PARS Defense(@parsdefense), is a research company specializes in low level security with a focus on mobile systems and they're hiring.
Come find out what they are offering!
PARS Defense(@parsdefense), is a research company specializes in low level security with a focus on mobile systems and they're hiring.
Only 14 chains are exclusive